Network Access Control Introduction

Cezen Tech Network Access Control Network access control (nac) secures a network by ensuring only authenticated, compliant users and devices can connect. it strengthens protection by enforcing security policies, controlling device access, and preventing unauthorized or unsafe systems from entering the network. Network access control (nac) is a security solution that enforces policy on devices that access networks to increase network visibility and reduce risk.
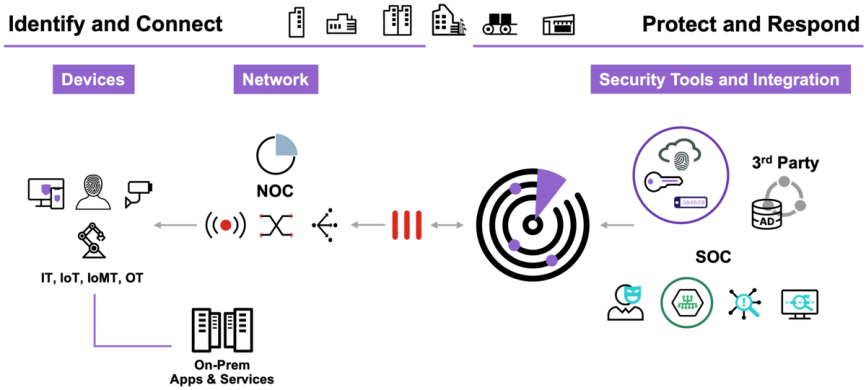
Network Access Control Provide Secure Access To Your Ict Network Network access control (nac) is an advanced security solution that helps control access to networks by enforcing policies that determine which users & devices are allowed to connect and what level of access they are granted. Learn how network access control works, its core components, and how to implement it for stronger network security. Discover how network access control (nac) enhances cybersecurity by controlling device access. learn its core functions, policies, and business benefits. Network access control (nac) is a security protocol that restricts unauthorized users and devices from gaining access to corporate or private networks.
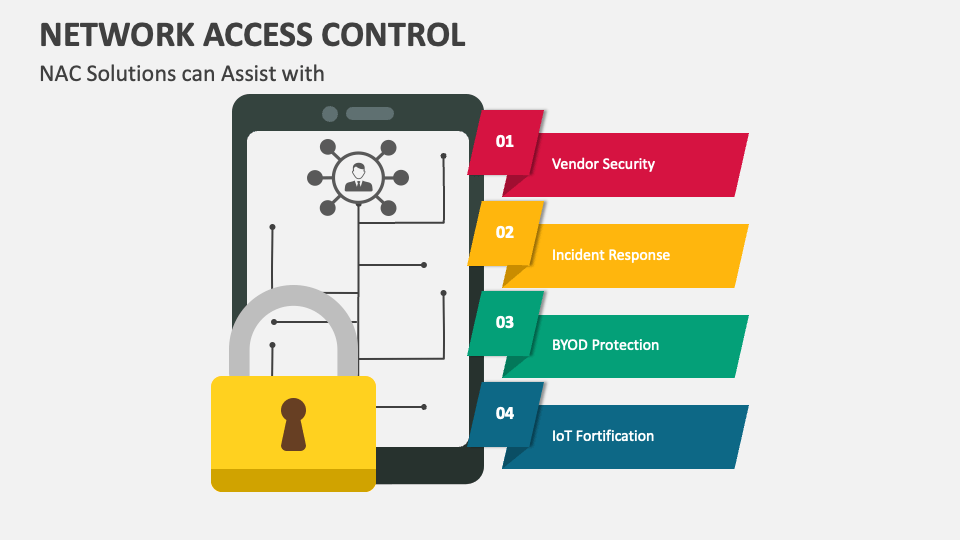
Network Access Control Complete Guide To Network Access Control Discover how network access control (nac) enhances cybersecurity by controlling device access. learn its core functions, policies, and business benefits. Network access control (nac) is a security protocol that restricts unauthorized users and devices from gaining access to corporate or private networks. Network access control (nac) regulates users’ and devices’ access to network resources, which is crucial in maintaining cybersecurity. understanding nac’s features and applications helps organizations protect sensitive data and optimize their it infrastructure. Network access control (nac) refers to a system that enforces security policies on devices trying to access the network. it ensures that only authorized, secure, and compliant devices can connect to your internal infrastructure. At its core, nac is a security solution that regulates and manages access to a network based on predetermined policies and compliance requirements. it encompasses both hardware and software technologies designed to authenticate and authorize devices and users before granting access to the network. Network access control (nac) is the process of leveraging security protocols such as endpoint monitoring and identity and access management (iam) to maximize control over who or what can access a proprietary network.

Guardians Of The Network The Evolution Of Access Control Technology Network access control (nac) regulates users’ and devices’ access to network resources, which is crucial in maintaining cybersecurity. understanding nac’s features and applications helps organizations protect sensitive data and optimize their it infrastructure. Network access control (nac) refers to a system that enforces security policies on devices trying to access the network. it ensures that only authorized, secure, and compliant devices can connect to your internal infrastructure. At its core, nac is a security solution that regulates and manages access to a network based on predetermined policies and compliance requirements. it encompasses both hardware and software technologies designed to authenticate and authorize devices and users before granting access to the network. Network access control (nac) is the process of leveraging security protocols such as endpoint monitoring and identity and access management (iam) to maximize control over who or what can access a proprietary network.
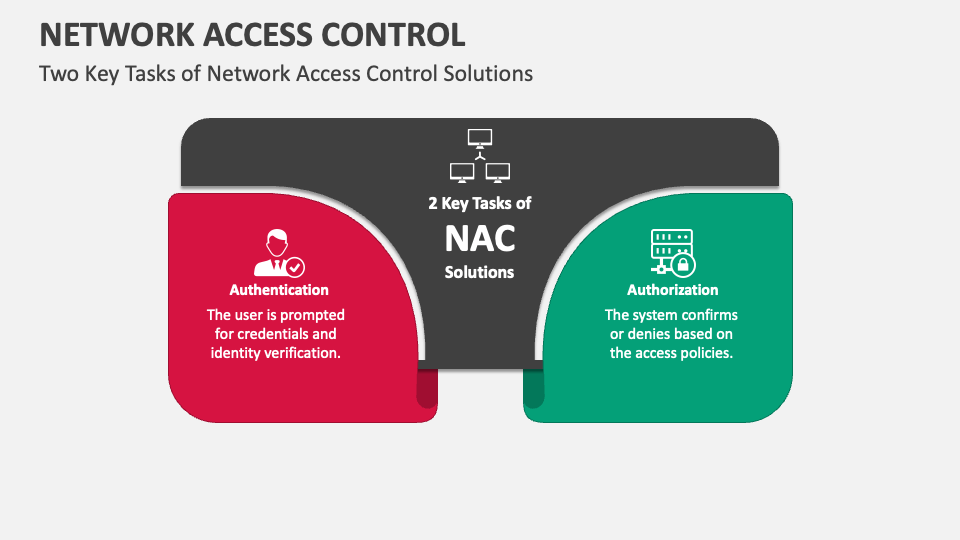
Network Access Control Powerpoint And Google Slides Template Ppt Slides At its core, nac is a security solution that regulates and manages access to a network based on predetermined policies and compliance requirements. it encompasses both hardware and software technologies designed to authenticate and authorize devices and users before granting access to the network. Network access control (nac) is the process of leveraging security protocols such as endpoint monitoring and identity and access management (iam) to maximize control over who or what can access a proprietary network.
Network Access Control Powerpoint And Google Slides Template Ppt Slides
Comments are closed.