Network Security Pdf Virtual Private Network Backup

Virtual Private Network Pdf Virtual Private Network Computer Network A virtual private network (vpn) i s a secure communication technology that enables users to send and receive data across public or shared networks as if their devices were. Network security is challenging as new threats emerge regularly. this document discusses elements used to secure networks, including virtual private networks (vpns) and protocols like pptp and l2tp. vpns extend local area networks over public networks through encrypted connections between computers. while vpns reduce costs and simplify adding remote clients, they also raise security and.

Network Security Pdf Virtual Private Network Backup Overview of virtual private networks (vpns) for secure remote access virtual private networks (vpns) are a foundational technology for enabling secure remote access to corporate networks, especially as remote and hybrid work become standard business practices. they provide encrypted connections, ensuring data confidentiality and integrity even over insecure public networks. Introduction to vpn virtual private network (vpn) is a secure communication technology that enables users to send and receive data across public or shared networks as if their devices were directly connected to a private network. vpns ensure privacy, security, and anonymity, making them essential for personal, corporate, and governmental use. Abstract— virtual private networks (vpns) have become a communication medium for accessing information, data exchange and flow of information. many organizations require intranet or vpn, for data access, access to servers from computers and sharing different types of data among their offices and users. a secure vpn environment is essential to the organizations to protect the information and. These systems use encryption and other security mechanisms to ensure that only authorized users can access the network and that the data cannot be intercepted the act of configuring and creating a virtual private network is known as virtual private networking. a well designed vpn can greatly benefit a company. for example, it can:.

09 Network Security Pdf Virtual Private Network Computer Network Abstract— virtual private networks (vpns) have become a communication medium for accessing information, data exchange and flow of information. many organizations require intranet or vpn, for data access, access to servers from computers and sharing different types of data among their offices and users. a secure vpn environment is essential to the organizations to protect the information and. These systems use encryption and other security mechanisms to ensure that only authorized users can access the network and that the data cannot be intercepted the act of configuring and creating a virtual private network is known as virtual private networking. a well designed vpn can greatly benefit a company. for example, it can:. Abstract: virtual private network (vpn) is a network technology that has been widely used in internet communications. this paper conducts an in depth study of the definition of vpn, the importance of internet communication, and its practice in application fields such as privacy protection, remote office, geographical location restrictions, and public wi fi security. we also provide an in depth. Materials and synopsis of the course certified network security specialist (cnss) provided by the international cybersecurity institute (icsi) icsi certified network security specialist cnss 06. The purpose of this policy is to provide guidelines for remote access virtual private network (vpn) connections to the city of providence network. this policy ensures the confidentiality, integrity, and availability of the city's data and it infrastructure, minimizing the risk of unauthorized access, data breaches, and other security threats. This creates a virtual network connection between the two points. however, this connection only provides a virtual network, and then the data is also encrypted, thus making that virtual network private. the question becomes this: how does one implement the authentication and encryption required to create a vpn?.
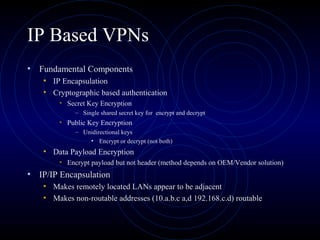
Virtual Private Network Ppt Computer Networking Computing Abstract: virtual private network (vpn) is a network technology that has been widely used in internet communications. this paper conducts an in depth study of the definition of vpn, the importance of internet communication, and its practice in application fields such as privacy protection, remote office, geographical location restrictions, and public wi fi security. we also provide an in depth. Materials and synopsis of the course certified network security specialist (cnss) provided by the international cybersecurity institute (icsi) icsi certified network security specialist cnss 06. The purpose of this policy is to provide guidelines for remote access virtual private network (vpn) connections to the city of providence network. this policy ensures the confidentiality, integrity, and availability of the city's data and it infrastructure, minimizing the risk of unauthorized access, data breaches, and other security threats. This creates a virtual network connection between the two points. however, this connection only provides a virtual network, and then the data is also encrypted, thus making that virtual network private. the question becomes this: how does one implement the authentication and encryption required to create a vpn?.

Virtual Private Network Doc The purpose of this policy is to provide guidelines for remote access virtual private network (vpn) connections to the city of providence network. this policy ensures the confidentiality, integrity, and availability of the city's data and it infrastructure, minimizing the risk of unauthorized access, data breaches, and other security threats. This creates a virtual network connection between the two points. however, this connection only provides a virtual network, and then the data is also encrypted, thus making that virtual network private. the question becomes this: how does one implement the authentication and encryption required to create a vpn?.

Virtual Private Network Pdf Virtual Private Network Computer Network
Comments are closed.