Nmap Tutorial Ip Spoofing
Ip And Mac Spoofing Techniques Using Nmap For Stealth Scanning There is no magic bullet (or nmap option) for detecting and subverting firewalls and ids systems. it takes skill and experience. a tutorial is beyond the scope of this reference guide, which only lists the relevant options and describes what they do. In this video i am explaining and demonstrating ip spoofing and ip decoying and showing you details through wireshark.

What Is Ip Spoofing Anura Learn how to use the ` s` option with nmap to spoof the source address, a powerful tool for testing firewall rules and evading detection. Learn how to evade firewalls and ids with nmap! master nmap techniques like decoy scans, packet fragmentation, ip spoofing, and rate limiting for network security testing. improve your nmap skills today!. Learn how to perform ip and mac spoofing with nmap to mask scan origins, evade detection, and understand ethical considerations in network scanning. In this blog, we will cover noise generation and decoy attacks using syn port scans with spoofed source ip addresses. as penetration testers or red teamers, we are often tasked with operating from an unauthenticated perspective within internal networks, simulating assumed breach scenarios.
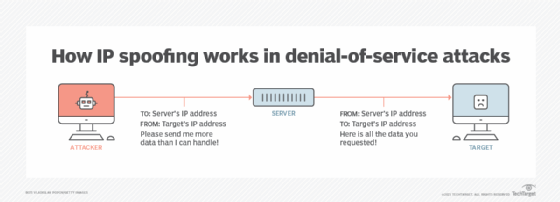
What Is Ip Spoofing How To Prevent It Learn how to perform ip and mac spoofing with nmap to mask scan origins, evade detection, and understand ethical considerations in network scanning. In this blog, we will cover noise generation and decoy attacks using syn port scans with spoofed source ip addresses. as penetration testers or red teamers, we are often tasked with operating from an unauthenticated perspective within internal networks, simulating assumed breach scenarios. Nmap lets you spoof your ip address using s ip address. spoofing the ip address is useful if your system is on the same subnetwork as the target host; otherwise, you won’t be able to read the replies sent back. I tried nmap s (
Ip Spoofing Pelo Nmap Security Master Nmap lets you spoof your ip address using s ip address. spoofing the ip address is useful if your system is on the same subnetwork as the target host; otherwise, you won’t be able to read the replies sent back. I tried nmap s (
Ip Spoofing Pelo Nmap Security Master In this blog i will be sharing the use of different switches which are used in nmap of bypassing firewall ids ips. with the use of this switches, data packets can be sent in the way that firewall ids ips does not detect the packet as different than normal packets. In this post, while most nmap tutorials stop at basic port scans and os detection, this post ventures into the shadows — where stealth, deception, and protocol manipulation redefine.
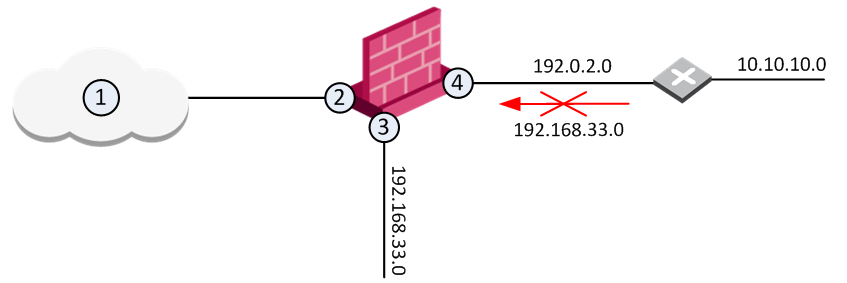
Preventing Ip Spoofing
Comments are closed.