Password Cracking Can A Rainbow Table Reverse A Hashed Password
Password Cracking Revisited Rainbow Tables Redmondmag In january 2026, security firm mandiant released a rainbow table targeting ntlmv1 hashes that can recover passwords in under 12 hours using consumer hardware costing less than $600. Passwords are typically stored not in plain text form, but as hash values. if such a database of hashed passwords falls into the hands of attackers, they can use a precomputed rainbow table to recover the plaintext passwords.
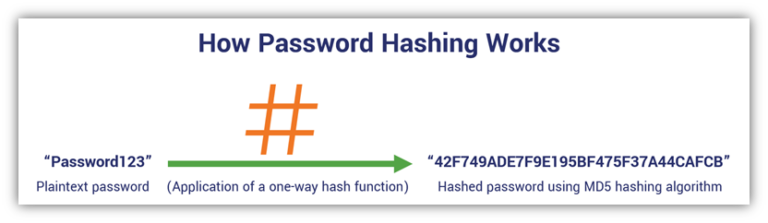
Rainbow Tables A Path To Password Gold For Cybercriminals Hashed Out A rainbow table attack is a password cracking technique where a threat actor uses a precomputed table to reverse cryptographic hashes and reveal plaintext passwords. Whenever a user enters a password, it is converted into a hash value and is compared with the already stored hash value. if the values match, the user is authenticated. a rainbow table is a database that is used to gain authentication by cracking the password hash. Since each password gets a unique salt, even if two users choose the same password, they will have different hash values — making rainbow tables impossible to build. The answer: they don’t reverse hashes. they guess passwords, hash them forward, and match the results. mike breaks down how rainbow tables speed this up with precomputed hashes, and why salting makes those precomputations far less effective by forcing attackers to redo work per user.
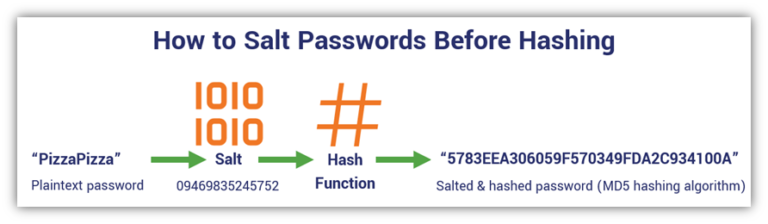
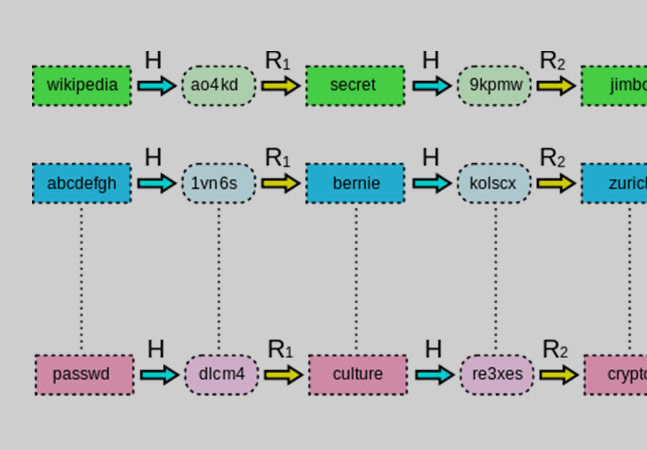
Rainbow Tables A Path To Password Gold For Cybercriminals Hashed Out Since each password gets a unique salt, even if two users choose the same password, they will have different hash values — making rainbow tables impossible to build. The answer: they don’t reverse hashes. they guess passwords, hash them forward, and match the results. mike breaks down how rainbow tables speed this up with precomputed hashes, and why salting makes those precomputations far less effective by forcing attackers to redo work per user. A rainbow table attack is a precomputed method used to reverse cryptographic hash functions, primarily targeting hashed passwords. in simpler terms, it allows someone to turn a hashed password back into its plaintext form by looking it up in a massive table of pre computed hashes. A rainbow table is a precomputed table used for reversing cryptographic hash functions, primarily for cracking password hashes. hash functions are algorithms that turn a set of data (like a password) into a fixed size string of characters, which is typically a sequence of numbers and letters. Rainbow table attacks represent an elegant application of the time memory trade off to the problem of password cracking. for a period in the early 2000s, they were devastatingly effective against the unsalted hash storage that was common at the time. A rainbow table is a precomputed lookup table used to reverse cryptographic hash functions. instead of guessing every password and hashing it in real time (brute force), attackers generate massive tables of password–hash pairs in advance.
Rainbow Tables A Path To Password Gold For Cybercriminals Hashed Out A rainbow table attack is a precomputed method used to reverse cryptographic hash functions, primarily targeting hashed passwords. in simpler terms, it allows someone to turn a hashed password back into its plaintext form by looking it up in a massive table of pre computed hashes. A rainbow table is a precomputed table used for reversing cryptographic hash functions, primarily for cracking password hashes. hash functions are algorithms that turn a set of data (like a password) into a fixed size string of characters, which is typically a sequence of numbers and letters. Rainbow table attacks represent an elegant application of the time memory trade off to the problem of password cracking. for a period in the early 2000s, they were devastatingly effective against the unsalted hash storage that was common at the time. A rainbow table is a precomputed lookup table used to reverse cryptographic hash functions. instead of guessing every password and hashing it in real time (brute force), attackers generate massive tables of password–hash pairs in advance.
Comments are closed.