Network Segmentation Future Ready Network Architecture Narrowin

Nokia Deploys Future Ready Network Architecture To Enhance Zayo S Our segmentation concepts comply with leading security standards such as iec 62443, nist cybersecurity framework, iso 27001 and industry specific requirements for energy, healthcare and critical infrastructure. automatic mapping and visualization of your network topology. Free vlan planning tool for network segmentation. start from scratch or use templates like purdue model for ot it networks. export your vlan plan as csv.

Network Architecture With Micro Segmentation Download Scientific Diagram "the consistent segmentation and centralized management make the network secure and manageable. thanks to zero touch provisioning and template based architecture, it scales with the expansion of the heating networks." managing director, zweckverband breitbandversorgung landkreis lörrach. Explore narrowin's projects and customer case studies in networking and security. university partnerships, industrial cybersecurity research and real world implementations. Learn how network segmentation contains breaches and stops lateral movement. explore segmentation types, zero trust architecture, and implementation strategy. Network segmentation divides a computer network into smaller, isolated segments to control and restrict communication. it enhances security by limiting unauthorized access and containing potential threats within defined boundaries.
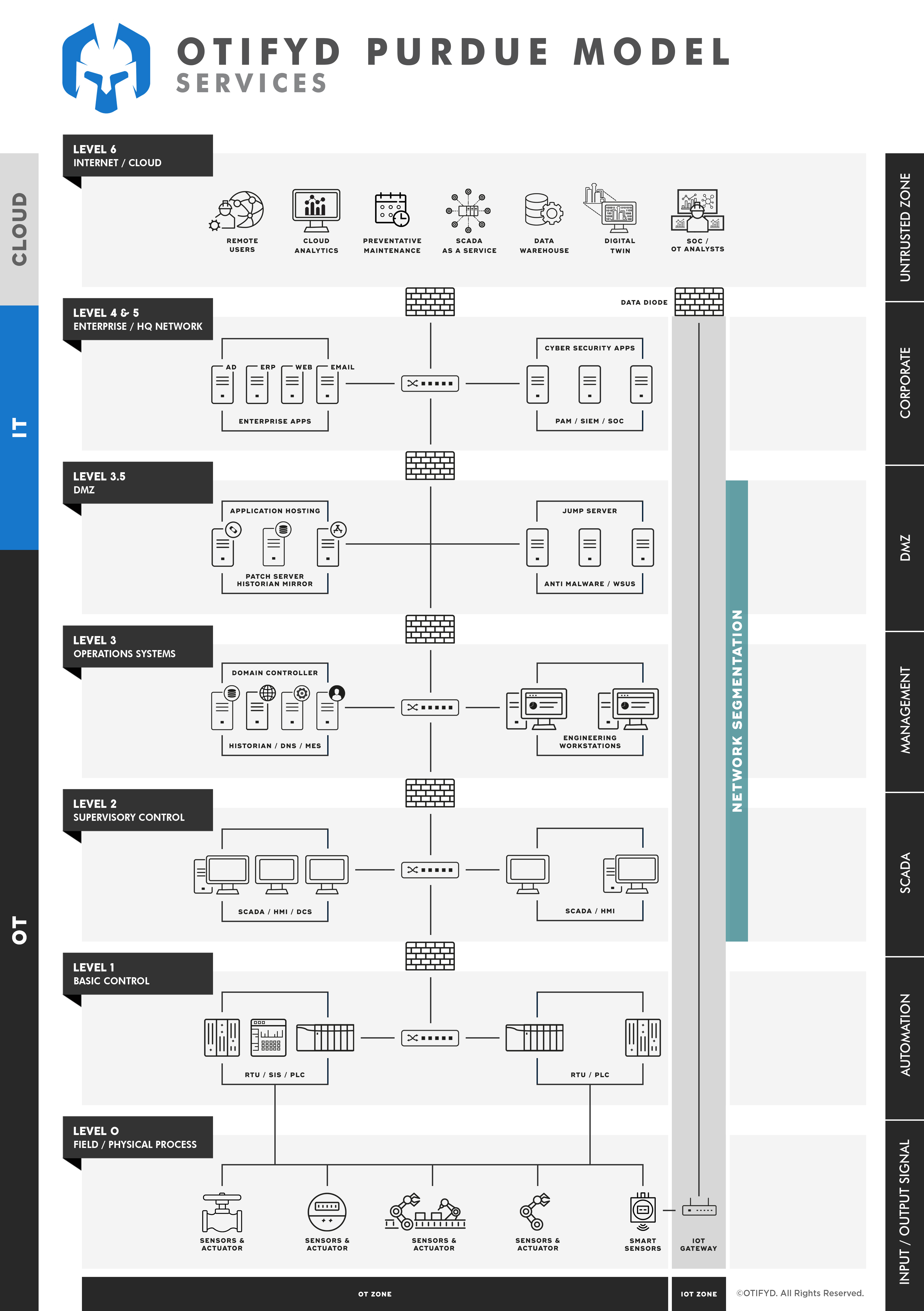
Network Segmentation Otifyd Safeguarding Ot Networks Learn how network segmentation contains breaches and stops lateral movement. explore segmentation types, zero trust architecture, and implementation strategy. Network segmentation divides a computer network into smaller, isolated segments to control and restrict communication. it enhances security by limiting unauthorized access and containing potential threats within defined boundaries. Learn about the recommendations for building a unified segmentation strategy using perimeters and isolation boundaries. With network segmentation, it can be very challenging to support legacy applications that rely on outdated protocols; you may have to create less restrictive segments. In this blog post, we review the basics of network segmentation and describe how organizations should implement it as an ongoing process. Learn how to use network segmentation best practices to effectively isolate network segments, minimize cyber threats, and maintain a robust security posture.

