Network Access Control Renaissance

Network Access Control Renaissance The number of endpoints on it networks is expanding at an ever increasing rate. user devices have moved beyond the traditional desktop and laptop to include smartphones, tablets, and wearable devices with network connectivity, such as the apple watch. Students who are using computers that aren't in your list of school network ip addresses can't use the products that are checked. notice that checked boxes are marked "restricted," while those that are not checked are marked "unrestricted.".

Guardians Of The Network The Evolution Of Access Control Technology Renaissance has been a valued and trusted partner of sierra wireless for several years. the team is easy to work with and accessible, while driving continuous improvement. Fortunately, network access control platforms have seen a renaissance in the past few years and have evolved substantially. Learn what network access control (nac) is, how it works with 802.1x and radius, and how modern nac enforces identity based, policy driven network security. Network access control (nac), also known as network admission control, is the process of restricting unauthorized users and devices from gaining access to a corporate or private network.
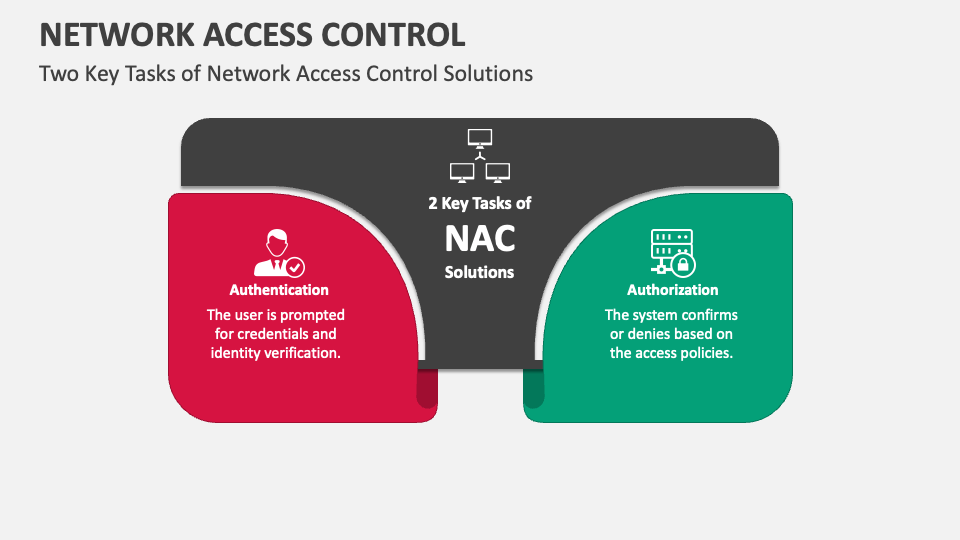
Network Access Control Powerpoint And Google Slides Template Ppt Slides Learn what network access control (nac) is, how it works with 802.1x and radius, and how modern nac enforces identity based, policy driven network security. Network access control (nac), also known as network admission control, is the process of restricting unauthorized users and devices from gaining access to a corporate or private network. Employees often bring their own devices (byod)? learn how network access control (nac) is the key to protecting your business network from cyber threat. Gaining access to a network should be more than forcing user and device authentication via credentials like user ids, passwords, biometrics, and certificates. network access control (nac) extends access management to processes designed to assess the state of devices attempting access to a network. Combined, these capabilities bolster the effectiveness of nac solutions in safeguarding networks from advanced threats. as organizations increasingly embrace zero trust security approaches and grapple with the complexities of distributed networks, the importance of nac solutions continues to grow. Network access control is no longer just about letting the right people in — it’s about keeping threats out and containing breaches. with zero trust network access (ztna) becoming the gold standard, organizations need modern nac solutions that provide visibility, segmentation, and adaptive security.
Comments are closed.