Oauth2 Implicit Flow Argus Documentation
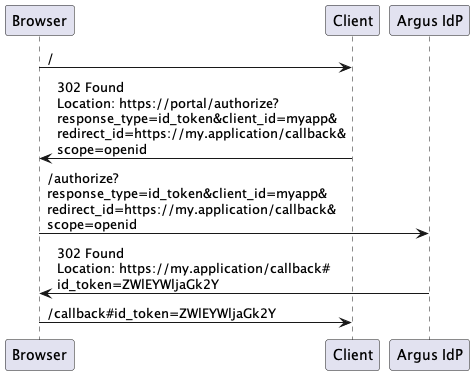
Oauth2 Implicit Flow Argus Documentation The client application can decode and verify the id token, which is signed by argus idp. this will contain claims about the user, which the client can trust to authenticate the user, and use information in the claims to determine user permissions or behaviour. The microsoft identity platform supports the oauth 2.0 implicit grant flow as described in the oauth 2.0 specification. the defining characteristic of the implicit grant is that tokens (id tokens or access tokens) are returned directly from the authorize endpoint instead of the token endpoint.

Oauth2 Implicit Grant Flow Diagram Iteritory The oauth 2.0 security best current practice document recommends against using the implicit flow entirely, and oauth 2.0 for browser based apps describes the technique of using the authorization code flow with pkce instead. In this article, i intend to introduce you with oauth 2's implicit grant flow, its security implications, and why it's no longer considered as best practice. The microsoft identity platform supports the oauth 2.0 implicit grant flow as described in the oauth 2.0 specification. the defining characteristic of the implicit grant is that tokens (id tokens or access tokens) are returned directly from the authorize endpoint instead of the token endpoint. Oauth 2.0 provides different flows depending on the type of application and security requirements. one of the earlier flows designed for browser based applications was the implicit flow.

Oauth V2 Implicit Flow The microsoft identity platform supports the oauth 2.0 implicit grant flow as described in the oauth 2.0 specification. the defining characteristic of the implicit grant is that tokens (id tokens or access tokens) are returned directly from the authorize endpoint instead of the token endpoint. Oauth 2.0 provides different flows depending on the type of application and security requirements. one of the earlier flows designed for browser based applications was the implicit flow. Argus can act as an openid oauth2 provider for external applications. please see argus identity provider integration guide for details. This guide addresses how to set up argus to be an oauth2 or openid connect identity provider for your application. to set up argus to use an external openid provider for authentication into argus, see argus identity provider integration guide. Oauth2 implicit flow is not recommended, as its security properties are weak. if your client supports authorization code flow, use this instead. an argus oauth2 client is bound to a required role (requiredfunction), which the user must have granted in order to be authorized to use the client. Oauth2 integration.