Network Architecture Of Segmentation Module Download Scientific Diagram Learn about the recommendations for building a unified segmentation strategy using perimeters and isolation boundaries. With network segmentation, it can be very challenging to support legacy applications that rely on outdated protocols; you may have to create less restrictive segments. In this blog post, we review the basics of network segmentation and describe how organizations should implement it as an ongoing process. Learn how to use network segmentation best practices to effectively isolate network segments, minimize cyber threats, and maintain a robust security posture.
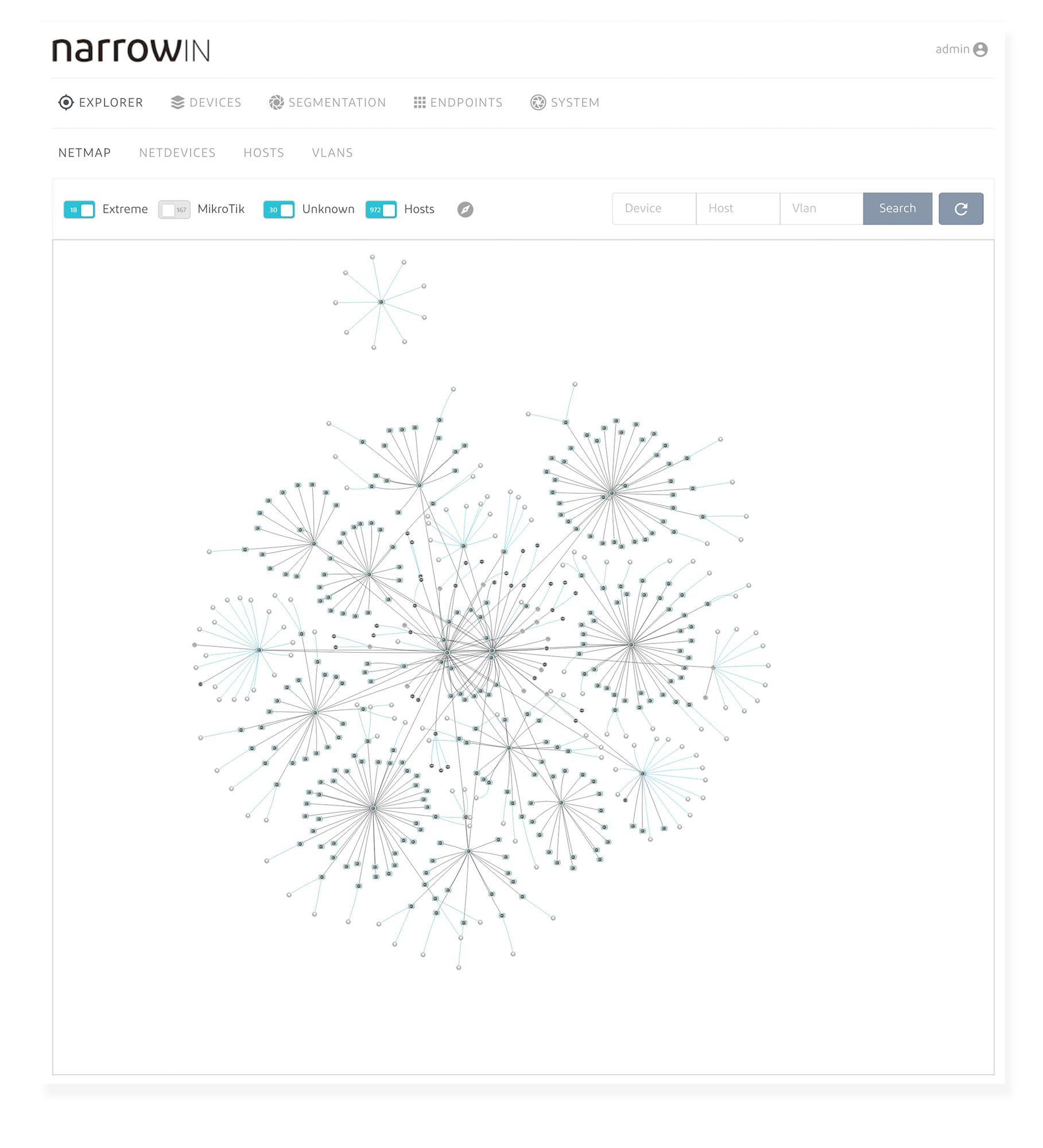
Network Segmentation Future Ready Network Architecture Narrowin In this blog post, we review the basics of network segmentation and describe how organizations should implement it as an ongoing process. Learn how to use network segmentation best practices to effectively isolate network segments, minimize cyber threats, and maintain a robust security posture.

Network Segmentation Future Ready Network Architecture Narrowin
Comments are closed.