Pdf Encryption Using Lester Hill Cipher Algorithm
Hill Cipher Encryption Technique Pdf The objective of this paper is to encrypt an text using a technique different from the conventional hill cipher. the hill cipher utilizes matrix manipulations for symmetric encryption, enhancing security through invertible key matrices. Cryptography is the art or science encompassing the principles and methods of transforming an intelligible message (plaintext) into one that is unintelligible (cipher text) and then retransforming that message back to its original form.
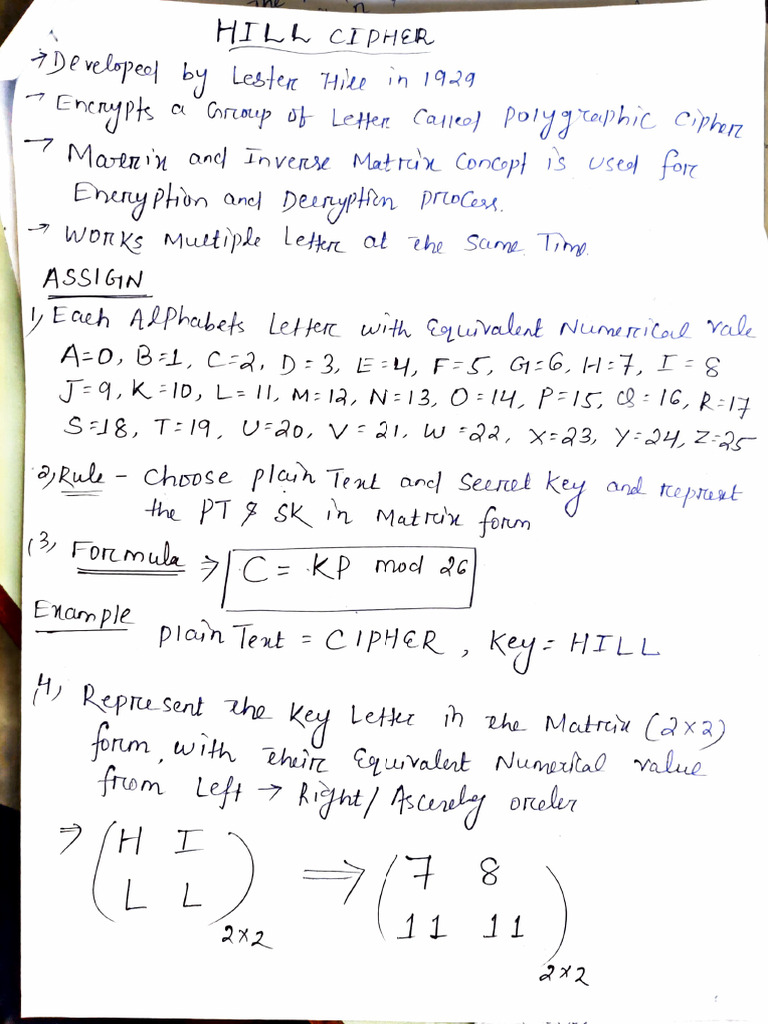
Hill Cipher Pdf Encryption Matrix Mathematics Since the letter frequencies are masked the hill cipher is considerably more difficult to crack than a monoalphabetic substitution that is vulnerable to frequency analysis. Since 1929, many modi cations have been made to the hill cipher in order to improve its security. in this project, we demonstrate how the hill cipher works, implement a 3x3 version of the cipher in matlab, and analyze the cryptographic method. The document discusses the hill cipher algorithm, a symmetric encryption technique that uses matrix manipulations for data encryption and decryption. it introduces an involuntary key matrix method that ensures the key matrix used for encryption is always invertible, thus simplifying decryption. To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.).
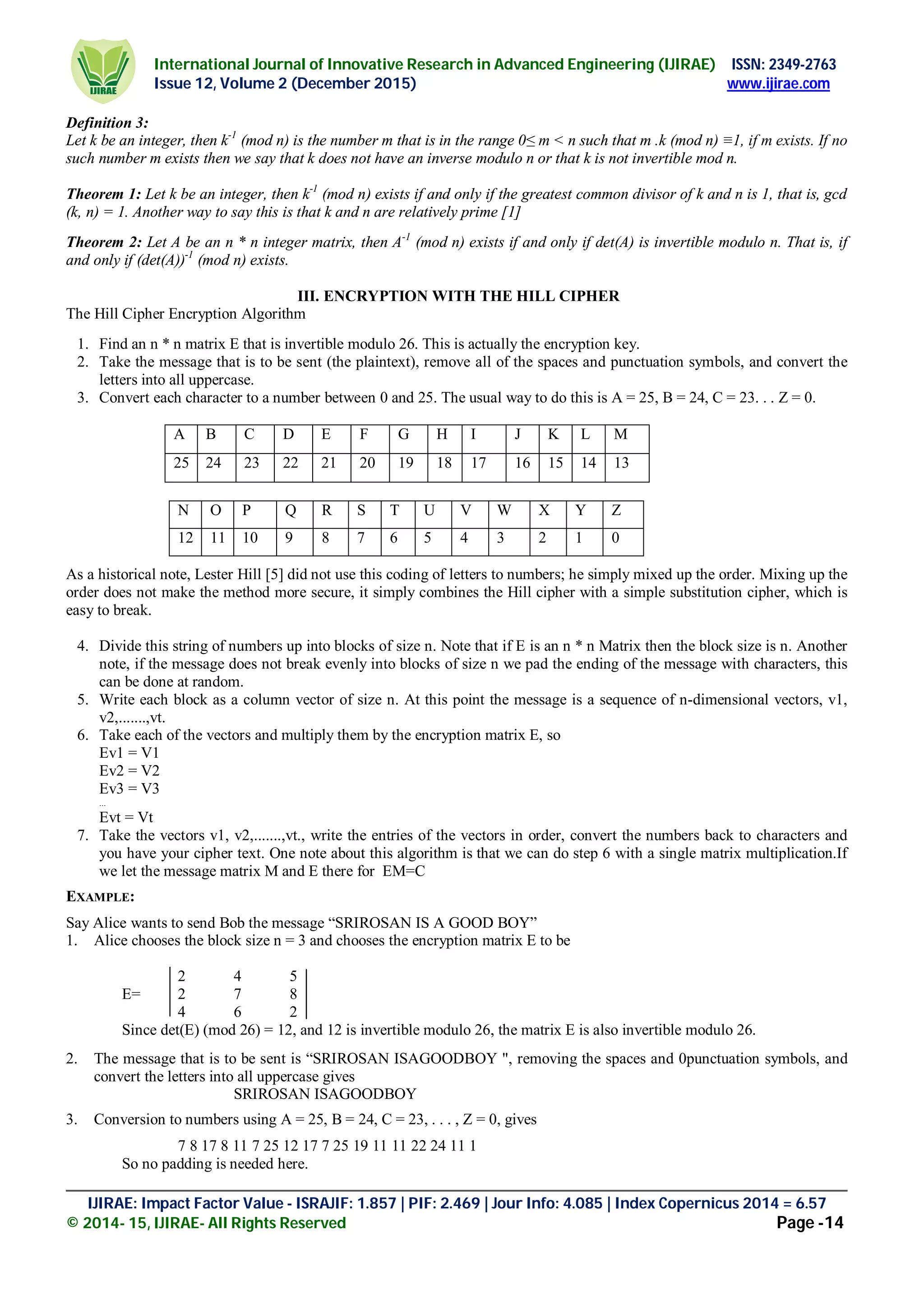
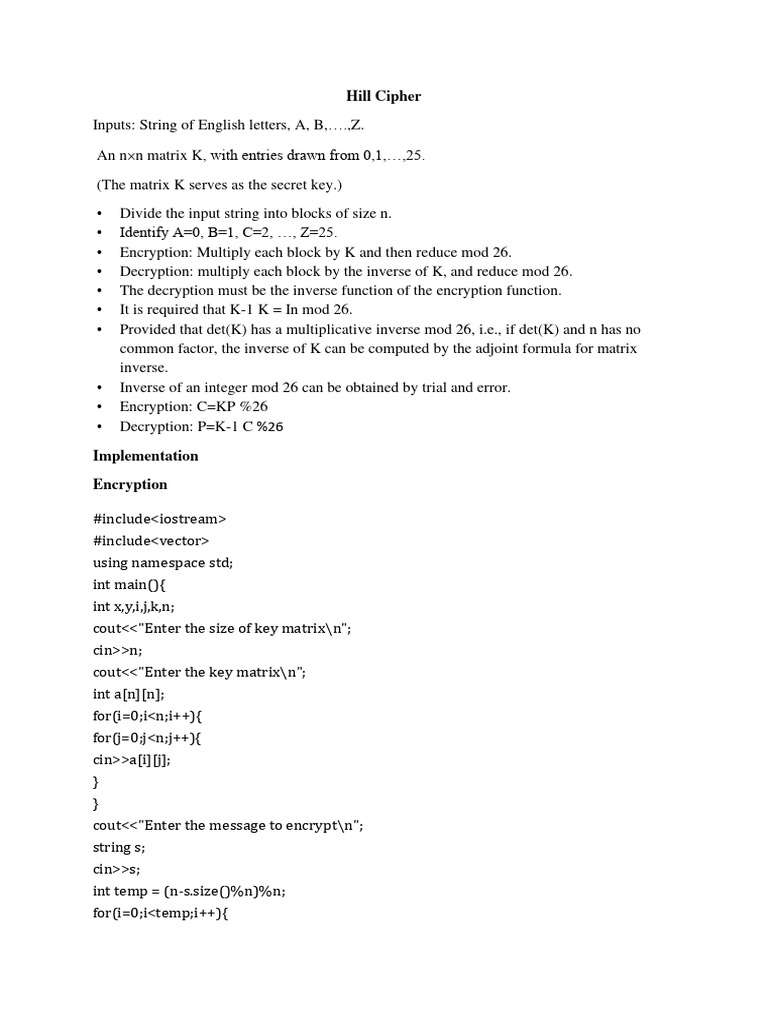
