Oauth 2 0 Rest Api User Guide

Securing Rest Apis The Role Of Oauth 2 0 In Authorization Learn how to implement oauth 2.0 for secure rest apis, covering key components, flows, and best practices for token management. If you’re building or working with rest apis, understanding oauth 2.0 is no longer optional—it’s a critical competency. this visual guide will walk you through oauth 2.0 implementation for rest apis, breaking down complex concepts into digestible, visual explanations.
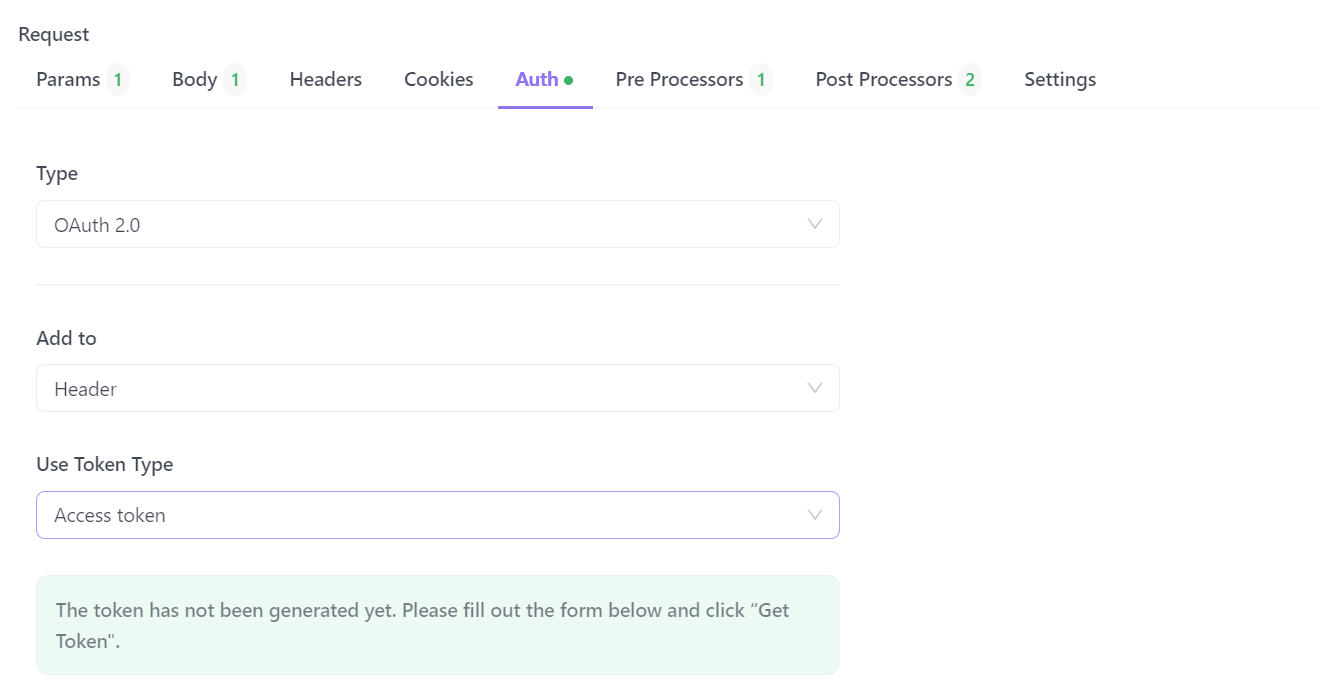
Securing Rest Apis The Role Of Oauth 2 0 In Authorization Oauth 2.0 requests are usually authenticated with an access token, which is passed as bearer token. to use this access token, you need to construct a normal http request and include it in an authorization header along with the value of bearer. This article will walk you through the implementation of oauth 2.0 for secure rest api authentication. we'll cover the oauth 2.0 flow, client registration, and authorization code grant, providing a step by step guide for developers to implement secure authentication in their apis. For an interactive demonstration of using oauth 2.0 with google (including the option to use your own client credentials), experiment with the oauth 2.0 playground. Setting up oauth 2.0 for your rest api involves several important steps to ensure a secure and efficient authentication system. below, we break down the key components you’ll need to.
Securing Rest Apis The Role Of Oauth 2 0 In Authorization For an interactive demonstration of using oauth 2.0 with google (including the option to use your own client credentials), experiment with the oauth 2.0 playground. Setting up oauth 2.0 for your rest api involves several important steps to ensure a secure and efficient authentication system. below, we break down the key components you’ll need to. The following sequence diagram illustrates a basic example of the oauth 2.0 authorization flow to access the identity domains rest api. use specific oauth 2.0 parameters when working with an identity domain. Oauth 2.0 is an authorization protocol that gives an api client limited access to user data on a web server. github, google, and facebook apis notably use it. oauth relies on authentication scenarios called flows, which allow the resource owner (user) to share the protected content from the resource server without sharing their credentials. Learn how to implement oauth 2.0 for secure authentication and authorization with zoho mail rest apis. step by step guide covering client registration, token management, and access to zoho resources. For an external client app or connected app to request access, it must be integrated with your org’s rest api using the oauth 2.0 protocol. oauth 2.0 is an open protocol that authorizes secure data sharing between applications through the exchange of tokens.

Implementing Oauth 2 0 In Rest Apis Complete Guide The following sequence diagram illustrates a basic example of the oauth 2.0 authorization flow to access the identity domains rest api. use specific oauth 2.0 parameters when working with an identity domain. Oauth 2.0 is an authorization protocol that gives an api client limited access to user data on a web server. github, google, and facebook apis notably use it. oauth relies on authentication scenarios called flows, which allow the resource owner (user) to share the protected content from the resource server without sharing their credentials. Learn how to implement oauth 2.0 for secure authentication and authorization with zoho mail rest apis. step by step guide covering client registration, token management, and access to zoho resources. For an external client app or connected app to request access, it must be integrated with your org’s rest api using the oauth 2.0 protocol. oauth 2.0 is an open protocol that authorizes secure data sharing between applications through the exchange of tokens.

Implementing Oauth 2 0 In Rest Apis Complete Guide Learn how to implement oauth 2.0 for secure authentication and authorization with zoho mail rest apis. step by step guide covering client registration, token management, and access to zoho resources. For an external client app or connected app to request access, it must be integrated with your org’s rest api using the oauth 2.0 protocol. oauth 2.0 is an open protocol that authorizes secure data sharing between applications through the exchange of tokens.

Implementing Oauth 2 0 In Rest Apis Complete Guide
Comments are closed.