Owasp Top 10 Api Vulnerabilities Explained Part One Tryhackme
Owasp Api Top 10 Explained With Real World Examples This room covers the first five owasp api security top 10 vulnerabilities using a deployable windows vm with talend api tester and a laravel app running on localhost:80 mht. Practical walkthrough of owasp api top 10 vulnerabilities with real exploitation steps and effective security fixes.
Owasp Api Security Top 10 Wattlecorp Cybersecurity Labs Ready to learn cyber security? the owasp api security top 10 1 room is only available for premium users. signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment. Tryhackme: owasp api security top 10 1 room question solutions are written with explanations and visuals. 📌 task 1 — introduction 🧠 what’s happening you’re basically spinning up a windows vm talend api tester vulnerable laravel app. ️ this environment is pre configured for testing api vulnerabilities. Contribute to thmrevenant tryhackme development by creating an account on github.

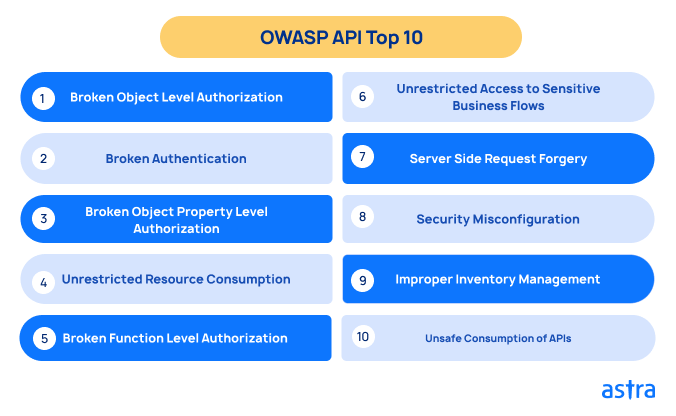
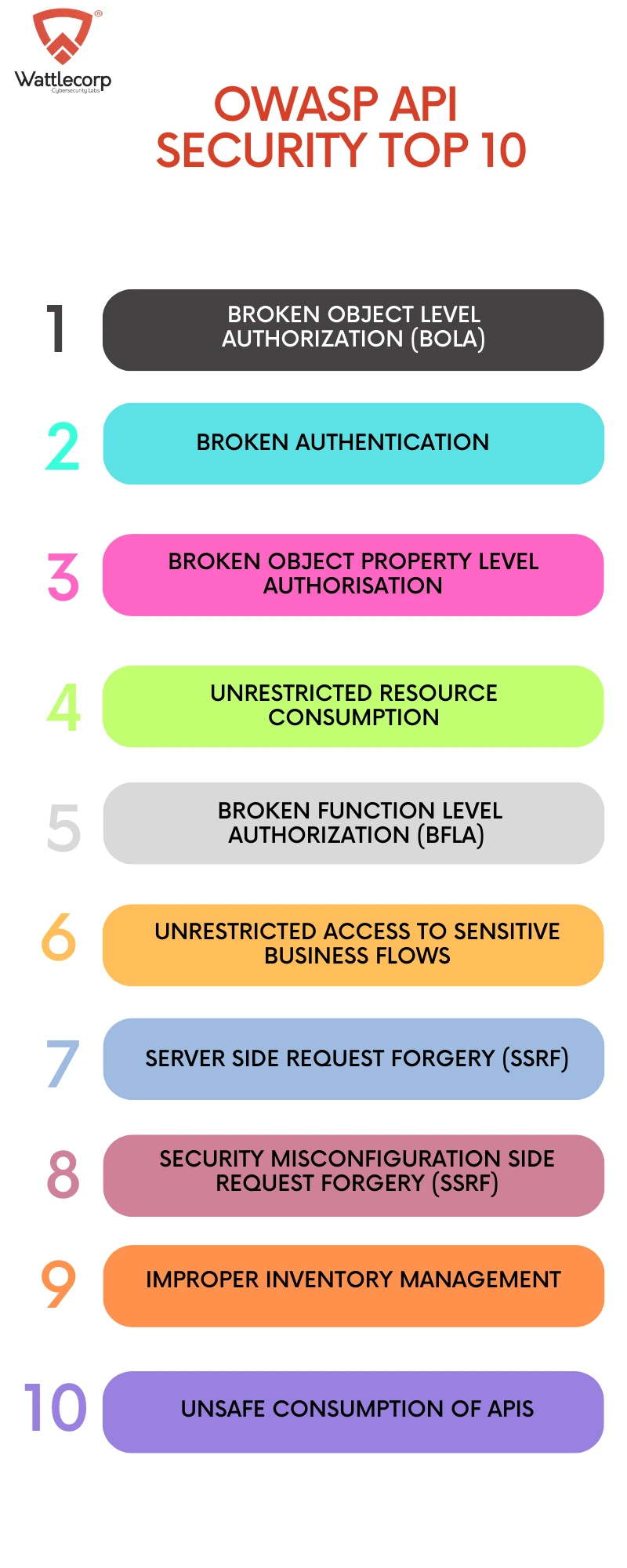
Protect Against Owasp Api Security Top 10 Vulnerabilities 📌 task 1 — introduction 🧠 what’s happening you’re basically spinning up a windows vm talend api tester vulnerable laravel app. ️ this environment is pre configured for testing api vulnerabilities. Contribute to thmrevenant tryhackme development by creating an account on github. In this video walk through, we covered the first part of explaining owasp top api 10. The owasp api security project seeks to provide value to software developers and security assessors by underscoring the potential risks in insecure apis, and illustrating how these risks may be mitigated. Now that we understand the threat and the damage caused due to non adherence to mitigation measures — let’s discuss developing a secure api through owasp api security top 10 principles. In 2019 the project released the top ten api vulnerabilities list. this module covers the first five principles in part one and the remaining principles in part two.
