Oauth Authorization Code With Implicit Grant Flow Iteritory

Oauth Authorization Code With Implicit Grant Flow Iteritory The microsoft identity platform supports the oauth 2.0 implicit grant flow as described in the oauth 2.0 specification. the defining characteristic of the implicit grant is that tokens (id tokens or access tokens) are returned directly from the authorize endpoint instead of the token endpoint. This tutorial will help you understand oauth2 implicit grant flow. the oauth 2 implicit grant flow is an oauth flow that web or app based clients use to access a restricted api and the client side apps are incapable of storing information securely.
Redirecting The implicit grant and hybrid flow aren't as secure as other oauth flows. unless absolutely required, you shouldn’t allow an access or id token to be issued when requested using implicit grant or hybrid flow in your app registration. This tutorial walks through how to use the oauth implicit code grant. for more information on the implicit grant, see use an implicit grant. The oauth 2.0 security best current practice document recommends against using the implicit flow entirely, and oauth 2.0 for browser based apps describes the technique of using the authorization code flow with pkce instead. For most of the history of oauth 2.0, the implicit flow was the recommended way to build single page apps. with the removal of third party cookies and greater attention paid to security concerns around the implicit flow, we've moved to the authorization code flow for single page apps.

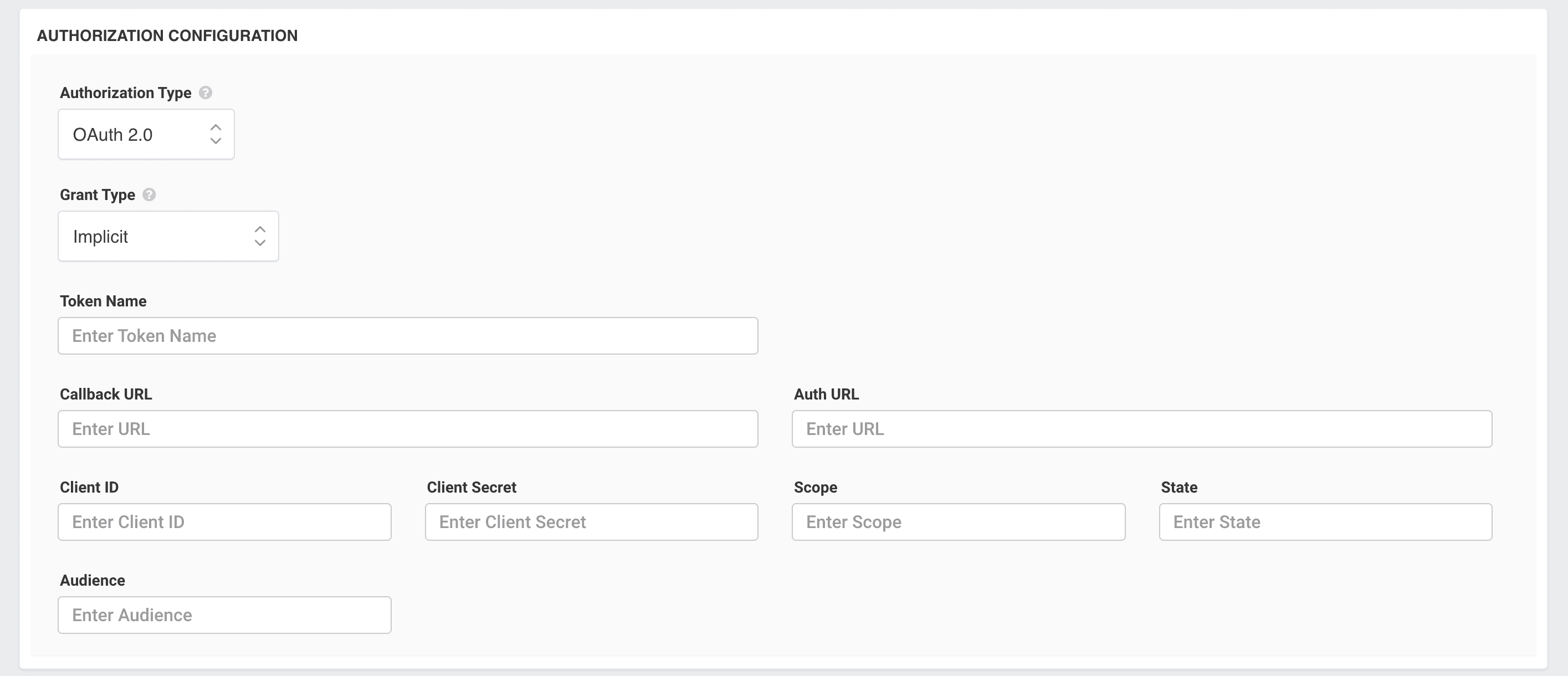
Tutorial On Understanding Oauth2 Implicit Grant Flow The oauth 2.0 security best current practice document recommends against using the implicit flow entirely, and oauth 2.0 for browser based apps describes the technique of using the authorization code flow with pkce instead. For most of the history of oauth 2.0, the implicit flow was the recommended way to build single page apps. with the removal of third party cookies and greater attention paid to security concerns around the implicit flow, we've moved to the authorization code flow for single page apps. Servicenow instances support the implicit grant of an access token. the implicit grant type, also known as implicit grant code flow, allows the access token to be given directly to the client application via the user agent, which is typically the web browser or mobile device. The implicit grant is similar to the authorization code grant with two distinct differences. it is intended to be used for user agent based clients (e.g. single page web apps) that can’t keep a client secret because all of the application code and storage is easily accessible. Implement authorization by grant type this guide explains how to implement an oauth 2.0 implicit flow for your app with okta. This implicit grant type authorization example describes the authorization flow for applications that are implemented in a web browser using a scripting language such as javascript or implemented on a mobile device.
Comments are closed.