Network Security Module 1 Pdf

Module 4 Network Security Pdf Security Computer Security Network security professionals must use secure devices on the edge of the network. in the figure, the main site is protected by an adaptive security appliance (asa), which provides stateful firewall features and establishes secure virtual private network (vpn) tunnels to various destinations. This document outlines the course details for the network security course taught by dr. shivashankar. the course aims to help students understand network security concepts like services, mechanisms, transport layer security, ip security, intrusion detection, firewalls and malicious software.

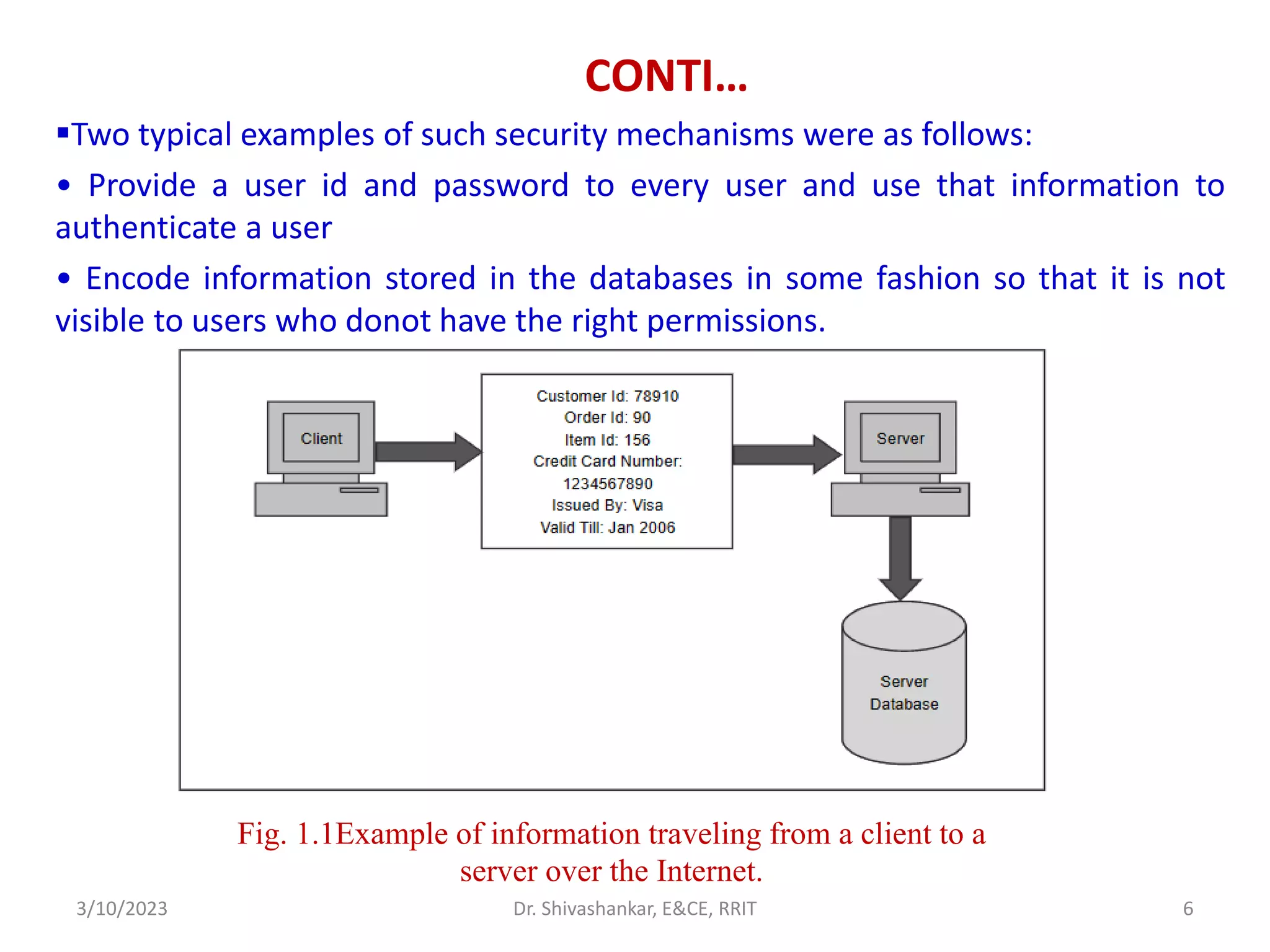
Module 01 Security Overview Pdf Network security v1.0 module 1 free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. Processes on two different end systems communicate with each other by exchanging messages across the computer network. a sending process creates and sends messages into the network; a receiving process receives these messages and possibly responds by sending messages back. • network security professionals must use secure devices on the edge of the network. • data center physical security is divided into two areas: outside perimeter security and inside perimeter security. Data center physical security can be divided into two areas: • outside perimeter security this can include on premise security officers, fences, gates, continuous video surveillance, and security breach alarms.

Network Security Module 1 Pdf Nse 1 network security technology foundation module 1: data center security module 2: next generation firewall (ngfw) module 3: unified threat management (utm) module 4: application security. This course is based to a significant extend on slides provided by prof. günter schäfer, author of the book "netzsicherheit algorithmische grundlagen und protokolle", available in german from dpunkt verlag. In the field of network security, the objective is to ensure the confidentiality, integrity, and authenticity of information being communicated over a potentially insecure network. Each module is comprised of topics. modules emphasize critical thinking, problem solving, collaboration, and the practical application of skills. many modules contain some way to practice and assess understanding, such as a lab or a packet tracer activity.
Network Security Module 1 Pdf In the field of network security, the objective is to ensure the confidentiality, integrity, and authenticity of information being communicated over a potentially insecure network. Each module is comprised of topics. modules emphasize critical thinking, problem solving, collaboration, and the practical application of skills. many modules contain some way to practice and assess understanding, such as a lab or a packet tracer activity.

Module 1 Network Security Introduction Pdf Vulnerability Computing
Comments are closed.