Encryption Using Lester Hill Cipher Algorithm Pdf The document discusses the hill cipher algorithm, a symmetric encryption technique that uses matrix manipulations for data encryption and decryption. it introduces an involuntary key matrix method that ensures the key matrix used for encryption is always invertible, thus simplifying decryption. To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.). To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. Given the focus of this paper on the hill cipher, which is a symmetric encryption algorithm, the following sections will delve deeper into the principles and applications of symmetric encryption. 1.1 substitution ciphers substitution ciphers work by substituting one leter with another. In this work, we present a novel hill cipher security method that utilizes gaussian integers from number theory.

Encryption Algorithm Of Modified Double Guard Hill Cipher Download To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. Given the focus of this paper on the hill cipher, which is a symmetric encryption algorithm, the following sections will delve deeper into the principles and applications of symmetric encryption. 1.1 substitution ciphers substitution ciphers work by substituting one leter with another. In this work, we present a novel hill cipher security method that utilizes gaussian integers from number theory.

Solution Hill Cipher Hill Cipher Encryption And Decryption Des Data 1.1 substitution ciphers substitution ciphers work by substituting one leter with another. In this work, we present a novel hill cipher security method that utilizes gaussian integers from number theory.

Algorithm For Digital Image Encryption Using Multiple Hill Ciphers A
Comments are closed.