Network Security Latest 2 Data Communication Ppt Pptx
Network Security Latest 2 Data Communication Ppt Pptx The document outlines the importance of network security and the various types associated with it, as well as authentication and network attack methods. This network security course provides a comprehensive overview of both theory and practice, covering topics such as cryptography, key exchange, email security, web security, hacking, and anti hacker techniques. the course also explores recent developments in the field.
Network Security Latest 2 Data Communication Ppt Pptx Computing The document recommends using strong, unique passwords for each account and biometric authentication to help protect data from hacking. strong passwords include mixed cases, numbers, and frequent changing. additional security measures can include security questions and personal images. Network security protects electronic devices such as computers, servers, mobile gadgets, data, electronic systems, and networks from network attacks. this powerpoint presentation illustrates important details about network security. It discusses the importance of secure communication channels, the prevention of network attacks, and the encapsulation de encapsulation process across different network layers. additionally, it highlights the interaction of network hardware and security measures such as vpns and port access controls. download as a pptx, pdf or view online for. This document provides an overview of network security principles including cryptography, authentication, message integrity, and key distribution.
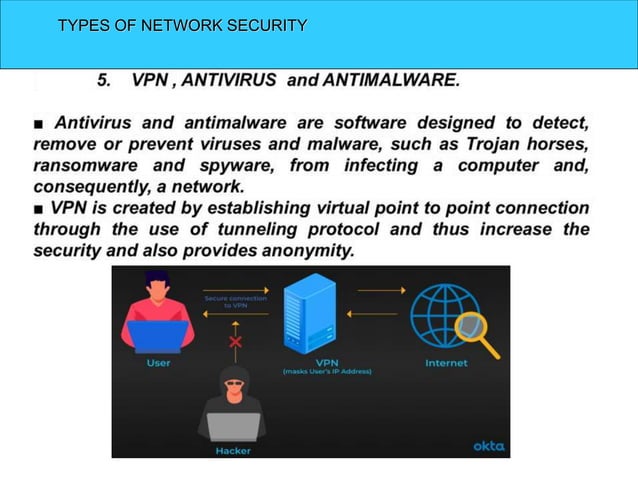
Network Security Latest 2 Data Communication Ppt Pptx Computing It discusses the importance of secure communication channels, the prevention of network attacks, and the encapsulation de encapsulation process across different network layers. additionally, it highlights the interaction of network hardware and security measures such as vpns and port access controls. download as a pptx, pdf or view online for. This document provides an overview of network security principles including cryptography, authentication, message integrity, and key distribution. The document discusses the critical need for network security in today's interconnected world, highlighting its history, types, and the evolution of security methods. It also discusses protocols for security at the network layer (ipsec), transport layer (ssl tls), and application layer (pgp), as well as the use of firewalls to filter network traffic. download as a pptx, pdf or view online for free. Network security protocols play a vital role in securing digital communication and establishing trust online. they provide encryption, authentication, access controls and other functions to protect data confidentiality, integrity and availability. It covers fundamental concepts, types of network security methods, authentication processes, and common network attacks, along with the advantages and challenges of implementing security measures.
Network Security Latest 2 Data Communication Ppt Pptx Computing The document discusses the critical need for network security in today's interconnected world, highlighting its history, types, and the evolution of security methods. It also discusses protocols for security at the network layer (ipsec), transport layer (ssl tls), and application layer (pgp), as well as the use of firewalls to filter network traffic. download as a pptx, pdf or view online for free. Network security protocols play a vital role in securing digital communication and establishing trust online. they provide encryption, authentication, access controls and other functions to protect data confidentiality, integrity and availability. It covers fundamental concepts, types of network security methods, authentication processes, and common network attacks, along with the advantages and challenges of implementing security measures.
Network Security Latest 2 Data Communication Ppt Pptx Computing Network security protocols play a vital role in securing digital communication and establishing trust online. they provide encryption, authentication, access controls and other functions to protect data confidentiality, integrity and availability. It covers fundamental concepts, types of network security methods, authentication processes, and common network attacks, along with the advantages and challenges of implementing security measures.
Comments are closed.