On Stream Prevent Github Actions Attacks

Github Actions Github I've opened the waitlist for those wanting to go deep in github actions for devops and ai automation. i'm so thrilled to announce this course. Publish block on vulnerabilities: prohibit the publication of github actions that fail these security checks, thus reducing the risk of supply chain attacks entering the marketplace.
Getting Started With Github Actions Github Build resilient github actions workflows with lessons from recent attacks. over the past three years, researchers have highlighted the risks associated with github actions. these threats became manifest with two recent incidents. “when creating workflows, custom actions, and composite actions actions, you should always consider whether your code might execute untrusted input from attackers. this can occur when an attacker adds malicious commands and scripts to a context. Learn from real world github actions exploits like the tj actions compromise and the pytorch runner attack. get practical hardening techniques, from pinning shas to securing runners. Master github actions security with expert best practices. learn how to protect your ci pipelines and prevent supply chain attacks. download the cheat sheet.
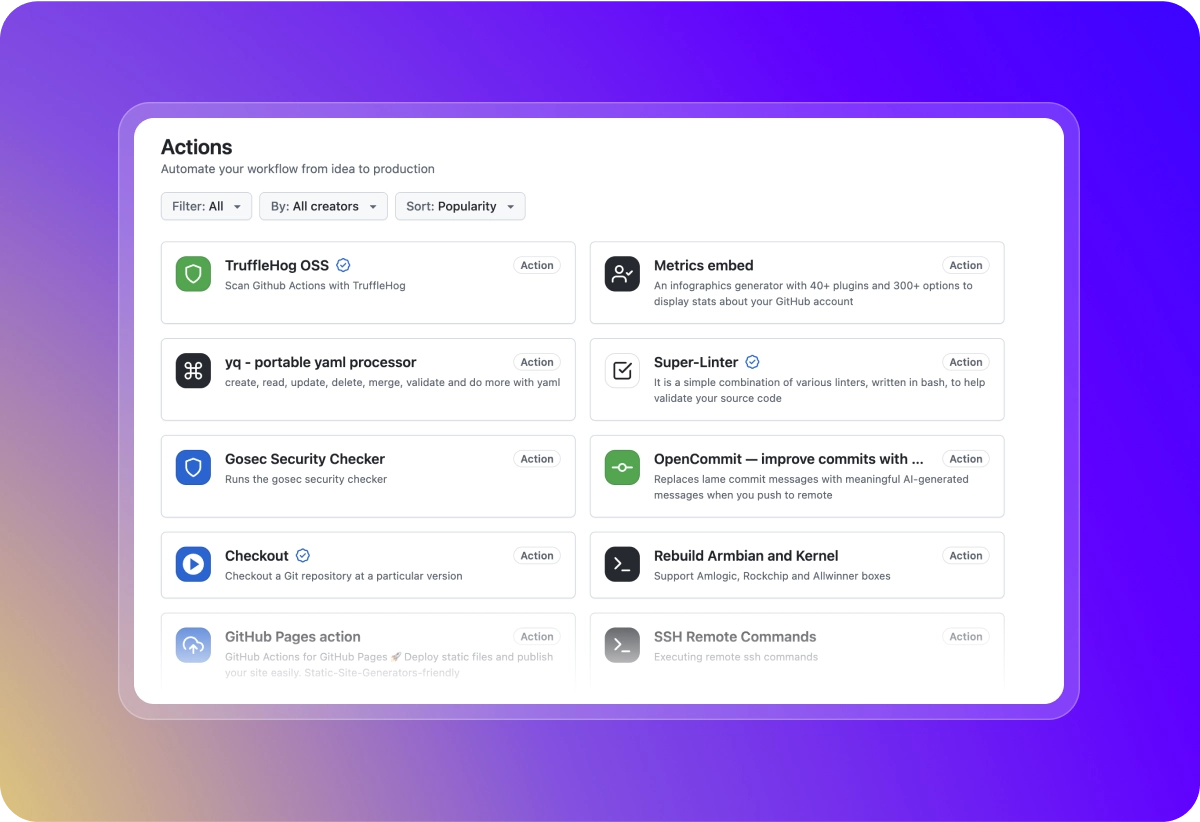
Getting Started With Github Actions Github Learn from real world github actions exploits like the tj actions compromise and the pytorch runner attack. get practical hardening techniques, from pinning shas to securing runners. Master github actions security with expert best practices. learn how to protect your ci pipelines and prevent supply chain attacks. download the cheat sheet. Github actions is a game changer, but security is your responsibility. treat your workflows like a fortress—gatekeep those secrets, vet your triggers, and always double check third party code. But did you know that github actions injections are one of the most common vulnerabilities in projects stored in github repositories? thankfully, this is a relatively easy vulnerability to address, and github has some tools to make it even easier. Understand the risks of github actions in public repositories and learn how to implement best practices to safeguard your ci cd environment from vulnerabilities and attacks. Third party “actions” enhance workflow automation, but they can pose security risks. for example, the popular github action “ tj actions cha nged files” action was recently compromised, potentially exposing sensitive data. in this blog post, we’ll provide hands on tips to help you reduce such risks.
