Nmap Tutorial Ip Spoofing Youtube
Ip And Mac Spoofing Techniques Using Nmap For Stealth Scanning In this video i am explaining and demonstrating ip spoofing and ip decoying and showing you details through wireshark. Learn how to evade firewalls and ids with nmap! master nmap techniques like decoy scans, packet fragmentation, ip spoofing, and rate limiting for network security testing. improve your nmap skills today!.

Free Video Nmap Class Tcp Ip And Basics Of Nmap Part 1 From Youtube With a basic understanding of ip addresses and service ports, this tutorial will walk you through installing nmap, running your first scans, and understanding how nmap works at the packet level, why ports show as open, closed, or filtered, and how to interpret what you're seeing. A simple tutorial showing how to scan the network for live hosts, detecting their os and ip spoofing using nmap. In this video we will see, how can we spoof the ip address through nmapfor more info visit our website iethicalhacking xiarch. Our approach involves both online and classroom training, featuring hands on projects delivered practically by seasoned industry experts. with wscube tech, you'll gain hands on skills that make you.

Free Video Nmap Class Tcp Ip And Basics Of Nmap Part 2 From Youtube In this video we will see, how can we spoof the ip address through nmapfor more info visit our website iethicalhacking xiarch. Our approach involves both online and classroom training, featuring hands on projects delivered practically by seasoned industry experts. with wscube tech, you'll gain hands on skills that make you. How to spoof an ip address while scanning with nmap. d34dl0k1 part of a series of video tutorials about nmap and network hacking discovery. … more. About press copyright contact us creators advertise developers terms privacy policy & safety how works test new features nfl sunday ticket © 2024 google llc. I tried nmap s (
Ip Spoofing Pelo Nmap Security Master How to spoof an ip address while scanning with nmap. d34dl0k1 part of a series of video tutorials about nmap and network hacking discovery. … more. About press copyright contact us creators advertise developers terms privacy policy & safety how works test new features nfl sunday ticket © 2024 google llc. I tried nmap s (
Ip Spoofing Pelo Nmap Security Master I tried nmap s (
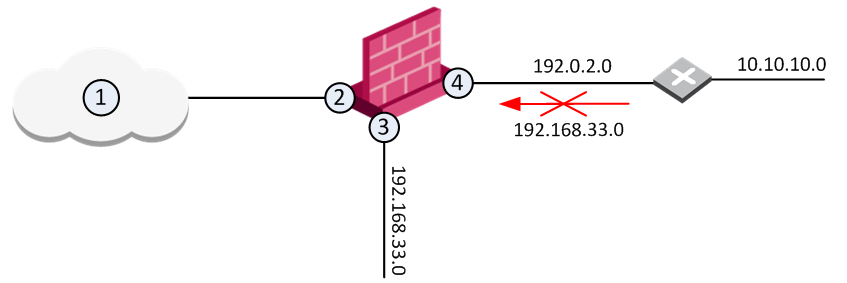
Preventing Ip Spoofing
Comments are closed.