Partial Homomorphic Encryption Explained

Partial Homomorphic Encryption Pptx In this article, we break down the two main types — partial and full homomorphic encryption — and show you how to get started with python examples that bring the concepts to life. Unlike conventional encryption, which calls for statistics to be decrypted for any significant operation, homomorphic encryption permits computations to be performed at once on encrypted statistics.
Partial Homomorphic Encryption Pptx Many classical encryption schemes have partial homomorphic properties. even the famous rsa or elgamal cryptosystem allow us to perform some meaningful homomorphic operations. Partially homomorphic encryption encompasses schemes that support the evaluation of circuits consisting of only one type of gate, e.g., addition or multiplication. somewhat homomorphic encryption schemes can evaluate two types of gates, but only for a subset of circuits. In rsa we can homomorphically multiply two ciphered values, and gain the result of a multiplication when we decipher them. so with rsa we cipher with: \ (cipher = m^e \pmod n\) and where \ (e\) is the encryption key, and \ (n\) is the multiplication of two prime numbers (\ (p\) and \ (q\)). A beginner friendly guide to homomorphism and how they power real cryptosystems: rsa and paillier through partially homomorphic encryption.
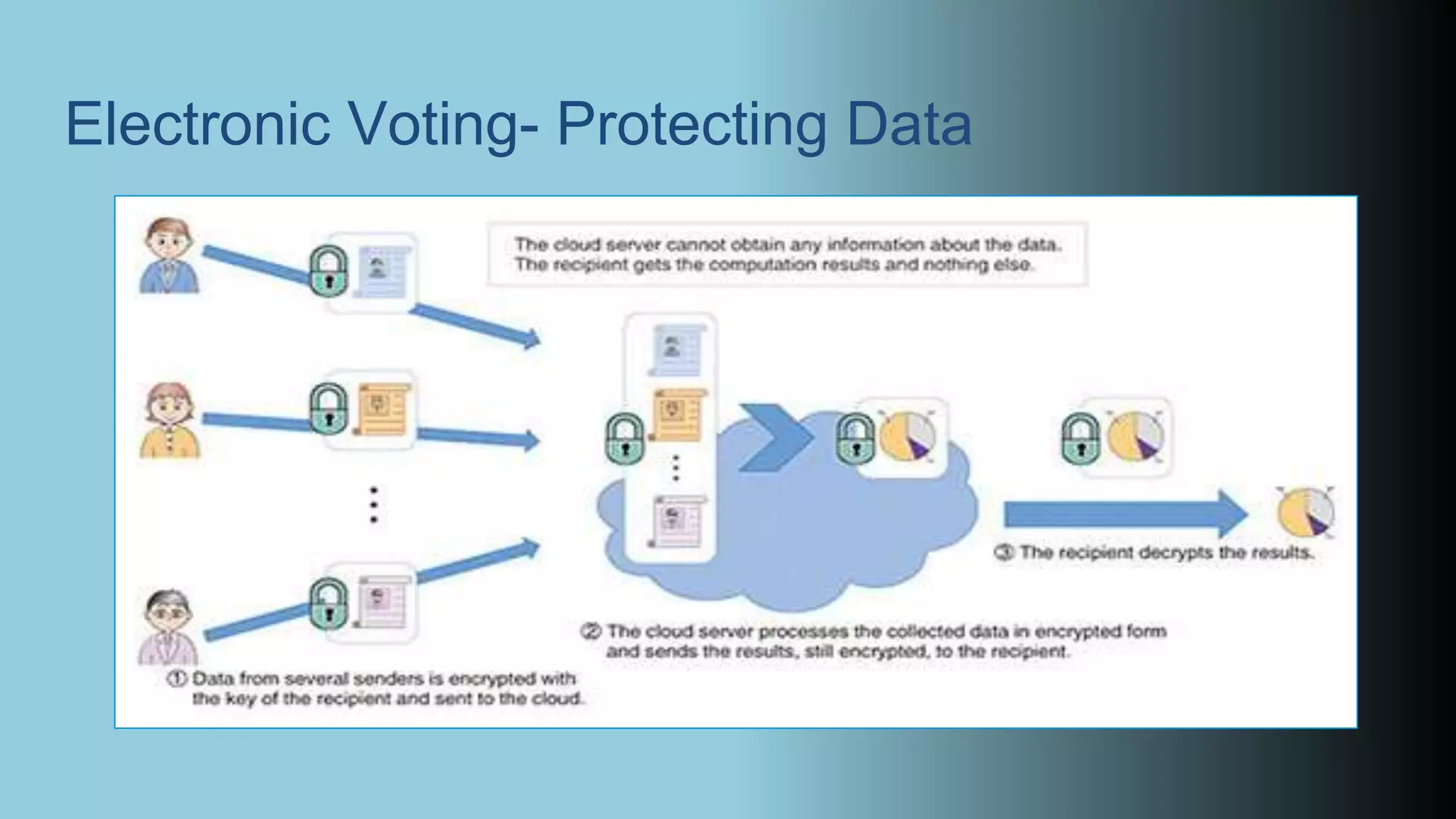
Github Vaibhavg277 Partial Homomorphic Encryption On Machine Learning In rsa we can homomorphically multiply two ciphered values, and gain the result of a multiplication when we decipher them. so with rsa we cipher with: \ (cipher = m^e \pmod n\) and where \ (e\) is the encryption key, and \ (n\) is the multiplication of two prime numbers (\ (p\) and \ (q\)). A beginner friendly guide to homomorphism and how they power real cryptosystems: rsa and paillier through partially homomorphic encryption. In such case, only the encrypted version of the data is given to the untrusted computer to process. the computer will perform computations on this encrypted data, without knowledge of the original plaintext. In this post, we’ll break down what homomorphic encryption is, why it matters in today’s privacy first digital world, and how you can start experimenting with it—even if you don’t have a background in cryptography or security. Partial homomorphic encryption schemes provide a middle ground, supporting either addition or multiplication operations but not both. the paillier cryptosystem, for example, supports homomorphic addition, allowing encrypted values to be added together without decryption. However, the type of computation depends on the type of he schemes in use, such as partially homomorphic encryption (phe), somewhat homomorphic encryption (she), and fully homomorphic encryption (fhe) are such examples.
Partial Homomorphic Encryption Ppt In such case, only the encrypted version of the data is given to the untrusted computer to process. the computer will perform computations on this encrypted data, without knowledge of the original plaintext. In this post, we’ll break down what homomorphic encryption is, why it matters in today’s privacy first digital world, and how you can start experimenting with it—even if you don’t have a background in cryptography or security. Partial homomorphic encryption schemes provide a middle ground, supporting either addition or multiplication operations but not both. the paillier cryptosystem, for example, supports homomorphic addition, allowing encrypted values to be added together without decryption. However, the type of computation depends on the type of he schemes in use, such as partially homomorphic encryption (phe), somewhat homomorphic encryption (she), and fully homomorphic encryption (fhe) are such examples.
Comments are closed.