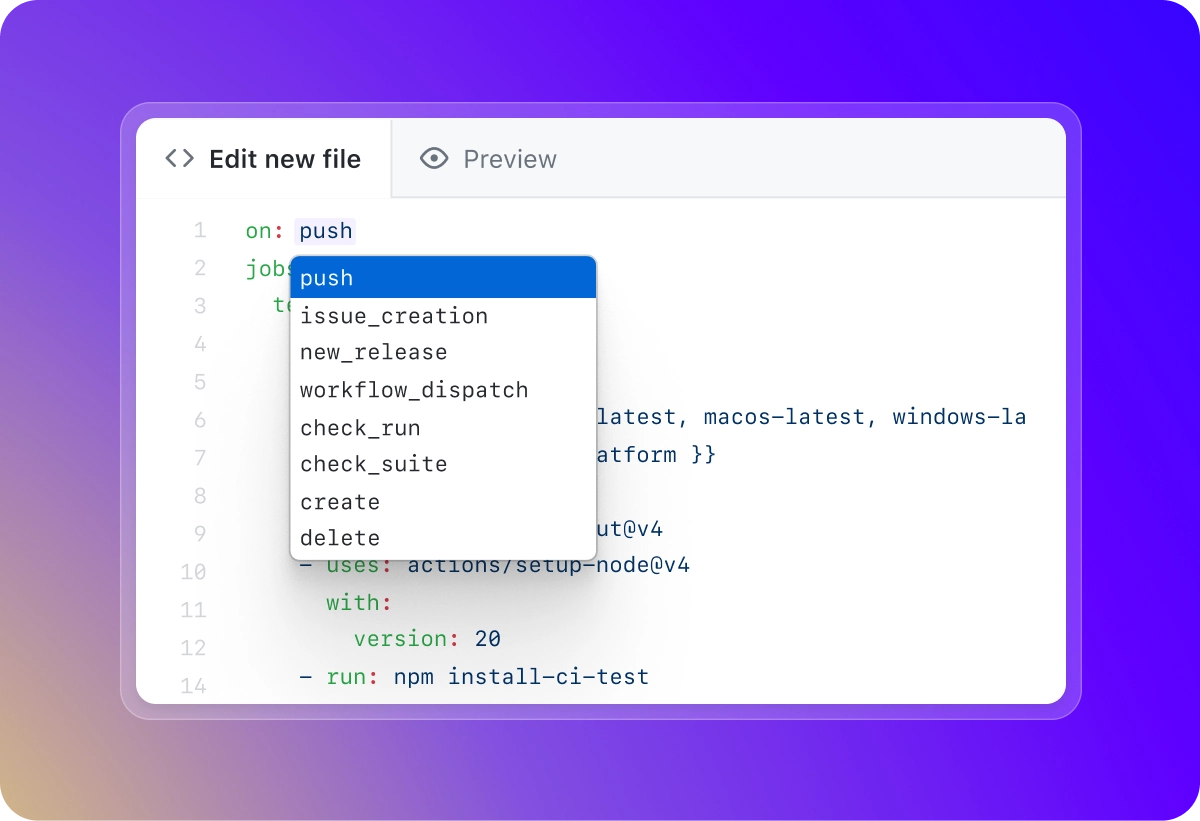
Getting Started With Github Actions Github Github actions is a game changer, but security is your responsibility. treat your workflows like a fortress—gatekeep those secrets, vet your triggers, and always double check third party code. But did you know that github actions injections are one of the most common vulnerabilities in projects stored in github repositories? thankfully, this is a relatively easy vulnerability to address, and github has some tools to make it even easier. Understand the risks of github actions in public repositories and learn how to implement best practices to safeguard your ci cd environment from vulnerabilities and attacks. Third party “actions” enhance workflow automation, but they can pose security risks. for example, the popular github action “ tj actions cha nged files” action was recently compromised, potentially exposing sensitive data. in this blog post, we’ll provide hands on tips to help you reduce such risks.