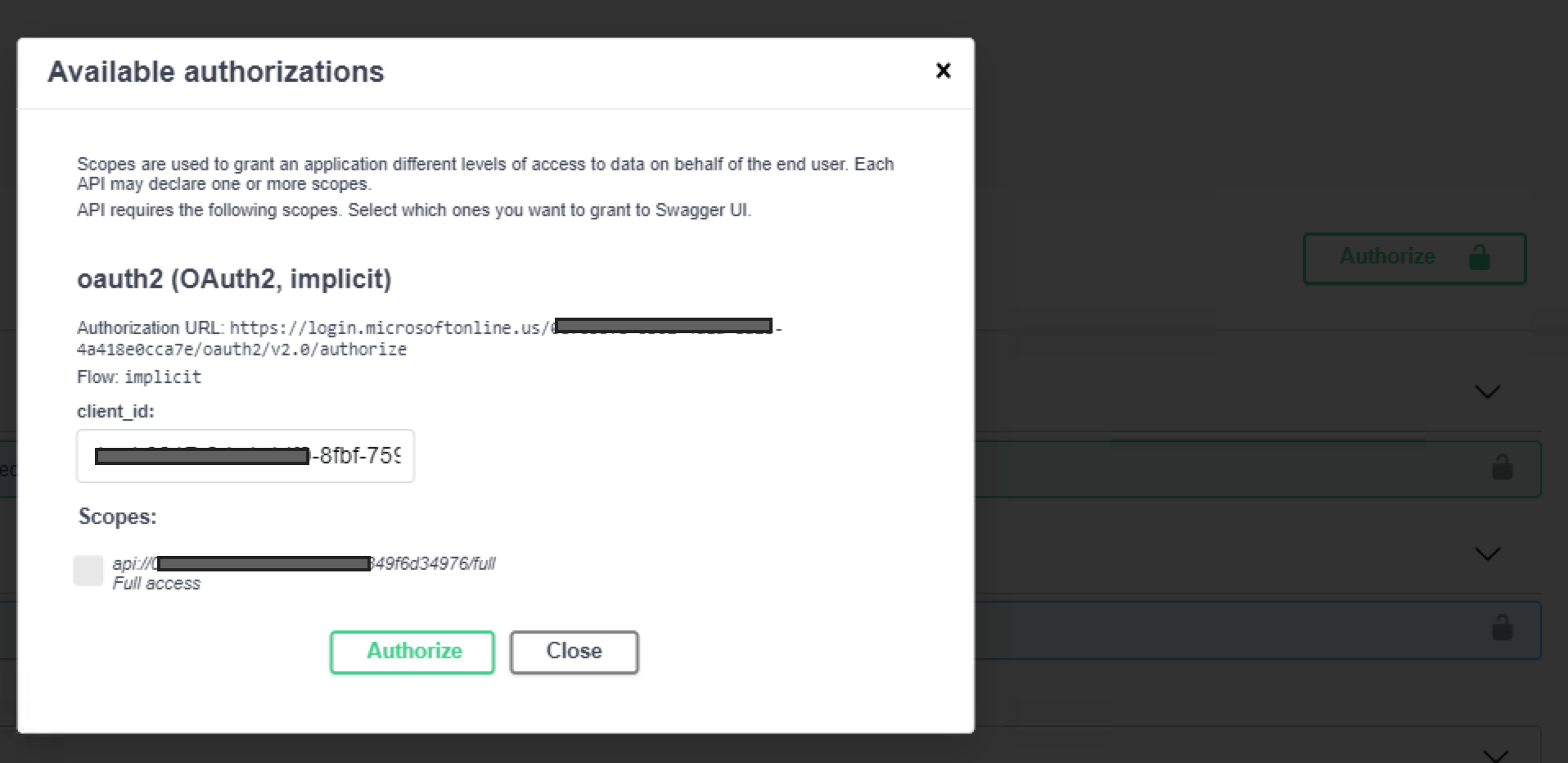
Configure Oauth2 Implicit Flow For Swagger Ui Taithienbo Argus can act as an openid oauth2 provider for external applications. please see argus identity provider integration guide for details. This guide addresses how to set up argus to be an oauth2 or openid connect identity provider for your application. to set up argus to use an external openid provider for authentication into argus, see argus identity provider integration guide. Oauth2 implicit flow is not recommended, as its security properties are weak. if your client supports authorization code flow, use this instead. an argus oauth2 client is bound to a required role (requiredfunction), which the user must have granted in order to be authorized to use the client. Oauth2 integration.
