Open Source Intelligence Osint Cycle Step By Step Guide

Open Source Intelligence Tools Osint Pdf Computing Cyberspace Recognize the various forms of open sources, such as public websites, social media, and other online sources. understanding how to use and gain access to various osint tools and techniques, such as search engines, social media scraping, and metadata analysis. The osint framework assists analysts in gathering & organizing open source information. learn the 5 steps of osint, sources, tools, and how to use it.
 - tools and techniques .webp)
Guide To Open Source Intelligence Osint Tools And Techniques Osint stands for open source intelligence where it is the process of gathering information from publicly available sources — legally and ethically, in order to analyse threats, investigate. This 24 tutorial series covers everything you need to master osint techniques, tools, and methodologies. our structured approach ensures you build solid fundamentals before advancing to complex investigations and professional applications. Osint framework started as a military tool but has grown into a vital intelligence gathering method used in many sectors. this piece showed you how a structured process turns public information into applicable information. Even though there are many different intelligence disciplines, variations of this cycle are present across all of them. in this blog, we will broadly discuss each step in the intelligence cycle and contextualize those steps in an open source intelligence (osint) workflow.

Osint The Most Comprehensive Guide On Open Source Intelligence Osint framework started as a military tool but has grown into a vital intelligence gathering method used in many sectors. this piece showed you how a structured process turns public information into applicable information. Even though there are many different intelligence disciplines, variations of this cycle are present across all of them. in this blog, we will broadly discuss each step in the intelligence cycle and contextualize those steps in an open source intelligence (osint) workflow. For beginners, getting this cycle down helps avoid info overload and keeps things ethical and effective. think of it like a recipe: skip steps, and your dish flops. this guide takes you through each phase with beginner friendly explanations, real world examples, and free tools. Open source intelligence (osint) is a method of gathering information from public or other open sources platforms like social media etc osint life cycle. Professionals rely on a structured methodology, often boiled down to five steps. is your research as rigorous as it should be? a robust osint investigation follows five main steps: define mission, gather sources, verify data, analyze relationships, and report insights. The workflow of an effective open source identification operation relies on the osint intelligence cycle. this cycle encompasses five critical steps, which are discussed below:.
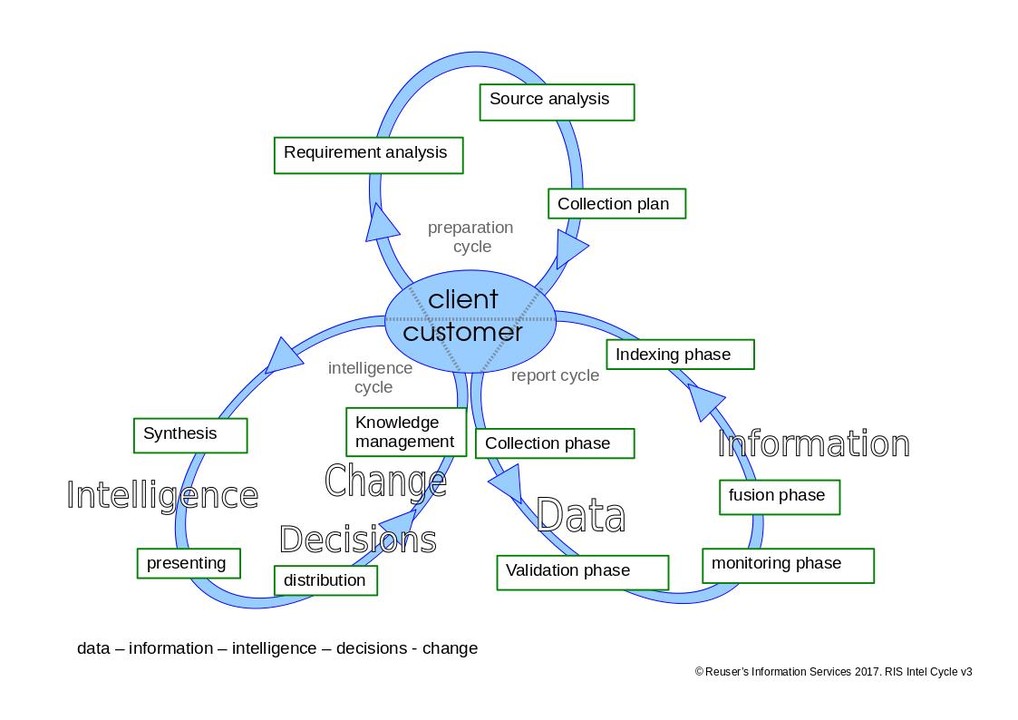
Ris Osint Open Source Intelligence Cycle For beginners, getting this cycle down helps avoid info overload and keeps things ethical and effective. think of it like a recipe: skip steps, and your dish flops. this guide takes you through each phase with beginner friendly explanations, real world examples, and free tools. Open source intelligence (osint) is a method of gathering information from public or other open sources platforms like social media etc osint life cycle. Professionals rely on a structured methodology, often boiled down to five steps. is your research as rigorous as it should be? a robust osint investigation follows five main steps: define mission, gather sources, verify data, analyze relationships, and report insights. The workflow of an effective open source identification operation relies on the osint intelligence cycle. this cycle encompasses five critical steps, which are discussed below:.

The Open Source Intelligence Osint Cycle Security Boulevard Professionals rely on a structured methodology, often boiled down to five steps. is your research as rigorous as it should be? a robust osint investigation follows five main steps: define mission, gather sources, verify data, analyze relationships, and report insights. The workflow of an effective open source identification operation relies on the osint intelligence cycle. this cycle encompasses five critical steps, which are discussed below:.

Open Source Intelligence Osint Powerpoint Presentation Slides Ppt
Comments are closed.