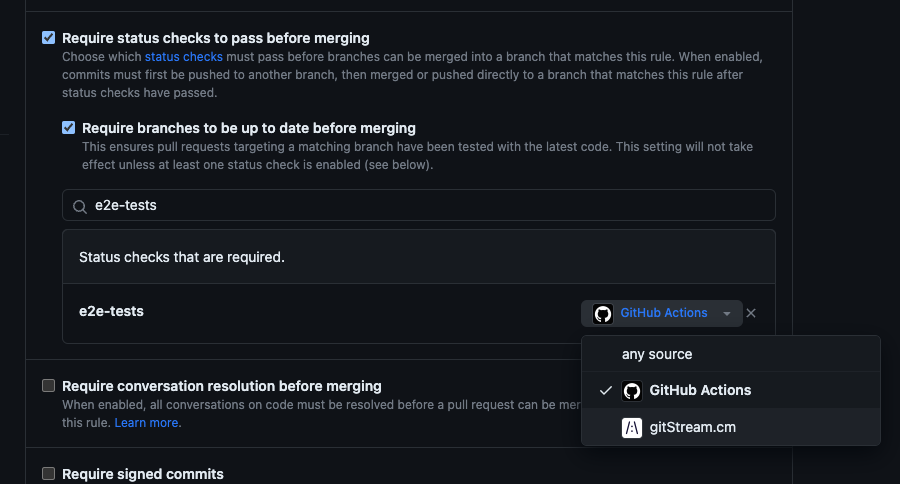
Integrate Gitstream With Github Actions Gitstream Documentation Understand the risks of github actions in public repositories and learn how to implement best practices to safeguard your ci cd environment from vulnerabilities and attacks. Third party “actions” enhance workflow automation, but they can pose security risks. for example, the popular github action “ tj actions cha nged files” action was recently compromised, potentially exposing sensitive data. in this blog post, we’ll provide hands on tips to help you reduce such risks.
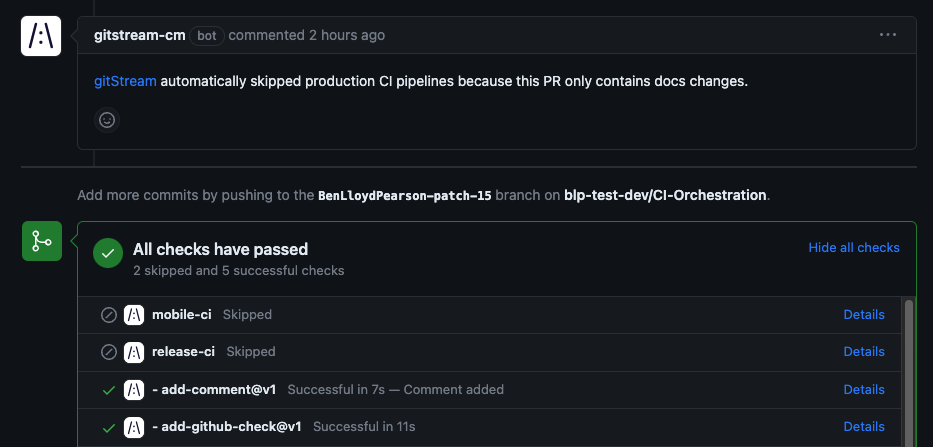
Integrate Gitstream With Github Actions Gitstream Documentation
Comments are closed.