Partial Homomorphic Encryption Pptx

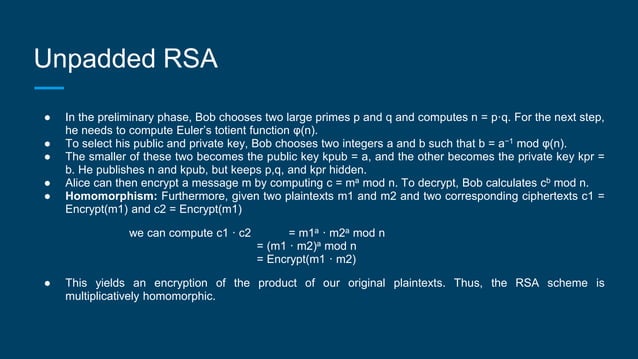
Fully Homomorphic Encryption 1 Pptx The document discusses homomorphic encryption, enabling computations on encrypted data without accessing the plaintext. it covers types of homomorphic encryption including partially and fully homomorphic schemes, and provides examples like rsa, elgamal, and paillier. Topic 20 * commutative encryption definition: an encryption scheme is commutative if ek1[ek2[m]] = ek2[ek1[m]] given an encryption scheme that is commutative, then dk1[dk2[ek1[ek2[m]] = m that is, if message is encrypted twice, the order does not matter.
Fully Homomorphic Encryption 1 Pptx Parties are equal > symmetric scenario: alice wants to send a message to bob alice and bob have previously agreed on a symmetric encryption scheme and a secret key k, the message can be sent encrypted examples: data encryption standard (des) advanced encryption standard (aes). Because microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of microsoft, and microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. It provides examples of partially homomorphic encryption schemes like rsa that allow only addition or multiplication, and fully homomorphic encryption introduced by craig gentry in 2009 that allows any computation. The size (bit length) of the evaluated ciphertext and the runtime of the decryption is independent of the complexity of the evaluated function. a relaxation (leveled homomorphic encryption): the size (bit length) of the evaluated ciphertext and the runtime of the decryption depends on the.
Fully Homomorphic Encryption 1 Pptx Web Development Internet It provides examples of partially homomorphic encryption schemes like rsa that allow only addition or multiplication, and fully homomorphic encryption introduced by craig gentry in 2009 that allows any computation. The size (bit length) of the evaluated ciphertext and the runtime of the decryption is independent of the complexity of the evaluated function. a relaxation (leveled homomorphic encryption): the size (bit length) of the evaluated ciphertext and the runtime of the decryption depends on the. Id phenotype “parties learn the genotype phenotype correlations and nothing else” homomorphic encryption: syntax 𝑠𝑘,𝑒𝑘←𝐺𝑒𝑛1𝑛. ppt key generation algorithm generates a secret key as well as a (public) evaluation key. 𝑐←𝐸𝑛𝑐𝑠𝑘,𝑚. Homomorphic encryption has two parts: 1. hybrid homomorphic encryption. 2. partial homomorphic encryption. what are the two types of homomorphic encryption? 1. hybrid homomorphic encryption. in this order of technology creates very fast data secure even when waiting in cloud. This document discusses homomorphic encryption techniques including partially homomorphic encryptions that support either addition or multiplication operations, and fully homomorphic encryption introduced by craig gentry that supports both types of operations. Current research continues to explore practical implementations, especially in conjunction with other privacy technologies. download as a pptx, pdf or view online for free.
Fully Homomorphic Encryption 1 Pptx Web Development Internet Id phenotype “parties learn the genotype phenotype correlations and nothing else” homomorphic encryption: syntax 𝑠𝑘,𝑒𝑘←𝐺𝑒𝑛1𝑛. ppt key generation algorithm generates a secret key as well as a (public) evaluation key. 𝑐←𝐸𝑛𝑐𝑠𝑘,𝑚. Homomorphic encryption has two parts: 1. hybrid homomorphic encryption. 2. partial homomorphic encryption. what are the two types of homomorphic encryption? 1. hybrid homomorphic encryption. in this order of technology creates very fast data secure even when waiting in cloud. This document discusses homomorphic encryption techniques including partially homomorphic encryptions that support either addition or multiplication operations, and fully homomorphic encryption introduced by craig gentry that supports both types of operations. Current research continues to explore practical implementations, especially in conjunction with other privacy technologies. download as a pptx, pdf or view online for free.
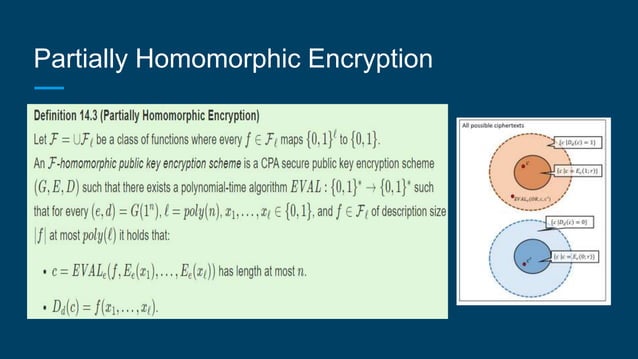
Fully Homomorphic Encryption 1 Pptx Web Development Internet This document discusses homomorphic encryption techniques including partially homomorphic encryptions that support either addition or multiplication operations, and fully homomorphic encryption introduced by craig gentry that supports both types of operations. Current research continues to explore practical implementations, especially in conjunction with other privacy technologies. download as a pptx, pdf or view online for free.
Comments are closed.