Password Leakage Zero Trust Zero Knowledge
Analysis Of Zero Key Authentication And Zero Knowledge Proof Zero knowledge encryption means that no one but you – not even the company that’s storing the data – can access and decrypt your data. this protects your information even if the server where it’s held is ever breached. Eth zurich’s deep dive into the world’s top password managers exposes how feature overload and legacy design obscure real security flaws, forcing a rethink of what "zero knowledge" actually.
Zero Knowledge Encryption Tresorit Features Understand how zero knowledge password managers work: client side encryption, key derivation, what servers can (and can’t) see, and the practical security tradeoffs for chrome users and teams. Episode description eth zurich's deep dive into the world's top password managers exposes how feature overload and legacy design obscure real security flaws, forcing a rethink of what "zero knowledge" actually means for your vault. learn why recent fixes matter—and why open source may be your safest bet. In today’s rapidly evolving digital world, ensuring robust security is more important than ever. the two key concepts in modern authentication strategies are zero trust and zero knowledge. Store passwords, api keys, and confidential documents with military grade encryption. our open source platform uses zero knowledge architecture and aes 256 encryption to keep your data truly private.
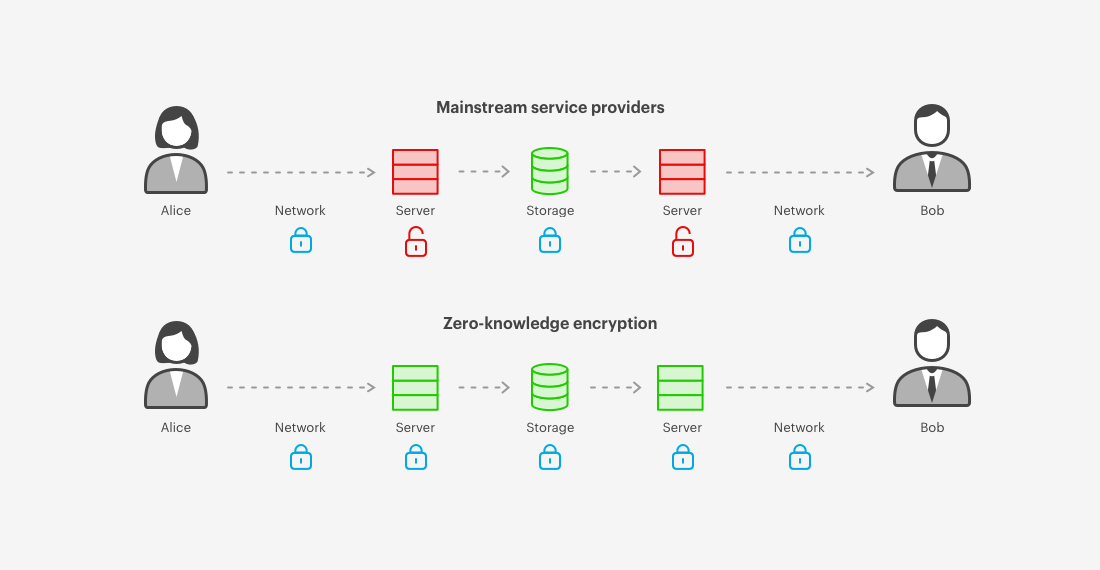
It S High Time To Deploy Zero Knowledge Encryption Tresorit In today’s rapidly evolving digital world, ensuring robust security is more important than ever. the two key concepts in modern authentication strategies are zero trust and zero knowledge. Store passwords, api keys, and confidential documents with military grade encryption. our open source platform uses zero knowledge architecture and aes 256 encryption to keep your data truly private. Eth zurich's deep dive into the world's top password managers exposes how feature overload and legacy design obscure real security flaws, forcing a rethink of what "zero knowledge" actually means for your vault. With a zero knowledge approach, you can rest easy knowing that no one else but you, not even your password manager vendor, has the keys to the kingdom. after all, you wouldn't want anyone else to be able to see the passwords you use to access critical business, it, and financial accounts. Researchers investigate password manager zero knowledge claims, exposing critical attack scenarios and advanced threat vectors for cybersecurity professionals. Zero knowledge primarily focuses on cryptographic methods that validate authentication without exposing sensitive information, while the zero trust framework enforces strict access controls and continuous verification to prevent unauthorized access within a system.
