Oscp Buffer Overflow Done Quick
Github Carlmon Oscp Buffer Overflow You need to know these top 10 cyber security interview questions elevatecybersecurity interviewwebsite elevatecybersecurity githubhttps:. All the payloads generated in this article can be tested using a simple buffer overflow emulation app (bov.cpp) which can be found at [2] along with building and use of instructions for windows.
Github Suyambu Education Oscp Like Stack Buffer Overflow Buffer overflow isn’t on the exam. no bof. i am preparing the oscp and i just started the fixing exploit part with buffer overflow i practically finished it, but i noticed something. this is…. As i was taking the oscp course i found that buffer overflows were a tedious process and very frustrating to understand as a beginner. i hope this walkthrough resonates with anyone having a. Just check whether the ip inside the script is correct and make sure to run again the oscp.exe in immunity debugger before running the script. buffer.append("a" * counter) counter = 100 for string in buffer: try: s = socket.socket(socket.af inet, socket.sock stream) s.settimeout(timeout) connect = s.connect((ip, port)) s.recv(1024). I'll extend an olive branch and give you a quick rundown of this simple typfe of bofs and what we're trying to do. a bof will occur when a program receives data that is longer than expected. when that happens you can often overwrite the entire buffer memory space on the stack.

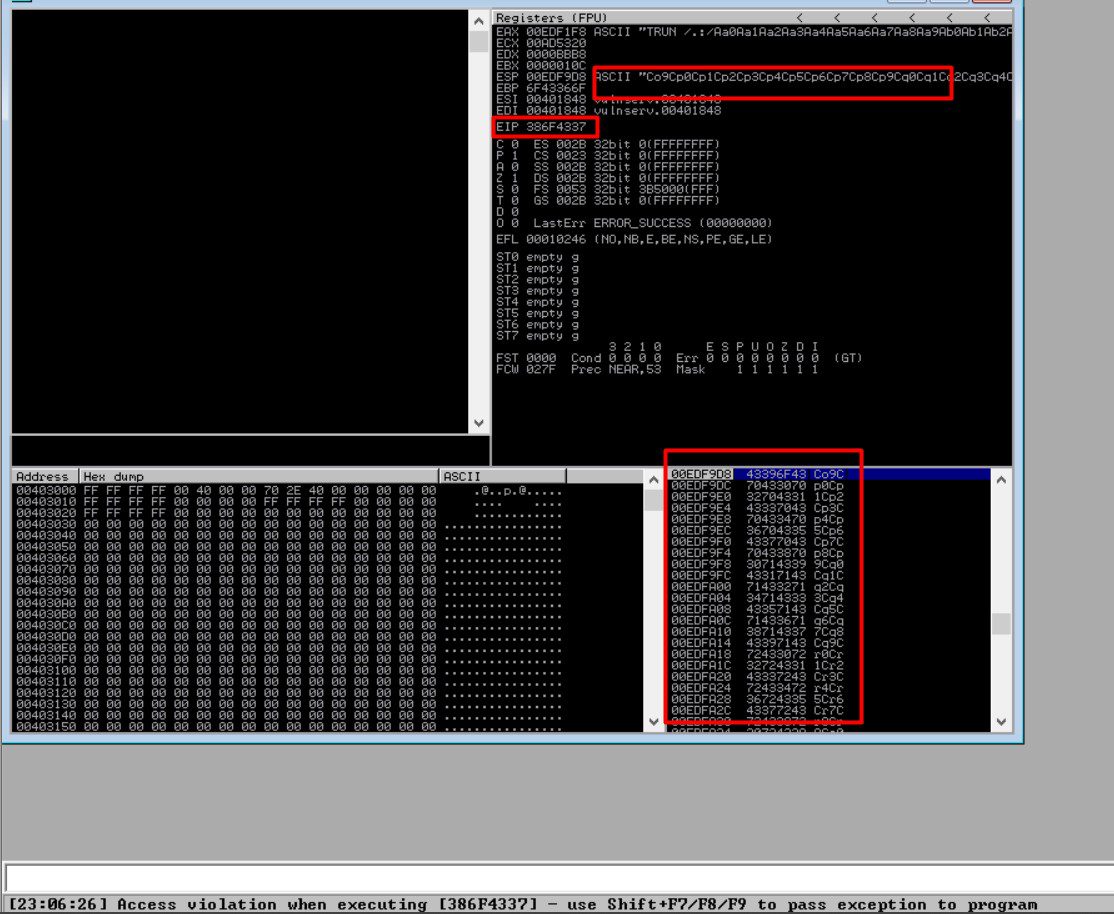
Oscp Notes Buffer Overflow Md At Main Jswinss Oscp Notes Github Just check whether the ip inside the script is correct and make sure to run again the oscp.exe in immunity debugger before running the script. buffer.append("a" * counter) counter = 100 for string in buffer: try: s = socket.socket(socket.af inet, socket.sock stream) s.settimeout(timeout) connect = s.connect((ip, port)) s.recv(1024). I'll extend an olive branch and give you a quick rundown of this simple typfe of bofs and what we're trying to do. a bof will occur when a program receives data that is longer than expected. when that happens you can often overwrite the entire buffer memory space on the stack. A lot can be said about buffer overflows and they are perhaps the most daunting part of attempting the oscp for most. however, as you'll find in most of your offensive hacking endeavors, it's all about experimentation and tweaking your process. Follow each step and you'll be able to craft a working example of a bof exploitation. all the specific variable are stored in 1 single resource file, to avoid any confusion during the exam. after each step, fill the proper variables with values found and they'll