Outdated Owasp Advice

Vulnerable And Outdated Components Practical Overview Owasp Top 10 Outdated software can lead to a variety of different vulnerabilities, ranging from vulnerabilities with a low criticality to vulnerabilities causing compromization of the entire system. the severity and amount of these vulnerabilities in an outdated software system depends on the individual case. Learn about owasp a06: its causes, business risks, real world attacks, and how to prevent vulnerable and outdated components.
Github Arbucheli Owasp Top 10 Vulnerable And Outdated Components Learn how to manage vulnerable and outdated components—a major owasp top 10 cybersecurity risk—by combining sca, patch management, and dast first testing. Learn how to identify, manage, and protect against vulnerable and outdated components—a critical risk in the owasp top 10. discover best practices to reduce real world threats by combining sca with dast. Discover how to manage vulnerable and outdated components—an owasp top 10 risk—using inventory management, patching, and dynamic security testing for safer apps. 💡 quick tips on mitigation: keep a complete inventory of all software components in use. regularly update libraries, plugins, and frameworks. subscribe to vulnerability databases like cve alerts.

Owasp Top 10 Vulnerable And Outdated Components By Hadley Swello On Prezi Discover how to manage vulnerable and outdated components—an owasp top 10 risk—using inventory management, patching, and dynamic security testing for safer apps. 💡 quick tips on mitigation: keep a complete inventory of all software components in use. regularly update libraries, plugins, and frameworks. subscribe to vulnerability databases like cve alerts. Vulnerable and outdated components are a supply chain risk lurking in every modern application. proactively updating, auditing, and monitoring all software dependencies is no longer optional—it's critical for defending against today's sophisticated attacks and reducing organizational risk. Outdated components are a silent security risk but one that attackers love to exploit. that's why owasp ranks it at no.6 in its top 10. but what exactly is the risk, how do attackers take advantage of it, and how can you prevent it?. Using outdated versions of technologies in a website can be dangerous because it exposes the site to known security vulnerabilities, leading to potential data breaches, performance issues, and compatibility problems. In this article, let’s break down everything you need to know about vulnerable and outdated components — why they matter, real world examples, and how you can protect your applications.
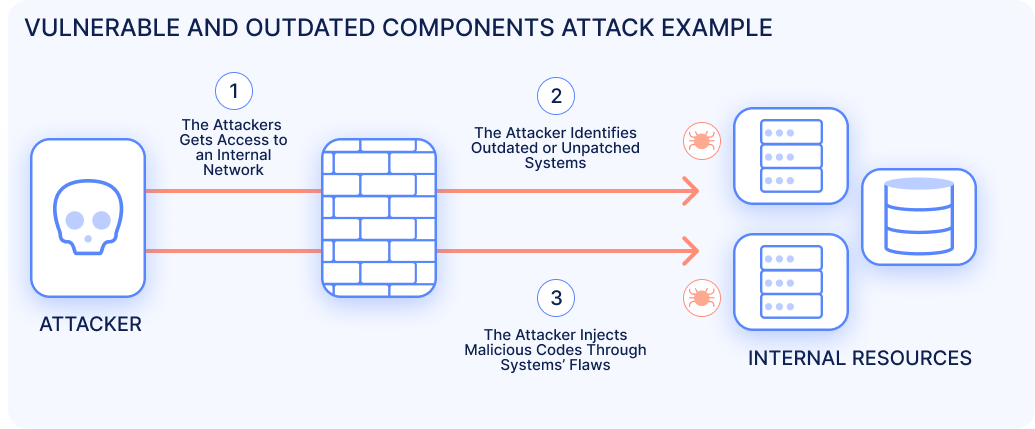
Owasp Top 10 Vulnerable And Outdated Components Ionix Vulnerable and outdated components are a supply chain risk lurking in every modern application. proactively updating, auditing, and monitoring all software dependencies is no longer optional—it's critical for defending against today's sophisticated attacks and reducing organizational risk. Outdated components are a silent security risk but one that attackers love to exploit. that's why owasp ranks it at no.6 in its top 10. but what exactly is the risk, how do attackers take advantage of it, and how can you prevent it?. Using outdated versions of technologies in a website can be dangerous because it exposes the site to known security vulnerabilities, leading to potential data breaches, performance issues, and compatibility problems. In this article, let’s break down everything you need to know about vulnerable and outdated components — why they matter, real world examples, and how you can protect your applications.

Owasp Top 10 Part 6 Vulnerable And Outdated Components Hackyourmom Using outdated versions of technologies in a website can be dangerous because it exposes the site to known security vulnerabilities, leading to potential data breaches, performance issues, and compatibility problems. In this article, let’s break down everything you need to know about vulnerable and outdated components — why they matter, real world examples, and how you can protect your applications.
Vulnerable And Outdated Components Owasp Top 10 6
Comments are closed.