Network Security Protocols Letsdefend 11 Comments

Tryhackme Walkthrough Network Security Protocols Secure network ports using port security and disable unnecessary protocols like cdp. leverage features like 802.1x authentication, bpdu guard, and dhcp snooping for enhanced network. During this course section, we'll explore the intricacies of network security, focusing on practical security strategies and techniques to enhance your ability to protect digital systems effectively.
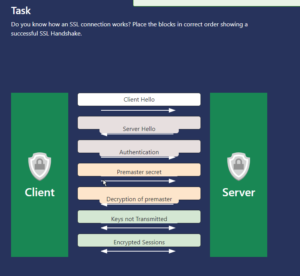
Tryhackme Walkthrough Network Security Protocols While creating tcp ip computer networks, a logical address (ip address) must first be assigned to each device in the network. these assignment processes are called "ip addressing mechanism". If you want to investigate suspicious network activities, you need to know how network protocols work and what evidence you can extract. learn how it works and how you can use it as an analyst. With its advanced threat detection capabilities, let’s defend empowers organizations to safeguard their digital assets from a wide range of security threats, including malware, ransomware,. The document introduces 'network fundamentals ii', a continuation of a network training series aimed at soc analysts, covering essential networking topics from a security perspective.
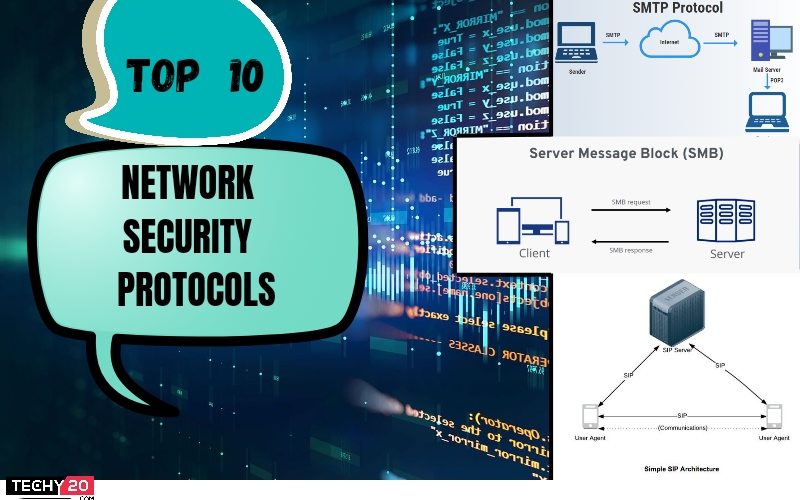
Top 10 Network Security Protocols Techy20 With its advanced threat detection capabilities, let’s defend empowers organizations to safeguard their digital assets from a wide range of security threats, including malware, ransomware,. The document introduces 'network fundamentals ii', a continuation of a network training series aimed at soc analysts, covering essential networking topics from a security perspective. As we can see there are 25,262 packets so let’s filter the streams to tcp protocols and check if there is anything suspicious. okay got 7780 stream so let’s check the whole stream and find something interesting. Network protocols http status codes for log analysis nov 18, 2025 · 195 views. With that said, i am researching letsdefend, security blueteam, and cyberdefenders to curate a more practical learning path to actually obtain the skills required to do the job i am aiming for which would be entry level cyber. This course will teach you how application level protocols work and how you can use it as soc analyst or incident responder. as an investigator, you need to know the basics of these protocols to use it as evidence.
Understanding Network Security Protocols As we can see there are 25,262 packets so let’s filter the streams to tcp protocols and check if there is anything suspicious. okay got 7780 stream so let’s check the whole stream and find something interesting. Network protocols http status codes for log analysis nov 18, 2025 · 195 views. With that said, i am researching letsdefend, security blueteam, and cyberdefenders to curate a more practical learning path to actually obtain the skills required to do the job i am aiming for which would be entry level cyber. This course will teach you how application level protocols work and how you can use it as soc analyst or incident responder. as an investigator, you need to know the basics of these protocols to use it as evidence.

Letsdefend Top Network Protocols For Cybersecurity Teams Facebook With that said, i am researching letsdefend, security blueteam, and cyberdefenders to curate a more practical learning path to actually obtain the skills required to do the job i am aiming for which would be entry level cyber. This course will teach you how application level protocols work and how you can use it as soc analyst or incident responder. as an investigator, you need to know the basics of these protocols to use it as evidence.
Network Security Protocols Pptx
Comments are closed.