Obiee 12c Security

Obiee 12c Pdf Oracle Database Command Line Interface Oracle business intelligence 12c is tightly integrated with the oracle fusion middleware security architecture and delegates core security functionality to components of that architecture. This is the first blog in a series which demonstrates security features and design choices that can made when building your secure oracle business intelligence system.

Obiee 12c Features Pdf Business Intelligence Backup Here comes the part that is familiar to every obiee administrator, the rpd modifications. if you are following the document, the sample ebs connection pool can be used or create a new one just for the initialization process and retrieving security. This chapter introduces the oracle business intelligence security model, discusses the tools used to configure security, and provides a detailed road map for configuring security in oracle business intelligence. December 2015 explains how to configure oracle business intelligence enterprise edition security, including settings for sso, ssl, external authentication, and presentation services privileges. The document outlines the high level steps to enable ssl for obiee 12c, including generating certificates and keystores, configuring weblogic servers for ssl, configuring the internal ldap to use ldaps, configuring trust stores, and disabling the http port.

Obiee 12c Installation Guide Pdf Zip File Format Oracle Corporation December 2015 explains how to configure oracle business intelligence enterprise edition security, including settings for sso, ssl, external authentication, and presentation services privileges. The document outlines the high level steps to enable ssl for obiee 12c, including generating certificates and keystores, configuring weblogic servers for ssl, configuring the internal ldap to use ldaps, configuring trust stores, and disabling the http port. Obiee security is defined by the use of a role based access control model. it is defined in terms of roles that are aligned to different directory server groups and users. This blog series so far has reviewed the basics of obiee security, the following questions should be included in any discussion of about the security of an obiee implementation. Explains how to configure oracle business intelligence enterprise edition security, including settings for sso, ssl, external authentication, and presentation services privileges. The oracle business intelligence release 11g and release 12c security models differ in the following ways:.
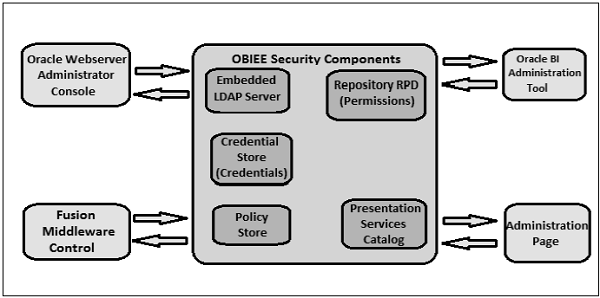
Girish Srivastava Obiee Security Obiee security is defined by the use of a role based access control model. it is defined in terms of roles that are aligned to different directory server groups and users. This blog series so far has reviewed the basics of obiee security, the following questions should be included in any discussion of about the security of an obiee implementation. Explains how to configure oracle business intelligence enterprise edition security, including settings for sso, ssl, external authentication, and presentation services privileges. The oracle business intelligence release 11g and release 12c security models differ in the following ways:.
Comments are closed.