Networking Ssh Secure Shell
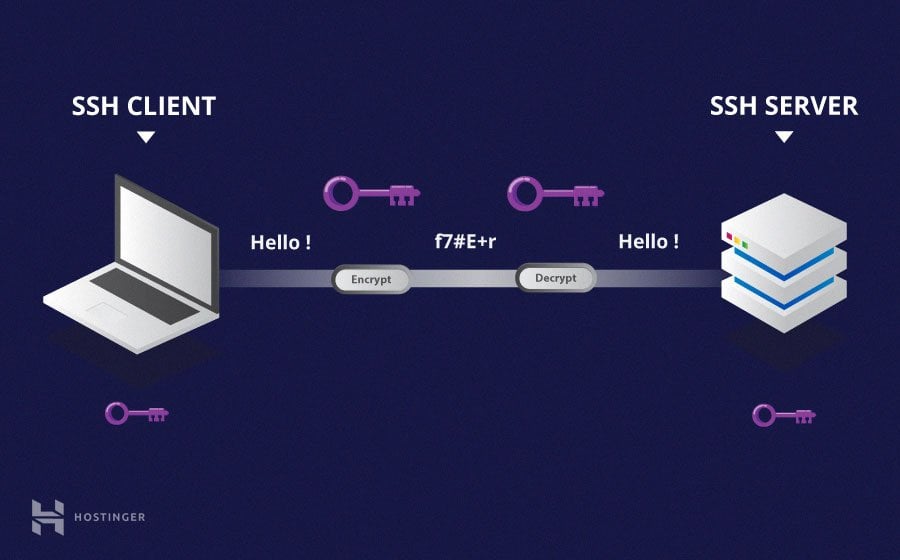
Secure Shell Protocol Ssh Msblab Ssh (secure shell) is a network protocol that establishes encrypted connections between computers for secure remote access. it operates on tcp port 22 and provides authentication, encryption, and integrity to protect data transmitted over unsecured networks. The ssh protocol uses encryption to secure the connection between a client and a server. all user authentication, commands, output, and file transfers are encrypted to protect against attacks in the network.

Secure Shell Ssh Protocol Encryption Over Insecure Networks The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. ssh also refers to the suite of utilities that implement the ssh protocol. Ssh (short for secure shell) is a network protocol that provides a secure way for two computers to connect remotely. ssh employs encryption to ensure that hackers cannot interpret the traffic between two connected devices.

Secure Shell Ssh Protocol Encryption Over Insecure Networks Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. ssh also refers to the suite of utilities that implement the ssh protocol. Ssh (short for secure shell) is a network protocol that provides a secure way for two computers to connect remotely. ssh employs encryption to ensure that hackers cannot interpret the traffic between two connected devices. Ssh is a secure protocol for encrypted communication, remote access, file transfers, and tunneling, offering robust authentication and data protection. secure shell (ssh) is a foundational tool for securely managing systems, transferring files, and tunneling connections. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric. Ssh specializes in remote shell access, secure file transfers, and creating secure tunnels for other network services. the ssh protocol provides session based encryption optimized for interactive command execution and bulk data transfers rather than request response web communications. Ssh (secure shell protocol) is an encrypted protocol for accessing and managing remote systems, such as a server, over the internet. it’s similar to other remote access tools like telnet, but provides a mechanism for authenticating hosts and data transfer.

299 Secure Shell Ssh Images Stock Photos Vectors Shutterstock Ssh is a secure protocol for encrypted communication, remote access, file transfers, and tunneling, offering robust authentication and data protection. secure shell (ssh) is a foundational tool for securely managing systems, transferring files, and tunneling connections. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric. Ssh specializes in remote shell access, secure file transfers, and creating secure tunnels for other network services. the ssh protocol provides session based encryption optimized for interactive command execution and bulk data transfers rather than request response web communications. Ssh (secure shell protocol) is an encrypted protocol for accessing and managing remote systems, such as a server, over the internet. it’s similar to other remote access tools like telnet, but provides a mechanism for authenticating hosts and data transfer.

Secure Shell Ssh Explained Encryption Ports Connecting Ssh specializes in remote shell access, secure file transfers, and creating secure tunnels for other network services. the ssh protocol provides session based encryption optimized for interactive command execution and bulk data transfers rather than request response web communications. Ssh (secure shell protocol) is an encrypted protocol for accessing and managing remote systems, such as a server, over the internet. it’s similar to other remote access tools like telnet, but provides a mechanism for authenticating hosts and data transfer.

Ssh Secure Shell Doodle Icon Design Illustration Networking Symbol On
Comments are closed.