Nist Protect
Frameworks Nist These mappings are intended to demonstrate the relationship between existing nist publications and the cybersecurity framework. The goal of the protect function is to develop and implement appropriate safeguards to ensure delivery of critical services. the protect function supports the ability to limit or contain the impact of a potential cybersecurity event.

Evaluating Encryption With The Nist Protect Framework Securitysenses The protect function under national institute of standards and technology cybersecurity framework (nist csf) helps you better understand and manage cybersecurity risks through safeguarding your data and systems against online attacks. Learn how to enhance your cybersecurity with the protect function in nist csf 2.0. explore access control, data security, and tools like encryption to safeguard assets effectively. The protect (pr) function at the highest level is defined as “safeguards to manage the organization’s cybersecurity risks”. safeguarding endpoints as a physical asset, however, cannot be protected by fences and video surveillance realistically as you would a data center physical asset. The nist cybersecurity framework (csf) is a set of guidelines developed by the u.s. national institute of standards and technology (nist) to help organizations manage and mitigate cybersecurity risks.

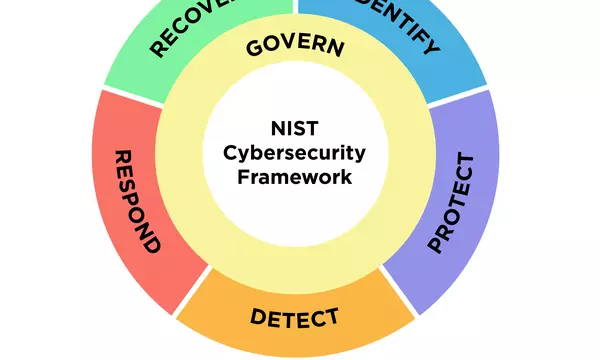
Nist Cybersecurity Framework Protect 11 11 Innovation Blog The protect (pr) function at the highest level is defined as “safeguards to manage the organization’s cybersecurity risks”. safeguarding endpoints as a physical asset, however, cannot be protected by fences and video surveillance realistically as you would a data center physical asset. The nist cybersecurity framework (csf) is a set of guidelines developed by the u.s. national institute of standards and technology (nist) to help organizations manage and mitigate cybersecurity risks. Protect (pr), information protection processes and procedures (pr.ip) protect (pr), maintenance (pr.ma) protect (pr), protective technology (pr.pt) copyright © 2017 2020 patrick marsceill. distributed by an mit license. The nist cybersecurity framework aims to improve cybersecurity through five core functions identify, protect, detect, respond, and recover. Dive into the nist csf's core function, protect, for robust cybersecurity. published in 2014, it's flexible, open ended, and renowned for its effectiveness. Six functions organize the csf 2.0 — govern, identify, protect, detect, respond, and recover. together, these functions provide a comprehensive view of managing cybersecurity risk.

30 Cyber Security Nist Images Stock Photos Vectors Shutterstock Protect (pr), information protection processes and procedures (pr.ip) protect (pr), maintenance (pr.ma) protect (pr), protective technology (pr.pt) copyright © 2017 2020 patrick marsceill. distributed by an mit license. The nist cybersecurity framework aims to improve cybersecurity through five core functions identify, protect, detect, respond, and recover. Dive into the nist csf's core function, protect, for robust cybersecurity. published in 2014, it's flexible, open ended, and renowned for its effectiveness. Six functions organize the csf 2.0 — govern, identify, protect, detect, respond, and recover. together, these functions provide a comprehensive view of managing cybersecurity risk.

Nist Cyber Security Framework Identify Protect Stock Vector Royalty Dive into the nist csf's core function, protect, for robust cybersecurity. published in 2014, it's flexible, open ended, and renowned for its effectiveness. Six functions organize the csf 2.0 — govern, identify, protect, detect, respond, and recover. together, these functions provide a comprehensive view of managing cybersecurity risk.
Comments are closed.