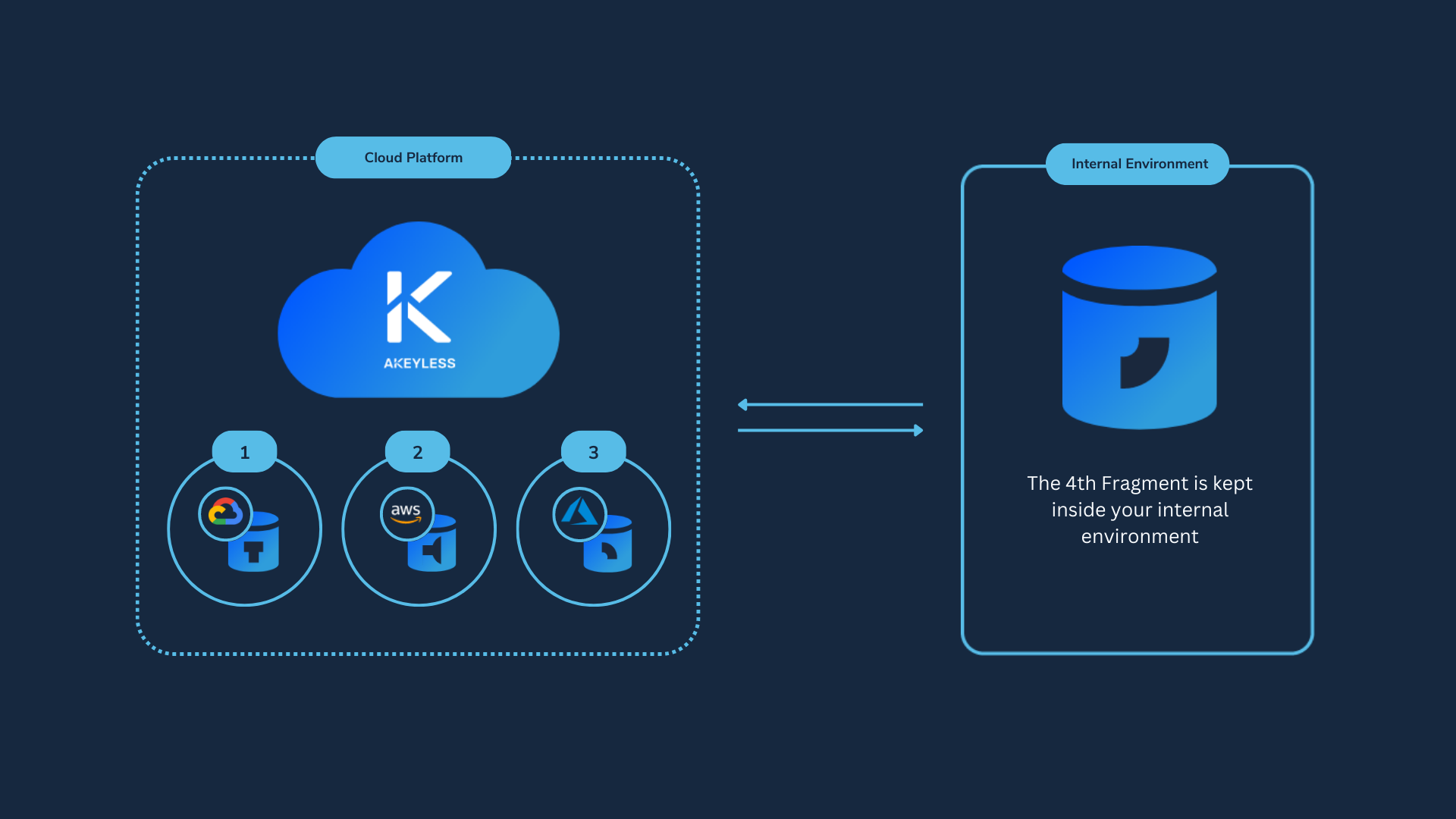
Zero Knowledge Encryption Eth zurich's deep dive into the world's top password managers exposes how feature overload and legacy design obscure real security flaws, forcing a rethink of what "zero knowledge" actually means for your vault. With a zero knowledge approach, you can rest easy knowing that no one else but you, not even your password manager vendor, has the keys to the kingdom. after all, you wouldn't want anyone else to be able to see the passwords you use to access critical business, it, and financial accounts. Researchers investigate password manager zero knowledge claims, exposing critical attack scenarios and advanced threat vectors for cybersecurity professionals. Zero knowledge primarily focuses on cryptographic methods that validate authentication without exposing sensitive information, while the zero trust framework enforces strict access controls and continuous verification to prevent unauthorized access within a system.

Your 2026 Guide To Zero Knowledge Encryption Researchers investigate password manager zero knowledge claims, exposing critical attack scenarios and advanced threat vectors for cybersecurity professionals. Zero knowledge primarily focuses on cryptographic methods that validate authentication without exposing sensitive information, while the zero trust framework enforces strict access controls and continuous verification to prevent unauthorized access within a system.
Comments are closed.