Oauth 2 0 Explained In 60 Seconds

Oauth 2 0 Explained With Examples How Does It Work Learn oauth 2.0 in just 60 seconds! this concise tutorial explains the basics of oauth 2.0, a widely used authorization framework that enables secure data ex. Learn everything you need to know about oauth: what it is, what problem it solves, and how it works.
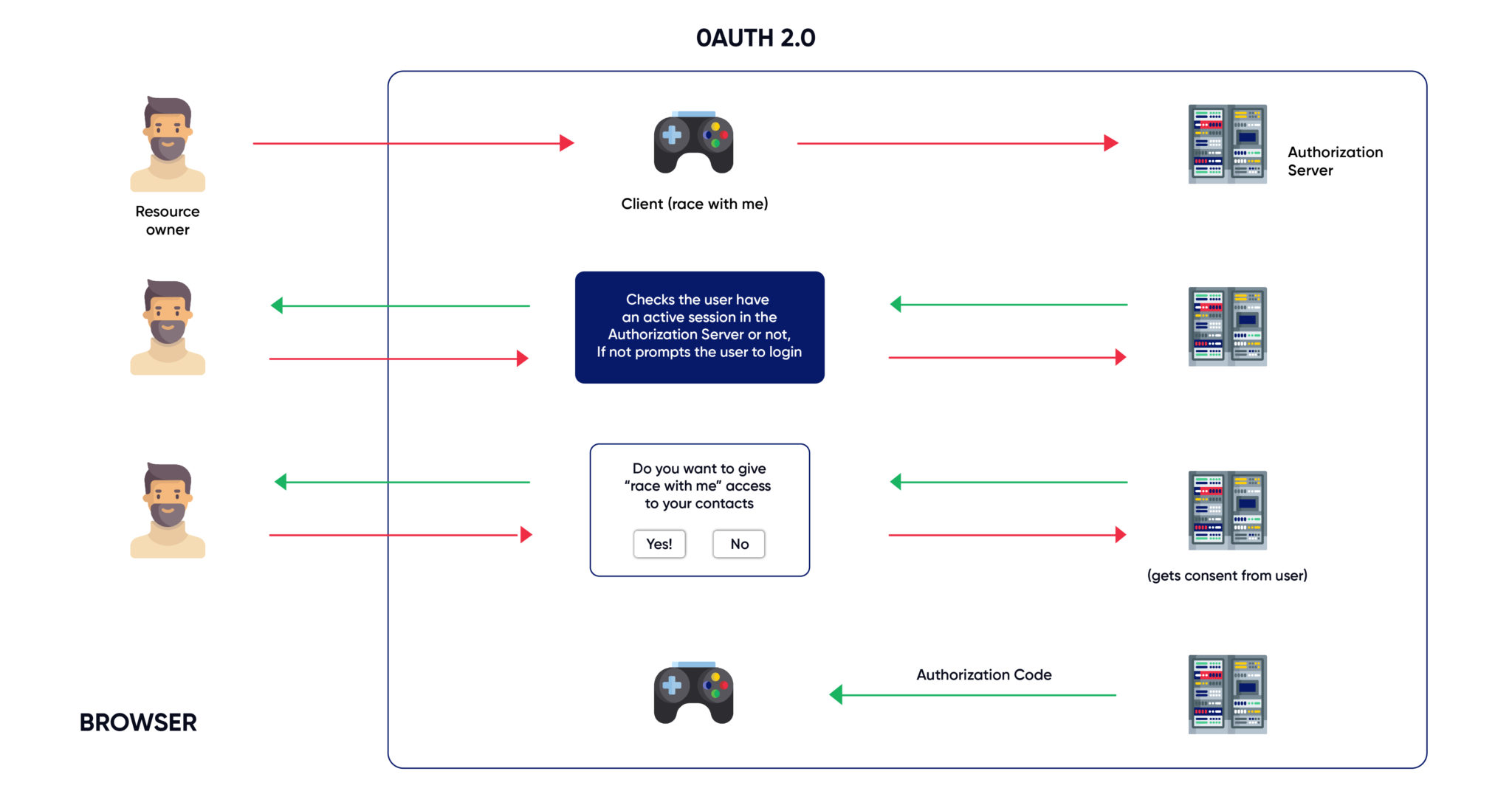
Oauth 2 0 Explained With Examples How Does It Work Oauth 2.0, which stands for “open authorization”, is a standard designed to allow a website or application to access resources hosted by other web apps on behalf of a user. it replaced oauth 1.0 in 2012 and is now the de facto industry standard for online authorization. Oauth 2.0 is like finding a secret door in the back of your favorite website, guarded by a bouncer. instead of just handing over your username and password like it's no big deal, oauth 2.0 insists on a exchanging tokens, redirect urls, and authorization codes. In this article, i’ll share a simple overview of oauth 2.0 🔐— what it is, why we need it, and how it’s different from the traditional authorization method. In this guide, we break down how oauth 2.0 works, core flows and grant types, security pitfalls to avoid, and how to implement oauth 2.0 using loginradius across web apps, spas, mobile apps, and machine to machine apis.
