Pdf Detection Of Obfuscated Malicious Javascript Code

Pdf Detection Of Obfuscated Malicious Javascript Code This paper proposes an automatic ids of obfuscated javascript that employs several features and machine learning techniques that effectively distinguish malicious and benign javascript codes. This paper proposes an automatic ids of obfuscated javascript that employs several features and machine learning techniques that effectively distinguish malicious and benign javascript.

Pdf Jstill Mostly Static Detection Of Obfuscated Malicious Abstract: websites on the internet are becoming increasingly vulnerable to malicious javascript code because of its strong impact and dramatic effect. numerous recent cyberattacks use javascript vulnerabilities, and in some cases employ obfuscation to conceal their malice and elude detection. Since an obfuscated definition of a user defined function is an indication of obfuscated malicious javascript code, we will discuss how to detect obfuscated function definition in this section. In this paper, we propose a novel malicious javascript detection method that is robust against obfuscation. we dive into the nature of benign and malicious based on the idea of splitting and regrouping. More importantly, it shows that jast does not confound obfuscation with malicious ness, and plain text with benign inputs, but could use differences between benign and malicious obfuscation at a syntactic level to distinguish benign obfuscated from malicious obfuscated files.
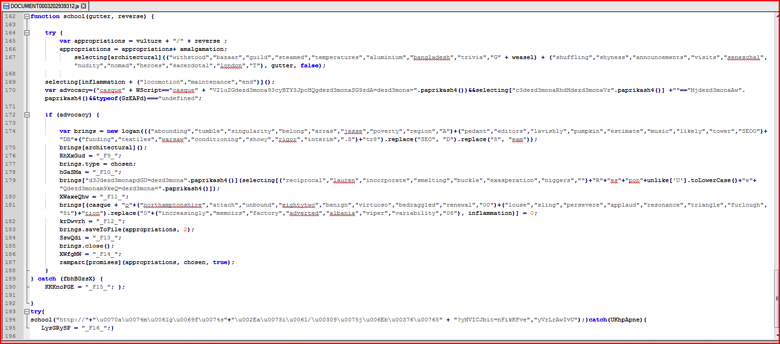
Manually Deobfuscating Strings Obfuscated In Malicious Javascript Code In this paper, we propose a novel malicious javascript detection method that is robust against obfuscation. we dive into the nature of benign and malicious based on the idea of splitting and regrouping. More importantly, it shows that jast does not confound obfuscation with malicious ness, and plain text with benign inputs, but could use differences between benign and malicious obfuscation at a syntactic level to distinguish benign obfuscated from malicious obfuscated files. To defend against obfuscated malicious javascript code, in this paper we propose a mostly static approach called jstill. jstill captures some essential characteristics of obfuscated malicious code by function invocation based analysis. Jast was able to detect 82.31% of the 13,595 malicious web javascript, which shows a certain similarity at the 4 grams level between email javascript and web javascript. In this paper, we present jast, a low overhead solution that combines the extraction of features from the abstract syntax tree with a random forest classifier to detect malicious javascript instances. By using such dynamic behavioral analysis with a low performance overhead, we can effectively detect obfuscated malicious codes as their final malicious behavior remains unchanged.

Grace You On Linkedin Detection Of Obfuscated Malicious Javascript Code To defend against obfuscated malicious javascript code, in this paper we propose a mostly static approach called jstill. jstill captures some essential characteristics of obfuscated malicious code by function invocation based analysis. Jast was able to detect 82.31% of the 13,595 malicious web javascript, which shows a certain similarity at the 4 grams level between email javascript and web javascript. In this paper, we present jast, a low overhead solution that combines the extraction of features from the abstract syntax tree with a random forest classifier to detect malicious javascript instances. By using such dynamic behavioral analysis with a low performance overhead, we can effectively detect obfuscated malicious codes as their final malicious behavior remains unchanged.
Comments are closed.