Oauth Login Ozdentity
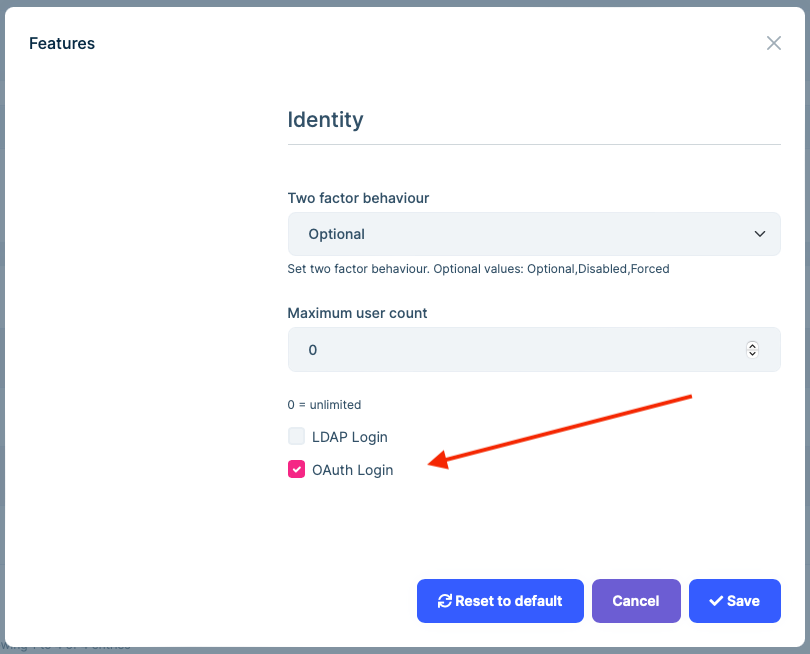
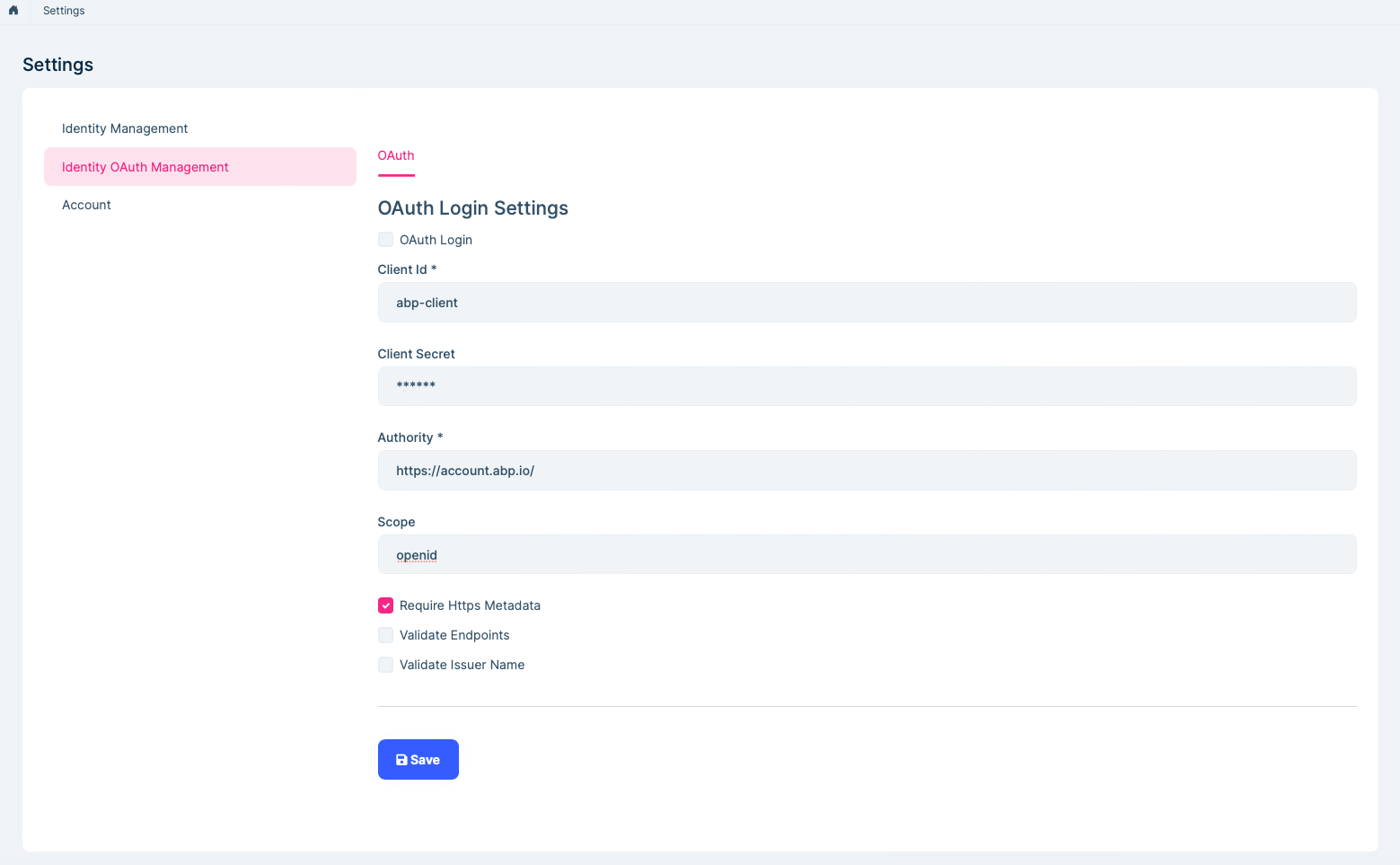
Oauth Login Ozdentity You need to enable the oauth login feature and configure related settings. then you can enter the user name and password on the login page for oauth external login. Authenticate users across all of your applications & apis with standards like ldap, oauth, oidc and two factor authentication (2fa). our enterprise identity & access management is comprehensive solution to manage your application security, privileged access and web api safeguarding.
