Owasp Secure Coding Practices Checklist Pdf Password Computers
Owasp Secure Coding Practices Quick Reference Guide Download Free Owasp secure coding practices free download as pdf file (.pdf), text file (.txt) or read online for free. owasp secure coding practices. This technology agnostic document defines a set of general software security coding practices, in a checklist format, that can be integrated into the software development lifecycle.

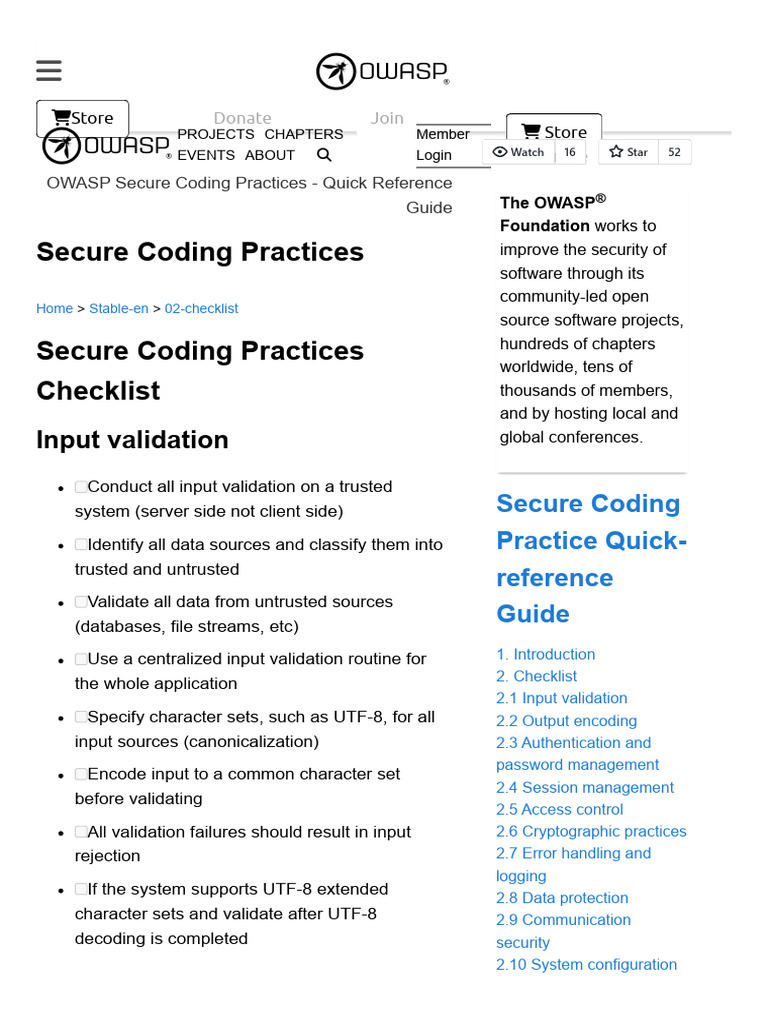
Secure Coding Practices Pdf Password Http Cookie It includes practices like requiring authentication for most resources, using standard authentication services, securely storing and handling passwords, enforcing password complexity and reset policies, and monitoring for suspicious activities. Explore owasp’s secure coding practice checklist & learn how to mitigate the most common software vulnerabilities to protect your business and customers. These recommendations are maintained by a community of experienced developers and security pros and are available in both web and pdf form for easy reference. i’ll summarise the checklist area by area, give real examples you can follow in code reviews and testing, and show how to train teams. This document provides a quick reference guide for secure coding practices. it contains a checklist of over 50 secure coding practices organized into categories such as input validation, authentication, session management, and access control.
Owasp Secure Coding Checklist These recommendations are maintained by a community of experienced developers and security pros and are available in both web and pdf form for easy reference. i’ll summarise the checklist area by area, give real examples you can follow in code reviews and testing, and show how to train teams. This document provides a quick reference guide for secure coding practices. it contains a checklist of over 50 secure coding practices organized into categories such as input validation, authentication, session management, and access control. Uspicious activities. the goal is to protect user accounts, data, and sensitive functions by implementing strong authentication and password management practices, ultimately safeguarding against unauthorized access. For the project, see owasp secure coding practices – quick reference guide. 1. conduct all data validation on a trusted system (e.g., the server) 2. identify all data sources and classify them into trusted and untrusted. validate all data from untrusted sources (e.g., databases, file streams, etc.) 3. The document is a checklist of secure coding practices based on owasp guidelines, covering various aspects such as input validation, output encoding, authentication, session management, and access control. Use a single site wide component to check access authorization. this includes libraries that call external authorization services. create an access control policy to document an application's business rules, data types and access authorization criteria and or processes so that access can be properly provisioned and controlled.
Comments are closed.