Networking Operating Systems Security
Github Dyeoell Computer Network Operating Systems Security It is software that checks a network or system for malicious activities or policy violations. each illegal activity or violation is often recorded either centrally using a siem system or notified to an administration. This article explores the role of networking and operating systems in cybersecurity, highlighting their functions, vulnerabilities, and best practices for enhanced security.

Network Security Overview Types Tools Technologies And This research contributes to advancing knowledge in os security and informs the development of effective strategies to safeguard computer systems against evolving threats and vulnerabilities. It is essential for cyber security professionals to have a solid understanding of how computers communicate. there is much more happening behind the scenes of computer networks than what can be observed when using applications. By employing authentication, access controls, and encryption techniques, os security aims to mitigate various threats such as malware, network intrusions, and buffer overflow attacks, thereby safeguarding the overall functionality and security of the operating system. Network security combines policies and technologies to protect systems and digital assets from unauthorized access, misuse, and disruption. by using layered defenses rather than a single control, it ensures data integrity and reliable performance across increasingly complex, distributed networks.
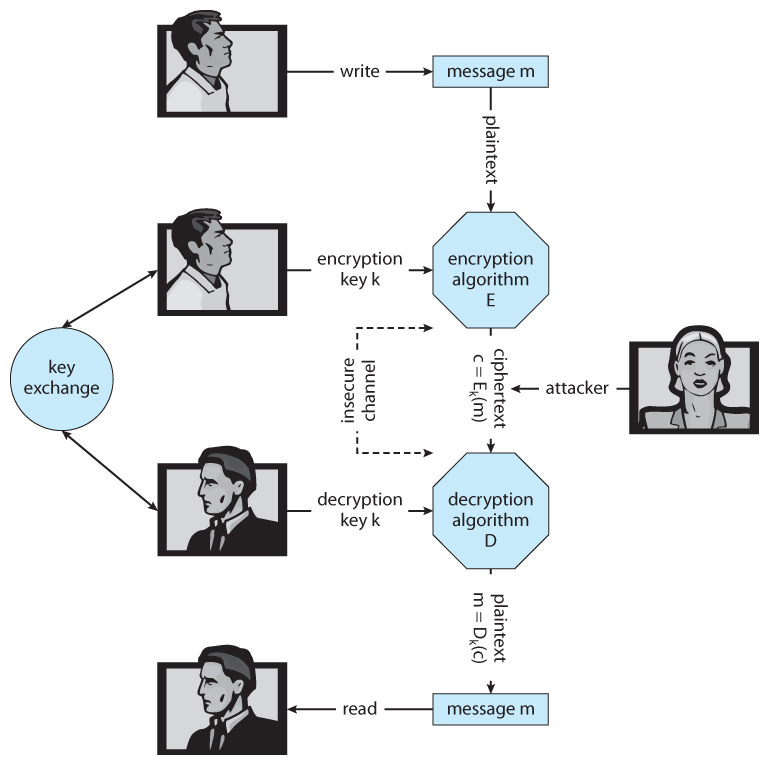
Operating Systems Protection By employing authentication, access controls, and encryption techniques, os security aims to mitigate various threats such as malware, network intrusions, and buffer overflow attacks, thereby safeguarding the overall functionality and security of the operating system. Network security combines policies and technologies to protect systems and digital assets from unauthorized access, misuse, and disruption. by using layered defenses rather than a single control, it ensures data integrity and reliable performance across increasingly complex, distributed networks. This article explores how operating system s manage network security, detailing the mechanisms they employ to safeguard systems against unauthorized access, data breaches, and cyberattacks. Lectures cover threat models, attacks that compromise security, and techniques for achieving security, based on recent research papers. topics include operating system (os) security, capabilities, information flow control, language security, network protocols, hardware security, and security in web applications. Learn about the crucial role of operating systems in computer networking and how they handle tasks like data transmission, network security, and resource management. The use of weak passwords compromises the security of the operating system, making it susceptible to attacks that can result in data breaches, loss of sensitive information, and a broader security compromise within the network.

What Is A Network Operating System Definition From Techtarget This article explores how operating system s manage network security, detailing the mechanisms they employ to safeguard systems against unauthorized access, data breaches, and cyberattacks. Lectures cover threat models, attacks that compromise security, and techniques for achieving security, based on recent research papers. topics include operating system (os) security, capabilities, information flow control, language security, network protocols, hardware security, and security in web applications. Learn about the crucial role of operating systems in computer networking and how they handle tasks like data transmission, network security, and resource management. The use of weak passwords compromises the security of the operating system, making it susceptible to attacks that can result in data breaches, loss of sensitive information, and a broader security compromise within the network.
Comments are closed.