Oauth Login Ozdentity The oauth 2.0 authorization code flow is described in section 4.1 of the oauth 2.0 specification. apps using the oauth 2.0 authorization code flow acquire an access token to include in requests to resources protected by the microsoft identity platform (typically apis). Ozdentity. Menu getting started add application identity two factor authentication ldap oauth login import external users. To begin, obtain oauth 2.0 client credentials from the google api console. then your client application requests an access token from the google authorization server, extracts a token from the.
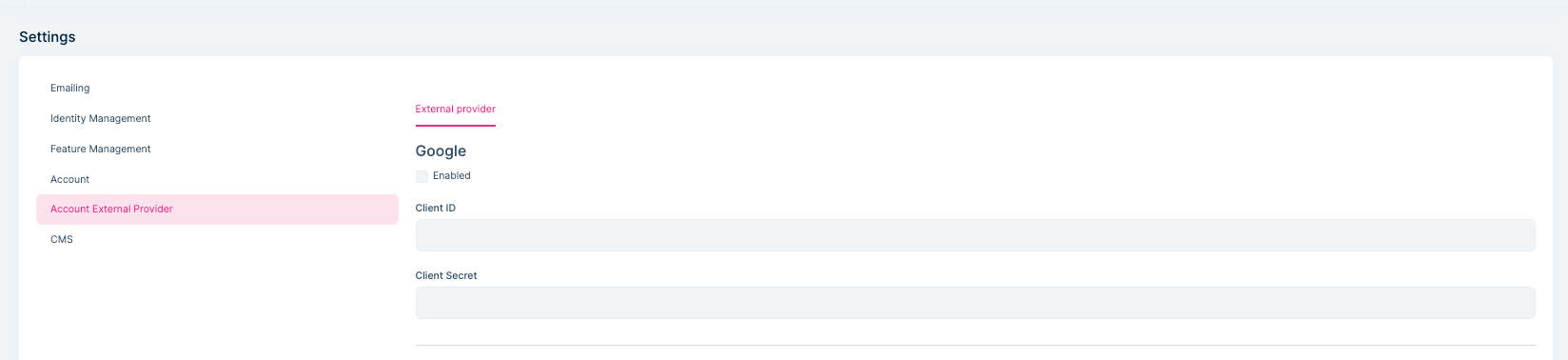
Oauth Login Ozdentity Menu getting started add application identity two factor authentication ldap oauth login import external users. To begin, obtain oauth 2.0 client credentials from the google api console. then your client application requests an access token from the google authorization server, extracts a token from the. Youu need to enable the ldap login feature and configure related settings. then you can enter the ldap user name and password on the login page for external login. It implements oauth resource owner password authentication and gets user info for external login. how to enable oauth external login? you need to enable the oauth login feature and configure related settings. then you can enter the user name and password oauth login read more ». Oauth 2.0 is the industry standard protocol for authorization. oauth 2.0 focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices. Integrating ldap authentication with an on premise ozdentity idp provides a robust solution for organizations that want to leverage their existing ldap active directory infrastructure while adopting modern identity and access management practices.
