Pdf Detecting Metamorphic Malware By Using Behavior Based Aggregated

Metamorphic Malware Pdf Malware Computer Virus We have capitalized upon this to create an aggregated signature for a family of malware. creating a signature that spans a malware family allows it to identify known and new variants of that. Abstract: the capability of advanced malware, such as metamorphic malware and polymorphic malware, are quickly outpacing our current abilities to detect their presence.
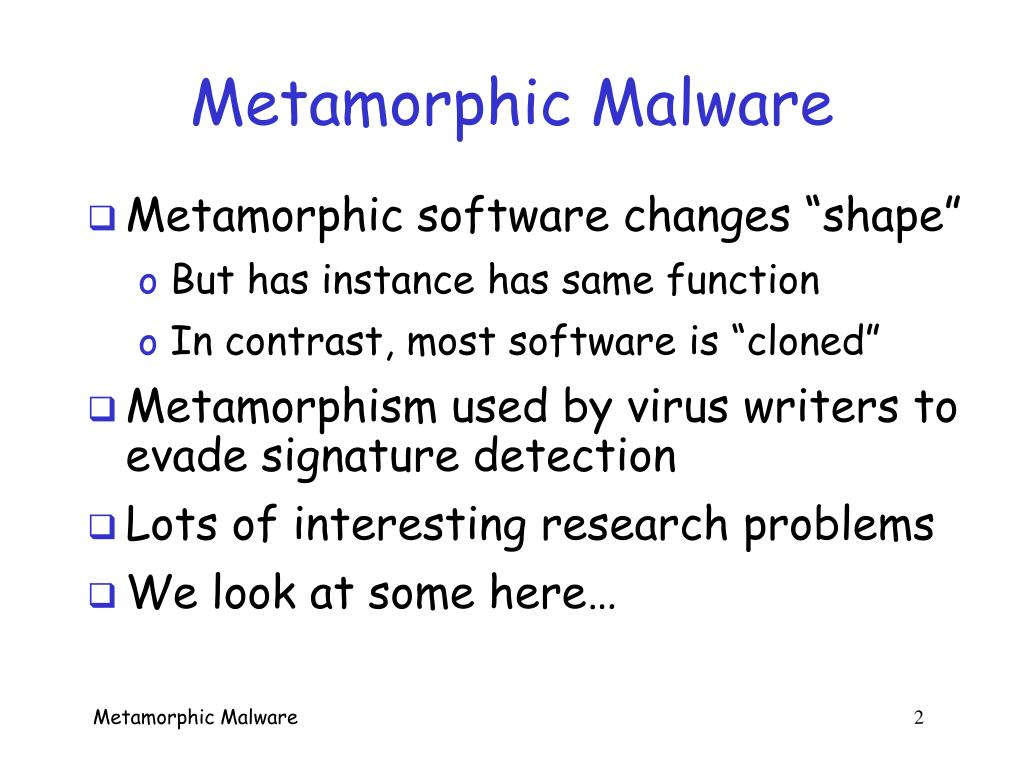
Ppt Metamorphic Malware Research Powerpoint Presentation Free The technique of malware behavior extraction is investigated, the formal malware behavior feature (mbf) extraction method is presented, and the malicious behavior feature based malware detection algorithm is proposed. We have capitalized upon this discovery to create a behavior based aggregate signature for a family of malware. In this paper, we propose malspm, an intelligent malware detection system based on sequential pattern mining (spm) for the analysis and classification of malware behavior during executions. Using an aggregated signature versus many signatures for each variant for detection of malware provides many benefits to anti virus vendors and the community as a whole by reducing the size of the signature database, reducing maintenance, and increasing speed of detection without losing accuracy.

Pdf Malspm Metamorphic Malware Behavior Analysis And Classification In this paper, we propose malspm, an intelligent malware detection system based on sequential pattern mining (spm) for the analysis and classification of malware behavior during executions. Using an aggregated signature versus many signatures for each variant for detection of malware provides many benefits to anti virus vendors and the community as a whole by reducing the size of the signature database, reducing maintenance, and increasing speed of detection without losing accuracy. Malware. in order to address the problem of detecting mutated generations, we propose a method based on opcode graph similar. ty (ogs). ogs tries to detect metamorphic malware using the similarity of opco. While we have techniques to easily detect the older variants using signature based mechanisms and some newer ones using emulators or dfa based techniques, the morphed variants are the most troublesome of all due to their slippery nature. In this section we proposed our methodology to detect metamorphic malware based on behavioural patterns using statistical features of application programming interface (api) calls from executables using similarity measurement to detect and classify even unknown malware. In this study, the focus is on metamorphic malware. an spm based approach is presented for the analysis of api calls sequences made by malware that were run in an isolated secured environment.

How Polymorphic And Metamorphic Malware Evades Detection Malware. in order to address the problem of detecting mutated generations, we propose a method based on opcode graph similar. ty (ogs). ogs tries to detect metamorphic malware using the similarity of opco. While we have techniques to easily detect the older variants using signature based mechanisms and some newer ones using emulators or dfa based techniques, the morphed variants are the most troublesome of all due to their slippery nature. In this section we proposed our methodology to detect metamorphic malware based on behavioural patterns using statistical features of application programming interface (api) calls from executables using similarity measurement to detect and classify even unknown malware. In this study, the focus is on metamorphic malware. an spm based approach is presented for the analysis of api calls sequences made by malware that were run in an isolated secured environment.

Pdf Metamorphic Malware Detection Using Opcode Frequency Rate And In this section we proposed our methodology to detect metamorphic malware based on behavioural patterns using statistical features of application programming interface (api) calls from executables using similarity measurement to detect and classify even unknown malware. In this study, the focus is on metamorphic malware. an spm based approach is presented for the analysis of api calls sequences made by malware that were run in an isolated secured environment.

Bioinformatics Techniques For Metamorphic Malware Analysis And
Comments are closed.