Pdf An Overview Of Security Attack

Emerging Technology Iot And Ot Overview Security Threats Attacks And With the recurrence of cyber attacks on the rise, governments and security organizations worldwide are taking proactive measures to reduce the risk of successful attacks against critical infrastructures. Attackers exploit vulnerabilities that exist in hardware, software, and communication layers. various types of cyber attacks include distributed denial of service (ddos), phishing,.
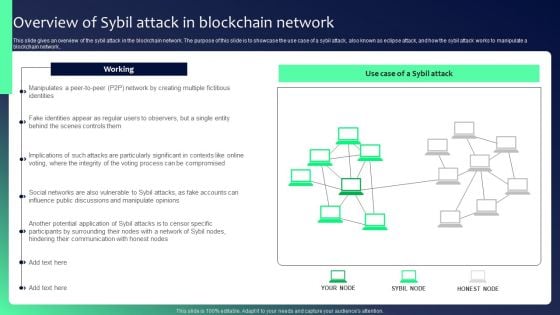
Blockchain Security Solutions Deployment Overview Of Sybil Attack In In order to develop necessary measures against cybercrime, we need to understand different kinds of cybercrime. our paper gives you an overview of various types of cyber crime like malware, phishing, zero day exploit, advanced persistent threat (apt). It describes different types of attacks such as denial of service attacks, backdoors, sniffing, spoofing, man in the middle attacks, and sql injection. the document also covers security basics like confidentiality, integrity, and availability. This paper aims at presenting a brief overview on the main pdf malware threats, the main detection techniques and gives a perspective on emerging challenges in detecting pdf malware. A phishing attack occurs when an attacker masquerades as a trusted entity and tricks the user into giving away sensitive information such as credit card information or login credentials.

A Systematic Survey Of Attack Detection And Prevention In Connected And This paper aims at presenting a brief overview on the main pdf malware threats, the main detection techniques and gives a perspective on emerging challenges in detecting pdf malware. A phishing attack occurs when an attacker masquerades as a trusted entity and tricks the user into giving away sensitive information such as credit card information or login credentials. Security is the application of technologies, processes, and controls to protect systems, networks, programs, devices and data from cyber attacks. Cyber security is the body of technologies, processes, and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. Various security measures are being taken to fight against these attacks. this paper outlines various network security attacks, their impacts and countermeasures. network attacks can be classified into passive and active, with significant implications for organizational security. A cyber attack is an attack initiated from a computer against a website, computer system or individual computer (collectively, a computer) that compromises the confidentiality, integrity or availability of the computer or information stored on it.

Pdf Emerging Security Attack Detection Using Capsule Neural Network Security is the application of technologies, processes, and controls to protect systems, networks, programs, devices and data from cyber attacks. Cyber security is the body of technologies, processes, and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. Various security measures are being taken to fight against these attacks. this paper outlines various network security attacks, their impacts and countermeasures. network attacks can be classified into passive and active, with significant implications for organizational security. A cyber attack is an attack initiated from a computer against a website, computer system or individual computer (collectively, a computer) that compromises the confidentiality, integrity or availability of the computer or information stored on it.

The Essential Cyber Security Overview Safeguarding Your Digital Life Various security measures are being taken to fight against these attacks. this paper outlines various network security attacks, their impacts and countermeasures. network attacks can be classified into passive and active, with significant implications for organizational security. A cyber attack is an attack initiated from a computer against a website, computer system or individual computer (collectively, a computer) that compromises the confidentiality, integrity or availability of the computer or information stored on it.
Comments are closed.