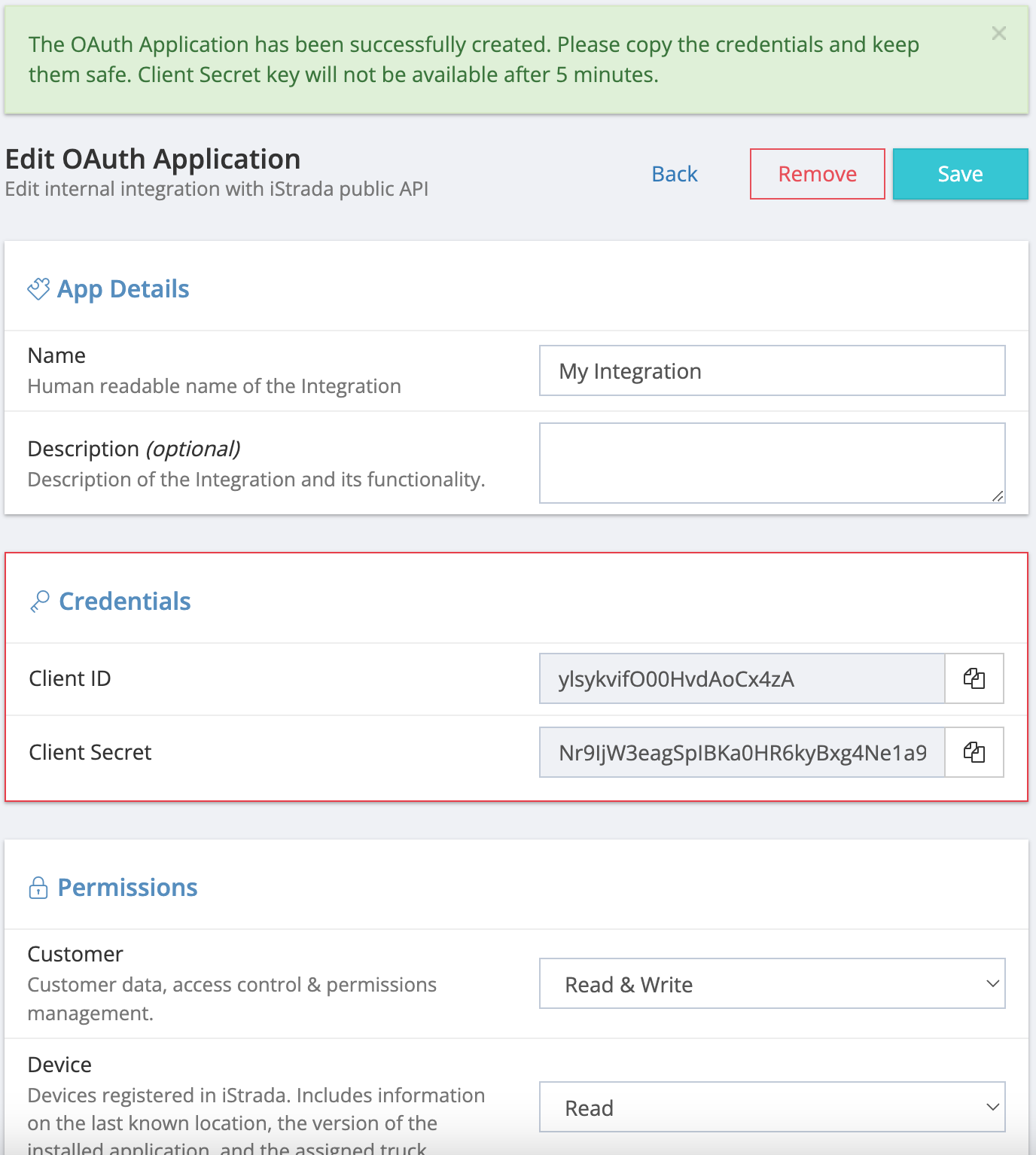
Creating Deliverygo Oauth App Sysdyne Cloud Api Youu need to enable the ldap login feature and configure related settings. then you can enter the ldap user name and password on the login page for external login. It implements oauth resource owner password authentication and gets user info for external login. how to enable oauth external login? you need to enable the oauth login feature and configure related settings. then you can enter the user name and password oauth login read more ». Oauth 2.0 is the industry standard protocol for authorization. oauth 2.0 focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices. Integrating ldap authentication with an on premise ozdentity idp provides a robust solution for organizations that want to leverage their existing ldap active directory infrastructure while adopting modern identity and access management practices.

Oauth Poozle Docs Oauth 2.0 is the industry standard protocol for authorization. oauth 2.0 focuses on client developer simplicity while providing specific authorization flows for web applications, desktop applications, mobile phones, and living room devices. Integrating ldap authentication with an on premise ozdentity idp provides a robust solution for organizations that want to leverage their existing ldap active directory infrastructure while adopting modern identity and access management practices.
Comments are closed.