Nist Cybersecurity Framework Implementation Case Study Sepa

Nist Cybersecurity Framework Implementation Case Study Authored by utilities, this enhanced case study provides utility it experts with a view into one of many potential approaches that electric utilities can use to leverage the nist csf, as well as the doe cybersecurity capability maturity model (es c2m2), to implement cybersecurity programs. The objective of this case study was to design a secure, compliant it environment aligned with dod and federal cybersecurity requirements while balancing operational needs, risk tolerance, and regulatory constraints. the project emphasizes security architecture, governance, and control selection rather than tool specific implementation.
Nist Cybersecurity Framework Implementation Case Study Sepa The nist cybersecurity framework implementation case study gives detailed steps and real world examples for implementing the csf, enabling utilities to identify and prioritize top security risks and present that information to senior management for cost benefit analysis exercises and planning. Do we understand and have the right assets, including “traditional” and “non traditional” nist skillsets, needed to carry out the program? what level of impact is a successful outcome of the program expected to have? where are we today? interest in and use of the cybersecurity framework is strong and growing!. This paper uses the national institute of standards and technology (nist) cyber security framework (csf) to assess the cyber security posture of a local government organisation in. Table iii summarizes the primary objectives and research contributions of each study, including case applications, comparative analyses, and proposals for implementation models of the nist framework.
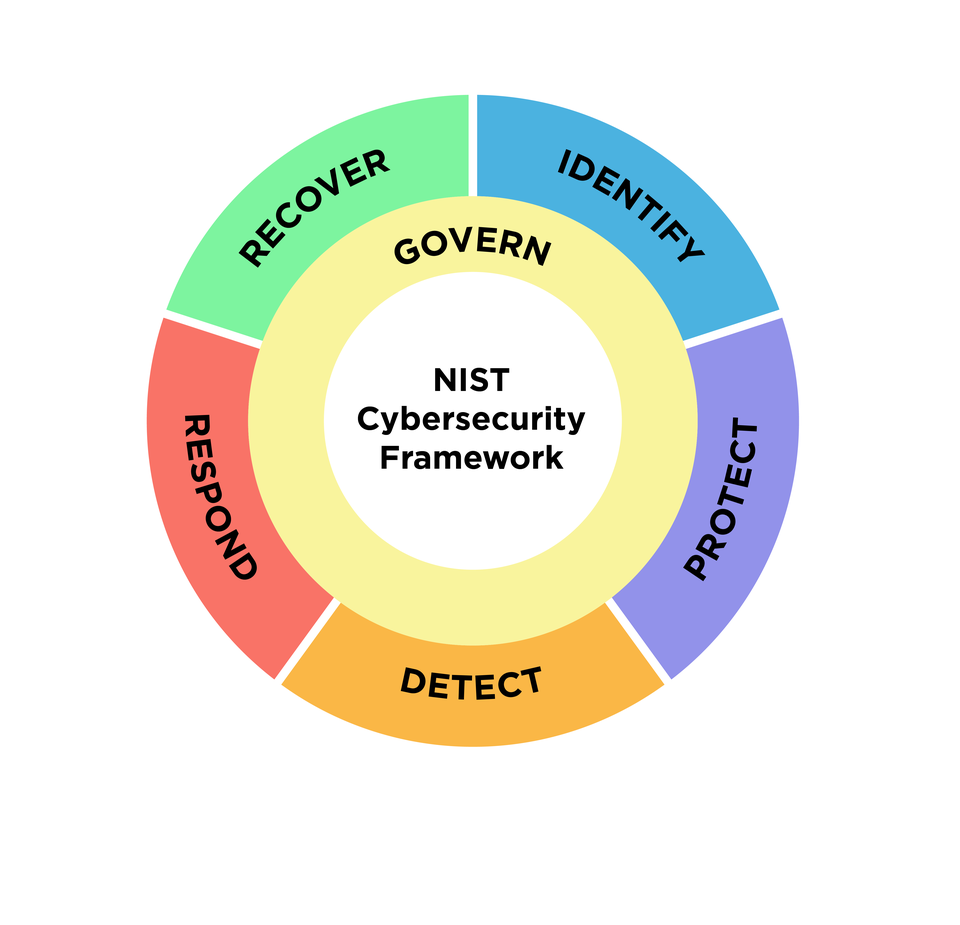
Nist Cybersecurity Framework 2 0 Draft This paper uses the national institute of standards and technology (nist) cyber security framework (csf) to assess the cyber security posture of a local government organisation in. Table iii summarizes the primary objectives and research contributions of each study, including case applications, comparative analyses, and proposals for implementation models of the nist framework. This paper reviews the nist based approach to implementing security for an ics ot, referencing the nist cybersecurity framework1 (csf), the five cybersecurity critical controls from the sans institute that are most relevant to icses, and fortinet security fabric2 technologies. Integrating risk management with business processes: ensuring cyber risks are part of enterprise risk management. case study and real world applications: reviewing a case study on implementing the nist csf in a real world organization. practical exercises: hands on activities to apply core functions and implementation tiers in simulated scenarios. Course overview this comprehensive course is designed to help organizations implement and comply with the nist cybersecurity framework. participants will gain a deep understanding of the framework's core components, implementation strategies, and best practices for managing and reducing cybersecurity risks. Nist csf 2.0 offers actionable implementation examples that help organizations align their cybersecurity risk management decisions with their mission, stakeholder expectations, and legal obligations.

Case Study Sepa Compliance Assurance Redcompass Labs This paper reviews the nist based approach to implementing security for an ics ot, referencing the nist cybersecurity framework1 (csf), the five cybersecurity critical controls from the sans institute that are most relevant to icses, and fortinet security fabric2 technologies. Integrating risk management with business processes: ensuring cyber risks are part of enterprise risk management. case study and real world applications: reviewing a case study on implementing the nist csf in a real world organization. practical exercises: hands on activities to apply core functions and implementation tiers in simulated scenarios. Course overview this comprehensive course is designed to help organizations implement and comply with the nist cybersecurity framework. participants will gain a deep understanding of the framework's core components, implementation strategies, and best practices for managing and reducing cybersecurity risks. Nist csf 2.0 offers actionable implementation examples that help organizations align their cybersecurity risk management decisions with their mission, stakeholder expectations, and legal obligations.
Comments are closed.