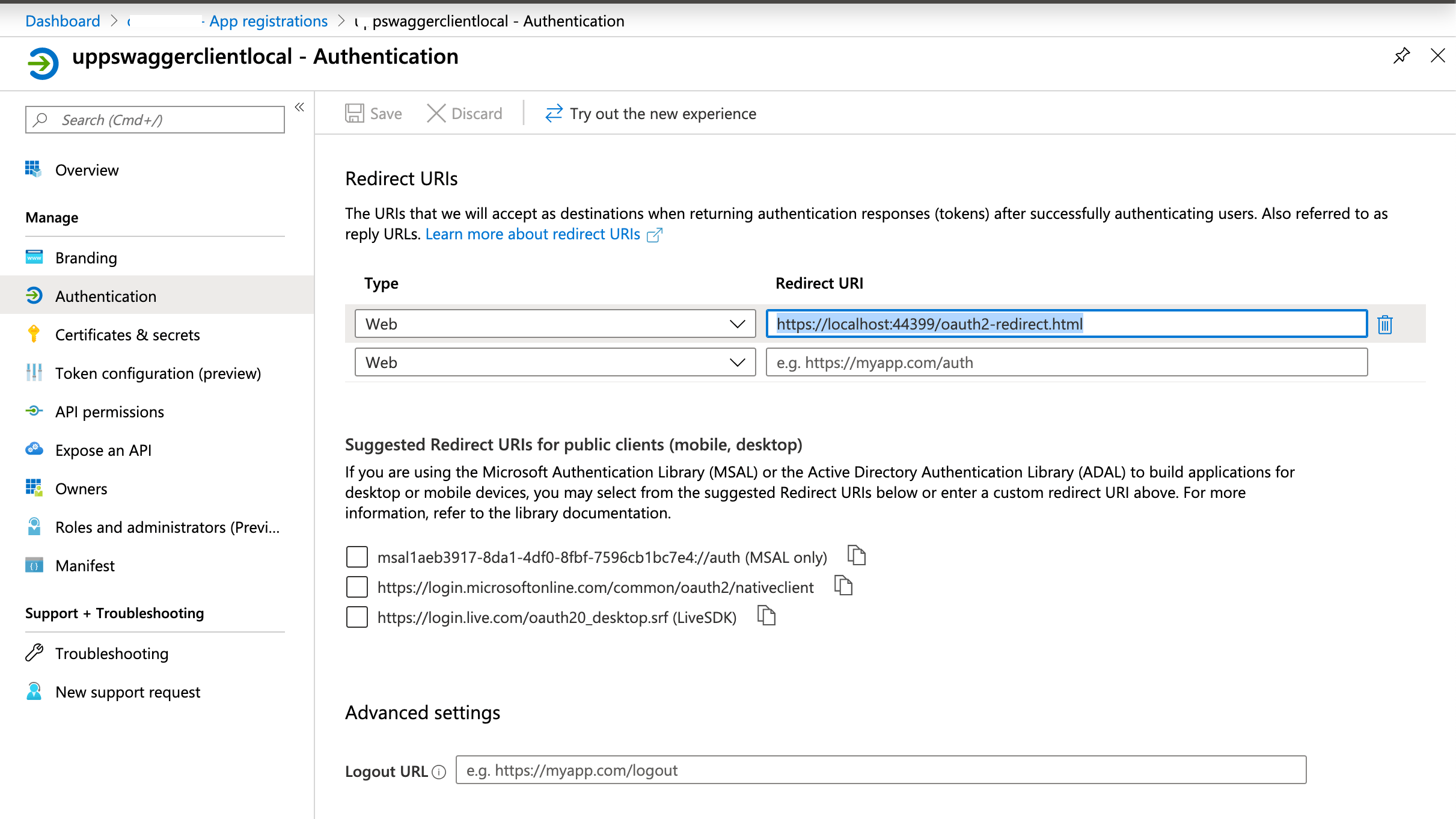
Configure Oauth2 Implicit Flow For Swagger Ui Taithienbo Oauth2 implicit flow is not recommended, as its security properties are weak. if your client supports authorization code flow, use this instead. an argus oauth2 client is bound to a required role (requiredfunction), which the user must have granted in order to be authorized to use the client. Oauth2 integration.