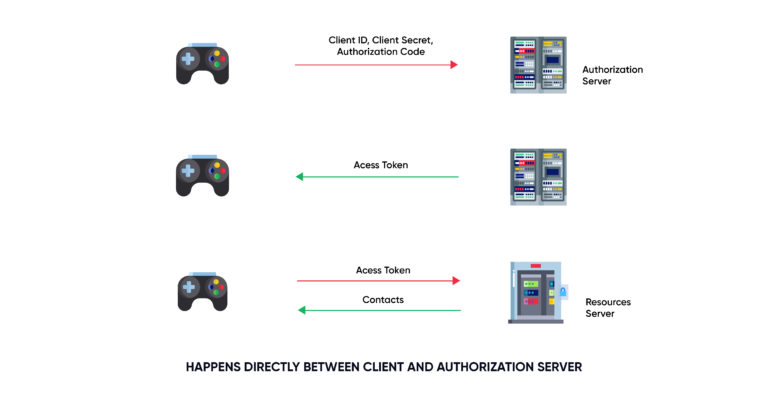
Oauth 2 0 Explained With Examples How Does It Work In this article, i’ll share a simple overview of oauth 2.0 🔐— what it is, why we need it, and how it’s different from the traditional authorization method. In this guide, we break down how oauth 2.0 works, core flows and grant types, security pitfalls to avoid, and how to implement oauth 2.0 using loginradius across web apps, spas, mobile apps, and machine to machine apis. When you use oauth, you get an oauth token that represents your identity and permissions. this token can do a few important things: single sign on (sso): with an oauth token, you can log into multiple services or apps using just one login, making life easier and safer. Oauth2.0 is an open industry standard authorization protocol that allows a third party to gain limited access to another http service, such as google, facebook, and github, on behalf of a user, once the user grants permission to access their credentials. This tutorial is designed for software programmers who would like to understand the concepts of oauth. this tutorial will give you enough understanding on oauth from where you can take yourself to higher levels of expertise. Basically, oauth 2.0 is a security standard where you give one application permission to access your data in another application. the steps to grant permission, or consent, are often referred to as authorization or even delegated authorization.