be re used for the next step. A beginner friendly oscp buffer overflow lab setup includes a windows 7 or windows 10 32 bit virtual machine with a vulnerable application like vulnserver, immunity debugger with mona.py installed for exploit development, and a kali linux machine as the attacker. the setup allows safe practice of buffer overflow concepts required for oscp certification. Stack buffer overflow is a memory corruption vulnerability that occurs when a program writes more data to a buffer located on the stack than what is actually allocated for that buffer, therefore overflowing to a memory address that is outside of the intended data structure.
Easy Oscp Bufferoverflow Preparation Hum4ng0d Github Io A lot can be said about buffer overflows and they are perhaps the most daunting part of attempting the oscp for most. however, as you'll find in most of your offensive hacking endeavors, it's all about experimentation and tweaking your process. Follow each step and you'll be able to craft a working example of a bof exploitation. all the specific variable are stored in 1 single resource file, to avoid any confusion during the exam. after each step, fill the proper variables with values found and they'll be re used for the next step. A beginner friendly oscp buffer overflow lab setup includes a windows 7 or windows 10 32 bit virtual machine with a vulnerable application like vulnserver, immunity debugger with mona.py installed for exploit development, and a kali linux machine as the attacker. the setup allows safe practice of buffer overflow concepts required for oscp certification. Stack buffer overflow is a memory corruption vulnerability that occurs when a program writes more data to a buffer located on the stack than what is actually allocated for that buffer, therefore overflowing to a memory address that is outside of the intended data structure.
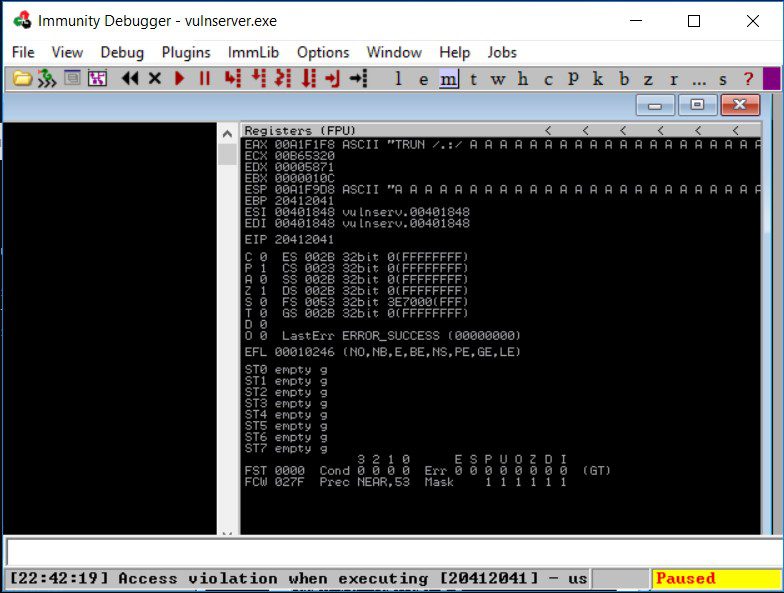
Oscp Detail Guide To Stack Based Buffer Overflow 6 A beginner friendly oscp buffer overflow lab setup includes a windows 7 or windows 10 32 bit virtual machine with a vulnerable application like vulnserver, immunity debugger with mona.py installed for exploit development, and a kali linux machine as the attacker. the setup allows safe practice of buffer overflow concepts required for oscp certification. Stack buffer overflow is a memory corruption vulnerability that occurs when a program writes more data to a buffer located on the stack than what is actually allocated for that buffer, therefore overflowing to a memory address that is outside of the intended data structure.
Oscp Detail Guide To Stack Based Buffer Overflow 6
Comments are closed.