Owasp Top 10 Ultimate Guide For Api Security Appknox In this video walk through, we covered the first part of explaining owasp top api 10. The owasp api security project seeks to provide value to software developers and security assessors by underscoring the potential risks in insecure apis, and illustrating how these risks may be mitigated. Now that we understand the threat and the damage caused due to non adherence to mitigation measures — let’s discuss developing a secure api through owasp api security top 10 principles. In 2019 the project released the top ten api vulnerabilities list. this module covers the first five principles in part one and the remaining principles in part two.
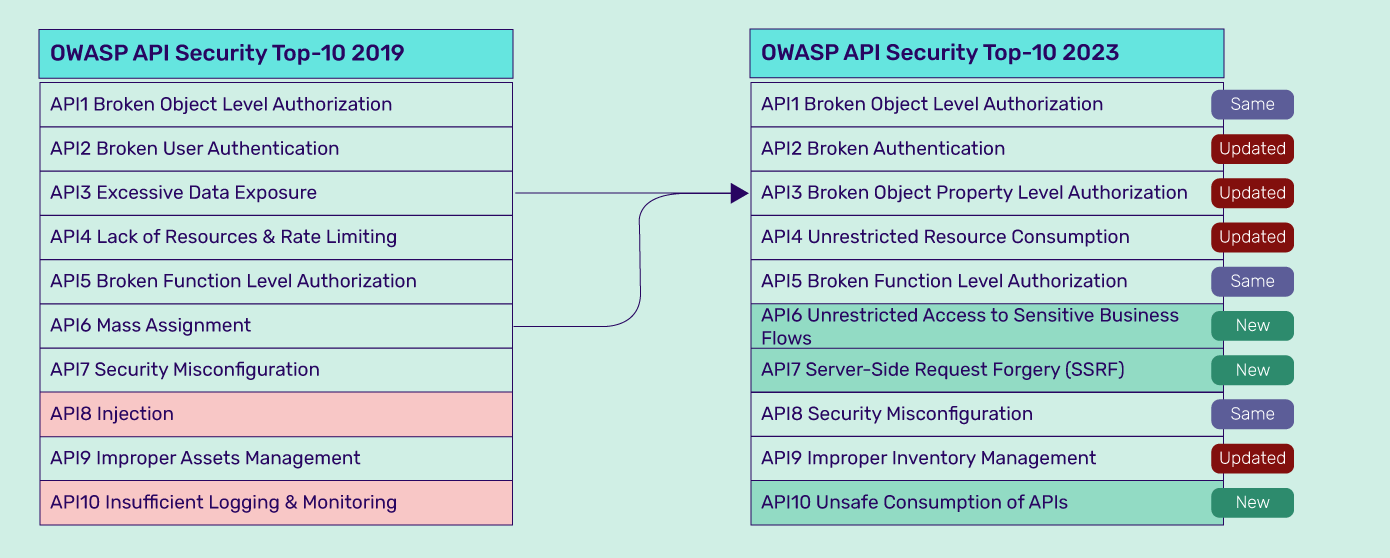
What S New In Owasp Api Top 10 2023 Indusface Blog Now that we understand the threat and the damage caused due to non adherence to mitigation measures — let’s discuss developing a secure api through owasp api security top 10 principles. In 2019 the project released the top ten api vulnerabilities list. this module covers the first five principles in part one and the remaining principles in part two.
Comments are closed.