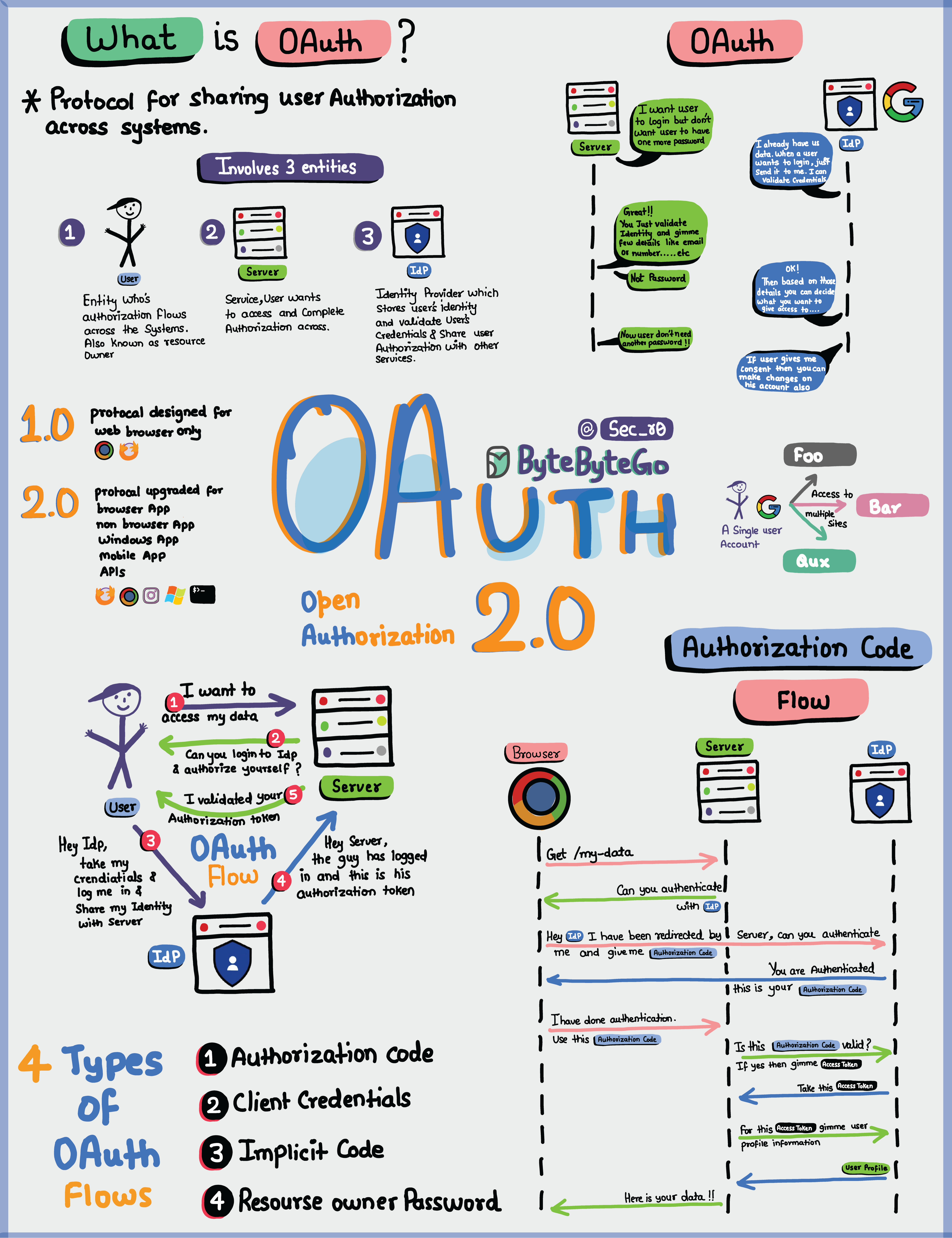
Bytebytego Oauth 2 0 Explained With Simple Terms When you use oauth, you get an oauth token that represents your identity and permissions. this token can do a few important things: single sign on (sso): with an oauth token, you can log into multiple services or apps using just one login, making life easier and safer. Oauth2.0 is an open industry standard authorization protocol that allows a third party to gain limited access to another http service, such as google, facebook, and github, on behalf of a user, once the user grants permission to access their credentials. This tutorial is designed for software programmers who would like to understand the concepts of oauth. this tutorial will give you enough understanding on oauth from where you can take yourself to higher levels of expertise. Basically, oauth 2.0 is a security standard where you give one application permission to access your data in another application. the steps to grant permission, or consent, are often referred to as authorization or even delegated authorization.

Ep72 Oauth 2 0 Explained With Simple Terms This tutorial is designed for software programmers who would like to understand the concepts of oauth. this tutorial will give you enough understanding on oauth from where you can take yourself to higher levels of expertise. Basically, oauth 2.0 is a security standard where you give one application permission to access your data in another application. the steps to grant permission, or consent, are often referred to as authorization or even delegated authorization.
Comments are closed.