Packet Injection Pdf Transmission Control Protocol Computer Network

Transmission Control Protocol In Computer Networks 1 1 Pdf Packet injection free download as pdf file (.pdf), text file (.txt) or read online for free. This document specifies the transmission control protocol (tcp). tcp is an important transport layer protocol in the internet protocol stack, and it has continuously evolved over decades of use and growth of the internet.
Computer Network Tcp Ip Transmission Control Protocol Internet This document describes the functions to be performed by the transmission control protocol, the program that implements it, and its interface to programs or users that require its services. Lecture 16: tcp ip vulnerabilities and dos attacks: ip spoofing, syn flooding, and the shrew dos attack lecture notes on “computer and network security”. Tcp is connection oriented and full duplex. the maximum segment size (mss)is set during connection establishment. reliability is achieved using acknowledgments, round trip delay estimations and data retransmission. tcp uses a variable window mechanism for flow control. What features must transport protocol implement to support these abstractions? meh! nothing else! each host tells its isn to the other host. e.g., why not just use isn = 0? how does this help? how fast will data be transferred? what’s missing? how to do this efficiently? extend tcp’s existing window based protocol all these windows.
Transmission Control Protocol Internet Protocol Studocu Tcp is connection oriented and full duplex. the maximum segment size (mss)is set during connection establishment. reliability is achieved using acknowledgments, round trip delay estimations and data retransmission. tcp uses a variable window mechanism for flow control. What features must transport protocol implement to support these abstractions? meh! nothing else! each host tells its isn to the other host. e.g., why not just use isn = 0? how does this help? how fast will data be transferred? what’s missing? how to do this efficiently? extend tcp’s existing window based protocol all these windows. The transmission control protocol tcp is one of the most important protocols of internet protocols suite. it is most widely used protocol for data transmission in communication network such as internet. When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!. Tcp is one of the most important protocols of internet protocols suite. it is most widely used protocol for data transmission in communication network such as internet. This literature review explores the network transmission process, examining how data packets travel across networks, and the various types of sniffing that can compromise data privacy and security.
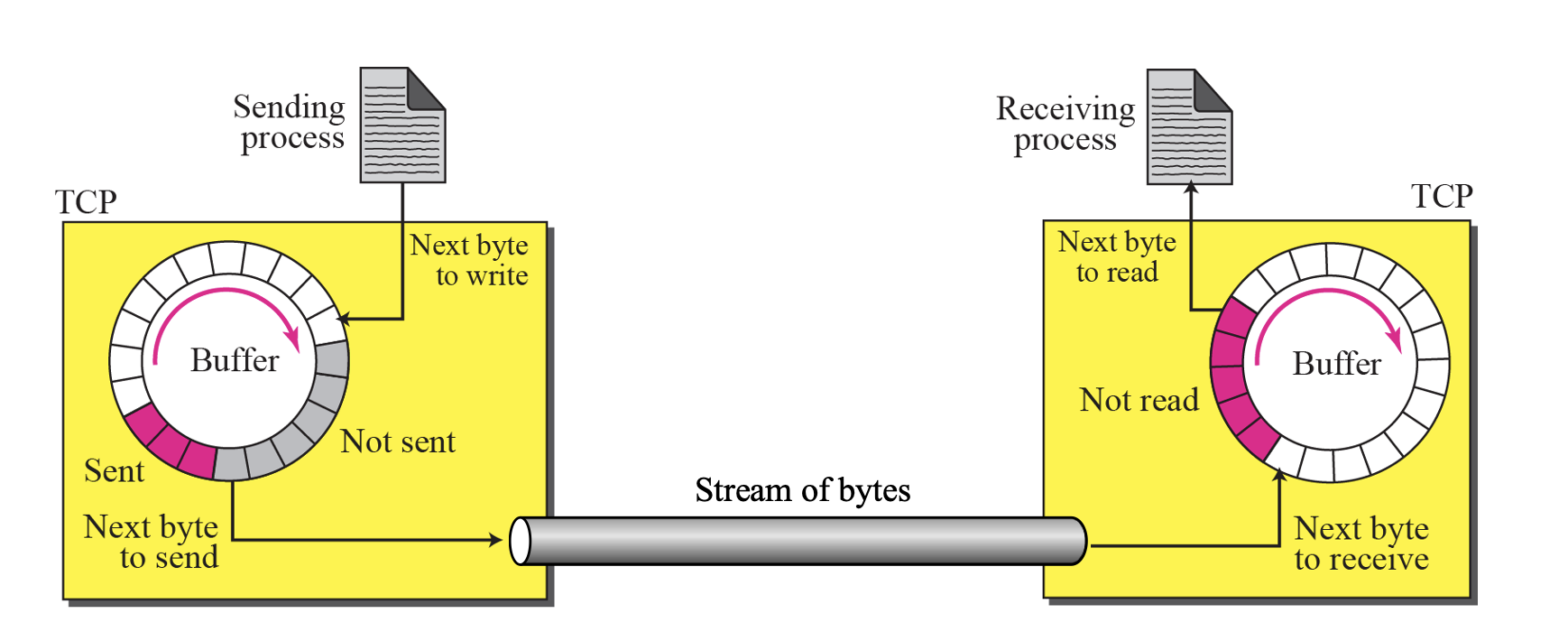
Transmission Control Protocol The transmission control protocol tcp is one of the most important protocols of internet protocols suite. it is most widely used protocol for data transmission in communication network such as internet. When sender’s retransmit timer expires, two indistinguishable cases (why?): in latter case, duplicate data packet reaches receiver! how to prevent receiver from passing duplicates to application? how many tombstones must receiver store? also should cover layer 3 source and destination!. Tcp is one of the most important protocols of internet protocols suite. it is most widely used protocol for data transmission in communication network such as internet. This literature review explores the network transmission process, examining how data packets travel across networks, and the various types of sniffing that can compromise data privacy and security.
Transmission Control Protocolinternet Protocol Tcp is one of the most important protocols of internet protocols suite. it is most widely used protocol for data transmission in communication network such as internet. This literature review explores the network transmission process, examining how data packets travel across networks, and the various types of sniffing that can compromise data privacy and security.

Chpter 2 Computer Network Pdf Transport Layer Security
Comments are closed.