Pdf Cryptography 07 00020

Applsci 07 00020 Pdf 3 D Printing Anisotropy In this research paper, a new method of digital image cryptography is introduced. this method is based on using a color image as an image key to generate a sophisticated matrix private key (mpk. Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus.
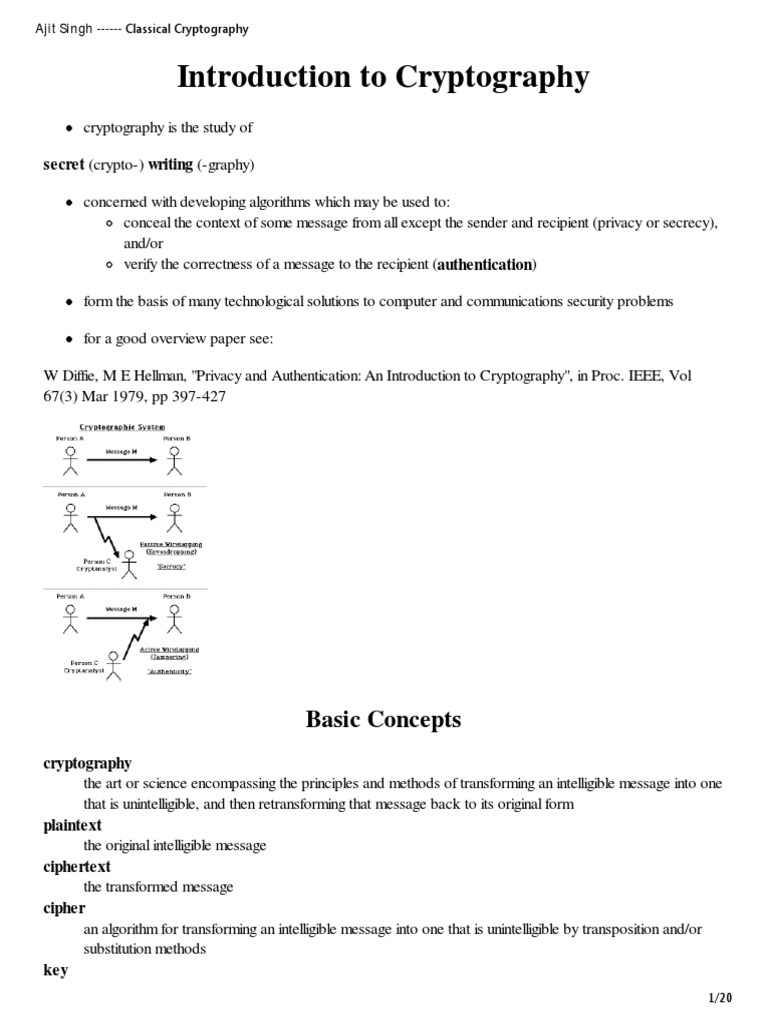
Cryptography 2 Pdf Cryptography Cipher Loading…. With our collection of free pdf books, you can delve into the principles of codes and hashes, learn about public and symmetric key cryptography, and discover innovative techniques used in cybersecurity. For those instructors who wish to give a rapid introduction to modern cryptography, in a 20–30 lecture course, i recommend chapters 3, 7, 8, 10, 11, 14 and 16 with enough of chapter 1 so as to enable the students to understand the following material. Cryptography, a word with greek origins, means “secret writing.” however, we use the term to refer to the science and art of transforming messages to make them secure and immune to attacks.

Cryptography An Open Access Journal From Mdpi Contribute to phanthetoan cryptography i development by creating an account on github. These are scribed notes from a graduate course on cryptography o ered at the university of california, berkeley, in the spring of 2009. the notes have been only minimally edited, and there may be several errors and imprecisions. Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message. The document provides comprehensive study notes on cryptography and security, covering topics from the history and fundamentals of cryptography to modern practices like asymmetric cryptography, digital signatures, and password security.

Downloadпёџ Book Pdf Cryptography Engineering Design Principles And Also known as secret key cryptography or conventional cryptography, symmetric key cryptography is an encryption system in which the sender and receiver of a message share a single, common key that is used to encrypt and decrypt the message. The document provides comprehensive study notes on cryptography and security, covering topics from the history and fundamentals of cryptography to modern practices like asymmetric cryptography, digital signatures, and password security.

Cryptography Algorithms A Guide To Algorithms In Blockchain Quantum

Cryptography Pdf Cryptography Encryption
Classical Cryptography Pdf Cryptography Cipher

Cryptography Pdf

Cryptography An Open Access Journal From Mdpi

Cs8792 Cryptography And Network Security Pdf Cryptography Public

Modern Cryptography Methods Explained Pdf Cryptography Encryption
Cryptography Pdf Cryptography Encryption

Modern Mathematics And Cryptography Pdf Cryptography Public Key

Chapter 07 Cryptography Pdf Chapter 07 Cryptography Definitions 2

Advjhtp1 07 Pdf Public Key Cryptography Key Cryptography

Cryptography Network Security Notes Pdf Cryptography Introduction

Cs6701 Cryptography And Network Security Pdf Cryptography Public

Cryptography Pdf

Cryptography Pdf Cryptography Applied Mathematics

Pdf Cryptography 07 00020

Cryptography Pdf

Cryptography An Open Access Journal From Mdpi
Ppt Download Pdf Handbook Of Applied Cryptography Discrete
Cryptography Pdf Cryptography Cipher
10 Cryptography Books For Free Pdf

Cryptography Pdf
Cryptography Standards For Pdf Digital Signatures Nutrient

Pdf International Workshop On Coding And Cryptography Pdf Télécharger

Cryptography 07 00040 Cryptography 2023 7 40 2 Of 18 Such As
Cryptography Pdf Cryptography Cipher
Cse2203 Lecture 3 Modern Cryptography And Cryptographic Mechanisms
Pdf Cryptography Cipher Schemes A Cryptographic Scheme Is An

Cryptography 05 00038 V2 Pdf Cryptography Review Post Quantum And

00020 Pdf

File 00020 Pdf
Comments are closed.