Openssh Openssh Verifyhostkeydns Issue Cve 2025 26465 Shorts
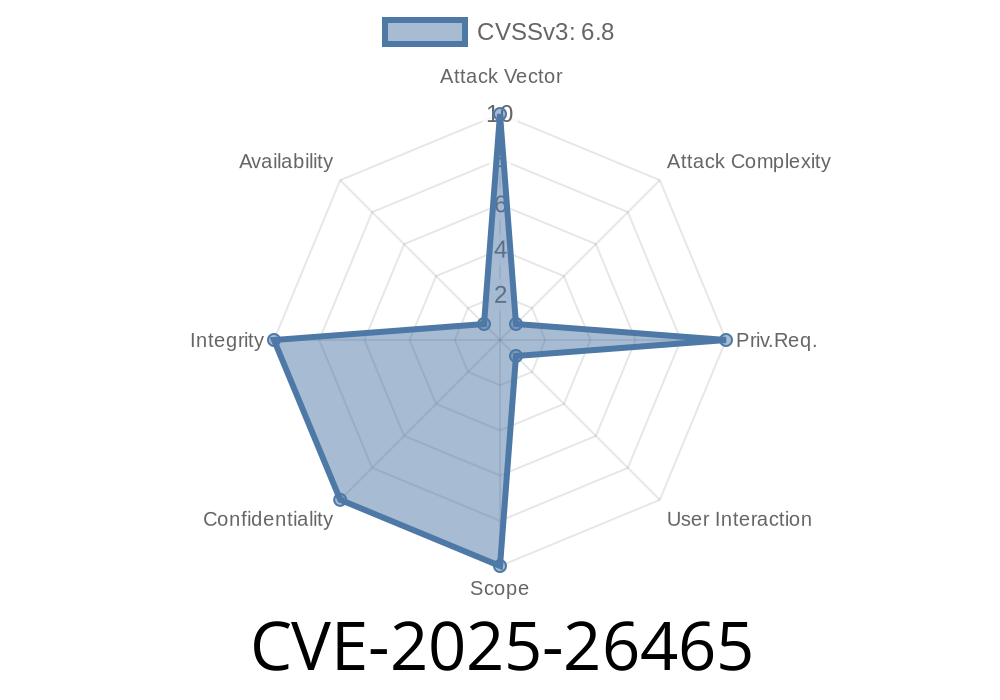
Cve 2025 26465 Openssh S Verifyhostkeydns Flaw Enables Complex **cve 2025 26465** is a vulnerability in certain openssh client versions (between 6.8p1 and 9.9p1) that can be exploited when the ssh configuration has the setting `verifyhostkeydns` set to either "yes" or "ask". In early 2025, a new security vulnerability was discovered in openssh. tracked as cve 2025 26465, this issue impacts openssh clients when the verifyhostkeydns option is turned on.
Cve 2025 26465 Openssh Vulnerability Allows Man In The Middle Attack Cve 2025–26465 allows an active machine in the middle attacker to impersonate legitimate servers by exploiting a flaw in openssh’s dns based host key verification. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server. this issue occurs due to how openssh mishandles error codes in specific conditions when verifying the host key. Enrichment data supplied by the nvd may require amendment due to these changes. a vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server. this issue occurs due to how openssh mishandles error codes in specific conditions when verifying the host key.
Cve 2025 26465 Openssh Vulnerability Allows Man In The Middle Attack Enrichment data supplied by the nvd may require amendment due to these changes. a vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server. this issue occurs due to how openssh mishandles error codes in specific conditions when verifying the host key. Cve 2025 26465: this vulnerability is caused by a logic flaw in openssh that could allow a man in the middle (mitm) attacker to impersonate a trusted server when the verifyhostkeydns option is enabled.by default, this option is disabled, which limits exposure in standard configurations. Cve 2025 26465 represents a significant security risk for users of openssh with the verifyhostkeydns option enabled. it is crucial to update to the patched versions of openssh to mitigate this vulnerability and ensure secure communications. Discovered by qualys tru, this vulnerability arises in the verifyhostkeydns component of openssh. an attacker can exploit this by impersonating a legitimate server, leading to a machine in the middle attack. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server.
Cve 2025 26465 Openssh Vulnerability Allows Man In The Middle Attack Cve 2025 26465: this vulnerability is caused by a logic flaw in openssh that could allow a man in the middle (mitm) attacker to impersonate a trusted server when the verifyhostkeydns option is enabled.by default, this option is disabled, which limits exposure in standard configurations. Cve 2025 26465 represents a significant security risk for users of openssh with the verifyhostkeydns option enabled. it is crucial to update to the patched versions of openssh to mitigate this vulnerability and ensure secure communications. Discovered by qualys tru, this vulnerability arises in the verifyhostkeydns component of openssh. an attacker can exploit this by impersonating a legitimate server, leading to a machine in the middle attack. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server.
Cve 2025 26465 Openssh Vulnerability Allows Man In The Middle Attack Discovered by qualys tru, this vulnerability arises in the verifyhostkeydns component of openssh. an attacker can exploit this by impersonating a legitimate server, leading to a machine in the middle attack. A vulnerability was found in openssh when the verifyhostkeydns option is enabled. a machine in the middle attack can be performed by a malicious machine impersonating a legit server.
Comments are closed.