Openvas Vulnerability Assessment Scanner Pptx

Openvas Vulnerability Scanner Be4sec Pdf Vulnerability Computing The document provides an overview of openvas, a vulnerability assessment scanner that highlights its importance, architecture, and functionality. it explains how to conduct vulnerability assessments using openvas, including setup, scanning targets, and exporting reports. Openvas (open vulnerability assessment system) is an open source framework for vulnerability scanning and management. it is designed to identify security issues in the network by performing comprehensive scans on the entire system and generating detailed reports on vulnerabilities found.
Setting Up And Using Openvas Vulnerability Scanner Learn about openvas, a vulnerability assessment system. covers architecture, features, lab generation, and network security. college level. Openvas • the open vulnerability assessment system (openvas) is a framework of several services and tools offering a comprehensive and powerful vulnerability scanning and vulnerability management solution. Openvas by greenbone openvas is a full featured vulnerability scanner. its capabilities include unauthenticated and authenticated testing, various high level and low level internet and industrial protocols, performance tuning for large scale scans and a powerful internal programming language to implement any type of vulnerability test. The scanner performs tests on the responses and compares these values against a database containing the os fingerprints e.g., examining the tcp options, the initial window size, etc. vulnerability assessment vulnerability assessment uses automated software to search for weaknesses (vulnerabilities) in a system.

Openvas Vulnerability Assessment Scanner Pptx Openvas by greenbone openvas is a full featured vulnerability scanner. its capabilities include unauthenticated and authenticated testing, various high level and low level internet and industrial protocols, performance tuning for large scale scans and a powerful internal programming language to implement any type of vulnerability test. The scanner performs tests on the responses and compares these values against a database containing the os fingerprints e.g., examining the tcp options, the initial window size, etc. vulnerability assessment vulnerability assessment uses automated software to search for weaknesses (vulnerabilities) in a system. Note: this guide provides practical openvas usage for penetration testing workflows. openvas (open vulnerability assessment system) is a comprehensive open source vulnerability scanning framework integrated into kali linux. In this article, we will walk you through the entire process of performing a full vulnerability scan with openvas, including the setup, configuration, and interpretation of results. Learn how openvas vulnerability scanner detects network security threats. step by step tutorial with installation, configuration, and scanning techniques. In this tutorial we will see how to perform a vulnerability assessment with openvas. the target on which we will perform this vulnerability assessment is again metasploitable.
Openvas Gvm Vulnerability Scanner Notes Noirchapeau S Gitbook Note: this guide provides practical openvas usage for penetration testing workflows. openvas (open vulnerability assessment system) is a comprehensive open source vulnerability scanning framework integrated into kali linux. In this article, we will walk you through the entire process of performing a full vulnerability scan with openvas, including the setup, configuration, and interpretation of results. Learn how openvas vulnerability scanner detects network security threats. step by step tutorial with installation, configuration, and scanning techniques. In this tutorial we will see how to perform a vulnerability assessment with openvas. the target on which we will perform this vulnerability assessment is again metasploitable.
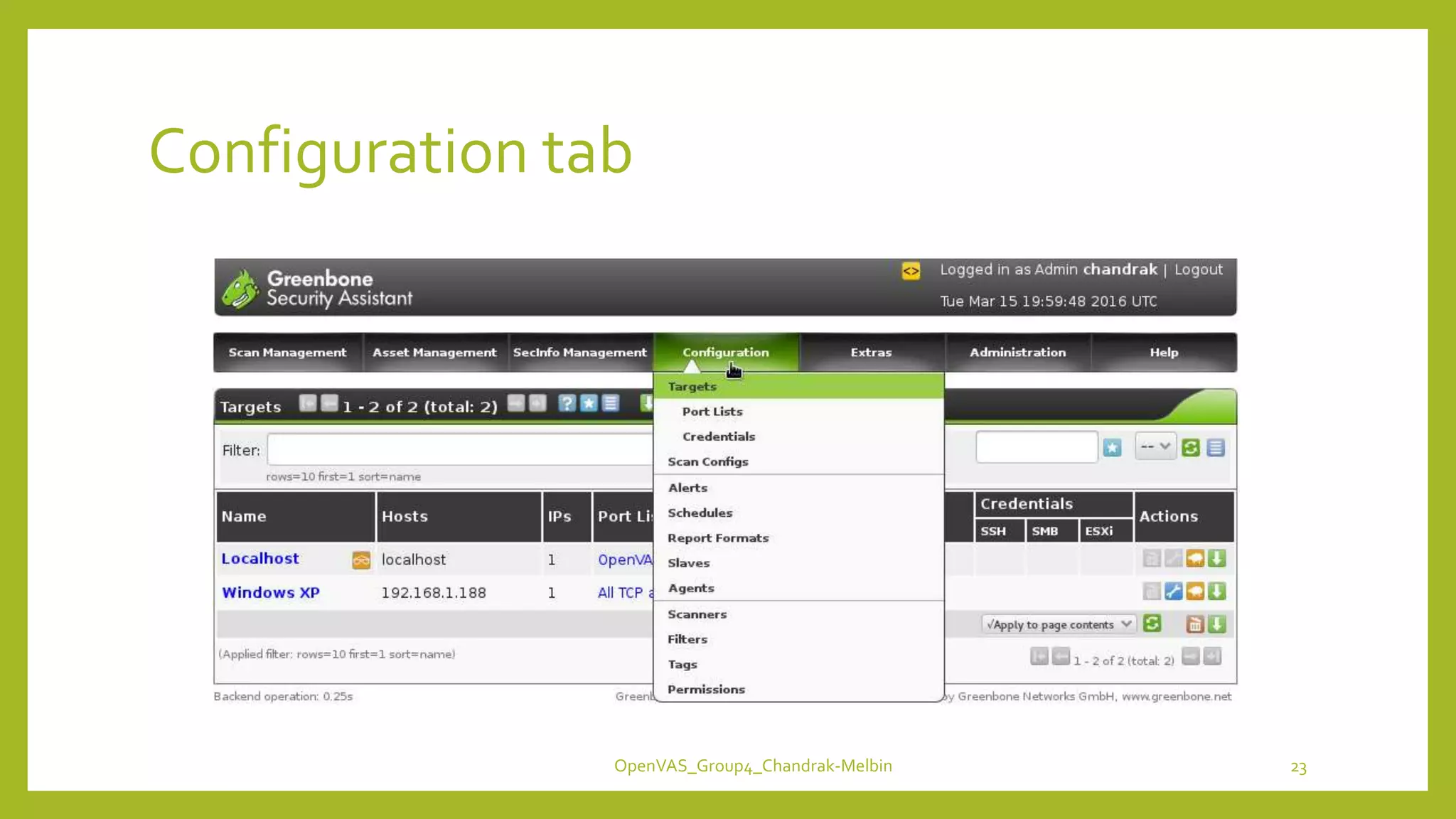
Openvas Vulnerability Assessment Scanner Pptx Learn how openvas vulnerability scanner detects network security threats. step by step tutorial with installation, configuration, and scanning techniques. In this tutorial we will see how to perform a vulnerability assessment with openvas. the target on which we will perform this vulnerability assessment is again metasploitable.
Comments are closed.