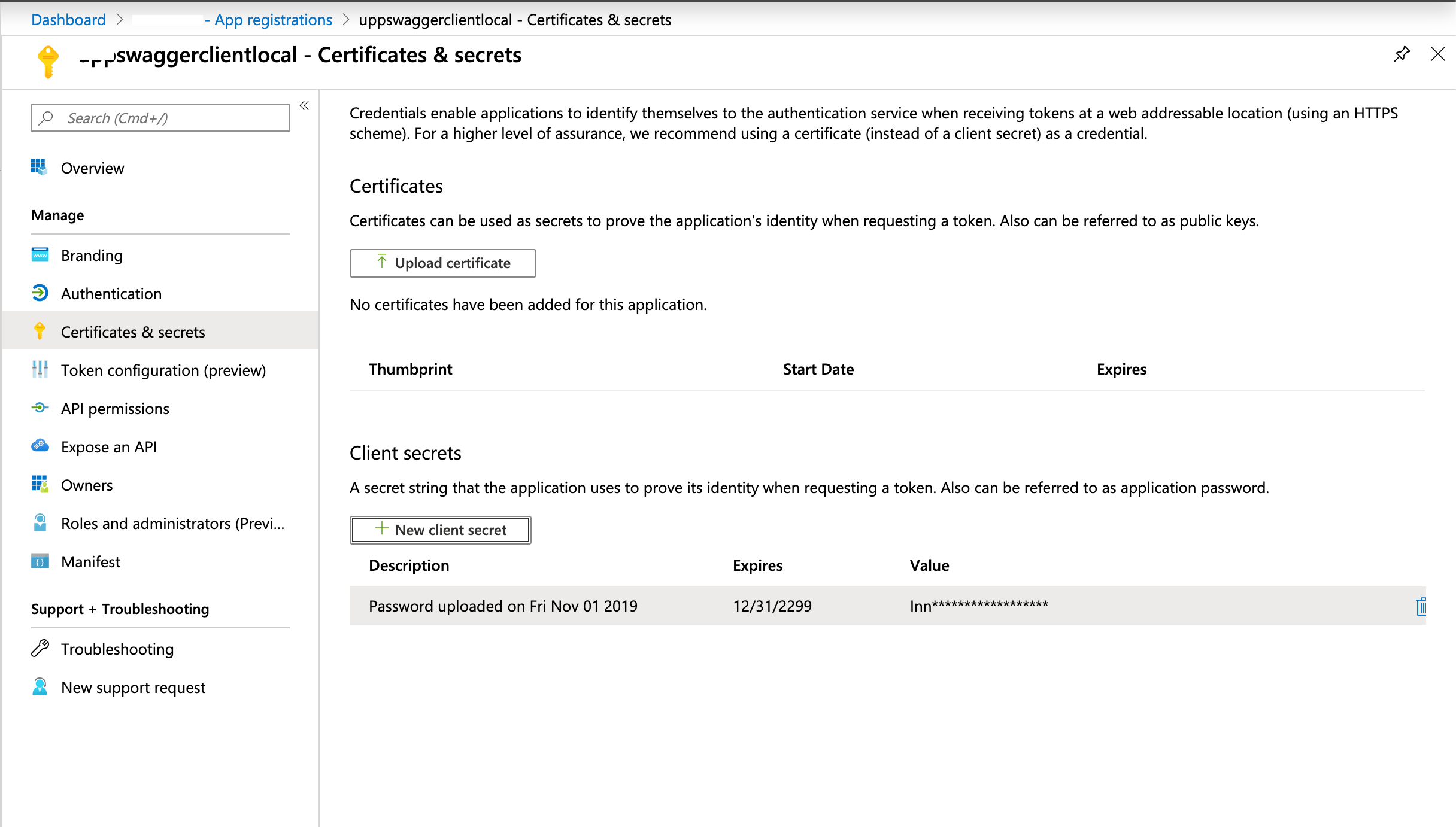
Configure Oauth2 Implicit Flow For Swagger Ui Taithienbo
Comments are closed.