Openssl Data Encryption Lab Guide Pdf Encryption Cryptography

Cryptography Lab 1 Pdf Pdf Cryptography Secure Communication The document provides the steps to encrypt, decrypt, and view the encrypted and decrypted files to demonstrate openssl encryption and decryption from the command line. Seful for encryption and secure network communication. ssl stands for secure . ockets layer, a cryptographic communications protocol. this tutorial will demonstrate one way.

Lab 2 Secret Key Encryption Lab Pdf Cryptography Encryption In this lab, you will use openssl to encrypt and decrypt text messages. note: while openssl is the de facto cryptography library today, the use presented in this lab is not recommended for robust protection. According to the documentation, openssl is a cryptography toolkit implementing the secure sockets layer (ssl) and transport layer security (tls) network protocols and related cryptography standards required by them. Laboratory 02: des encryption using openssl this laboratory covers openssl tool applicability for des encryption. While many encryption algorithms can be used, this lab focuses on aes. to use aes to encrypt a text file directly from the command line using openssl, follow the steps below:.
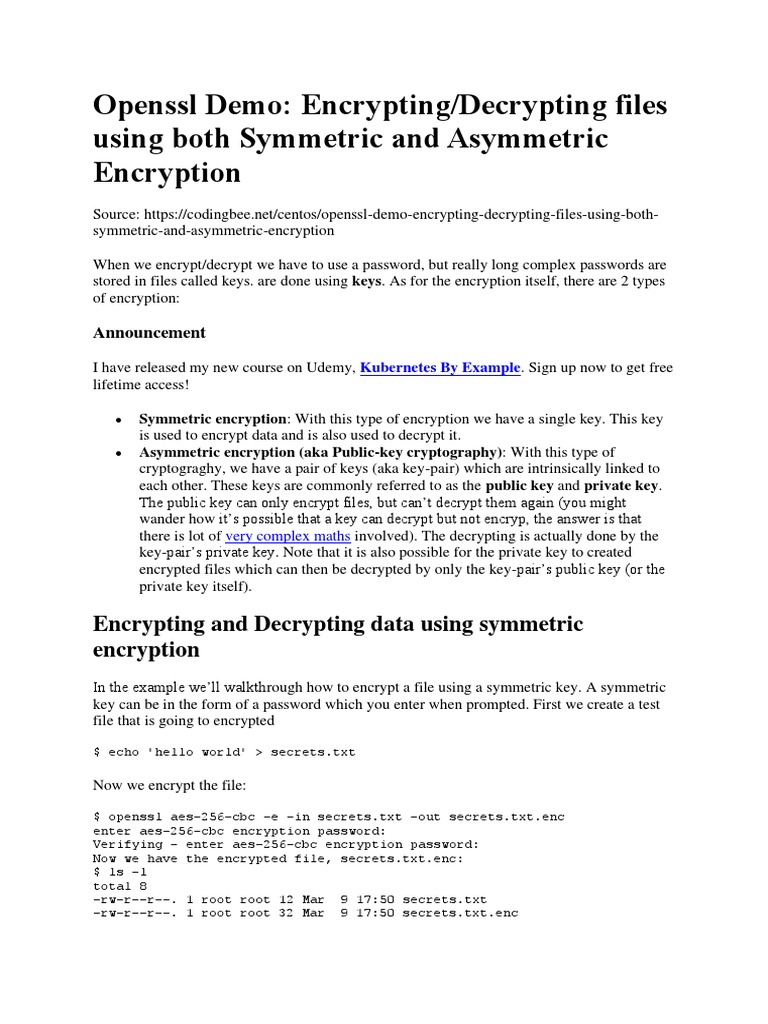
Prakt 8 Openssl Demo Encrypting Decrypting Files Using Both Symmetric Laboratory 02: des encryption using openssl this laboratory covers openssl tool applicability for des encryption. While many encryption algorithms can be used, this lab focuses on aes. to use aes to encrypt a text file directly from the command line using openssl, follow the steps below:. It discusses: 1) checking if openssl is already installed and how to install it if needed. 2) how to generate symmetric and asymmetric encryption keys in openssl and use them to encrypt decrypt files with des and rsa algorithms. In this lab, you will use openssl to encrypt and decrypt text messages. note: while openssl is the de facto cryptography library today, the use presented in this lab is not recommended for robust protection. Compare and contrast symmetric and asymmetric encryption systems and their vulnerability to various attacks. explain the role of third party agents in the provision of authentication services. comprehend and apply authentication, email security, web security services and mechanisms. discuss the effectiveness of passwords in access control. Writing tls client, server, and proxy program using python. explore public key cryptography, digital signature, certificate, and pki using openssl. write a program to implement the rsa algorithm, and use it to do encryption, decryption, signature generation and verification.

Cns 3 1 Lab Manual Pdf Encryption Cryptography It discusses: 1) checking if openssl is already installed and how to install it if needed. 2) how to generate symmetric and asymmetric encryption keys in openssl and use them to encrypt decrypt files with des and rsa algorithms. In this lab, you will use openssl to encrypt and decrypt text messages. note: while openssl is the de facto cryptography library today, the use presented in this lab is not recommended for robust protection. Compare and contrast symmetric and asymmetric encryption systems and their vulnerability to various attacks. explain the role of third party agents in the provision of authentication services. comprehend and apply authentication, email security, web security services and mechanisms. discuss the effectiveness of passwords in access control. Writing tls client, server, and proxy program using python. explore public key cryptography, digital signature, certificate, and pki using openssl. write a program to implement the rsa algorithm, and use it to do encryption, decryption, signature generation and verification.

Cryptography Lab Syllabus 6th Sem Pdf Cryptography Encryption Compare and contrast symmetric and asymmetric encryption systems and their vulnerability to various attacks. explain the role of third party agents in the provision of authentication services. comprehend and apply authentication, email security, web security services and mechanisms. discuss the effectiveness of passwords in access control. Writing tls client, server, and proxy program using python. explore public key cryptography, digital signature, certificate, and pki using openssl. write a program to implement the rsa algorithm, and use it to do encryption, decryption, signature generation and verification.
Comments are closed.