Network Access And Context Aware Settings Amplified It
Network Access And Context Aware Settings Amplified It The configuration for context aware access is located under security > context aware access, which gives access to the three key components for setting up and using context aware access. build out your access levels – what condition (s) are we looking to meet or not meet for a rule to be applied. Discover how modern iam platforms leverage context—like location, device, time, and risk signals—to power adaptive, risk based access. explore the benefits, implementation strategies, and common pitfalls of context aware access controls for smarter security.
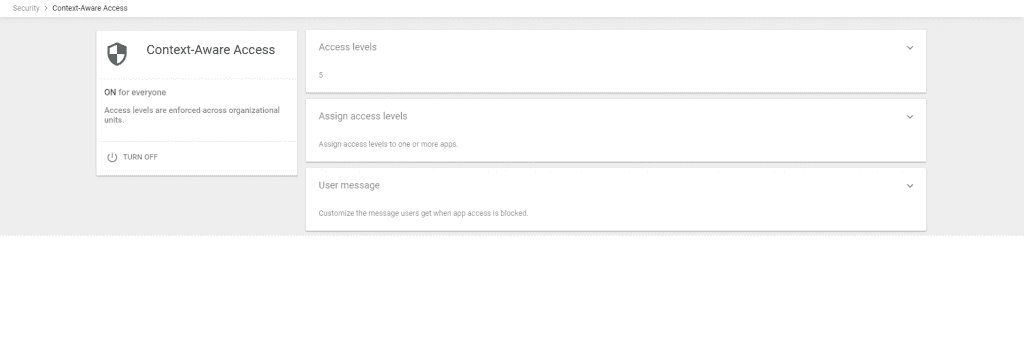
Network Access And Context Aware Settings Amplified It Using context aware access, you can create granular access control policies for apps that access workspace data based on attributes, such as user identity, location, device security status,. We’re making it easier to apply context aware access (caa) policies with new insights and recommendations. we’ll proactively surface potential security gaps and suggest pre built caa levels which admins can deploy to remediate the security gaps. Conditional access is at the heart of the new identity driven control plane. google's context aware access gives you control over which apps a user can access based on their context, such as whether their device complies with your it policy. Learn how to deploy context aware access in google workspace to enhance security by enforcing adaptive policies based on user identity, location, and more.

Network Access And Context Aware Settings Amplified It Conditional access is at the heart of the new identity driven control plane. google's context aware access gives you control over which apps a user can access based on their context, such as whether their device complies with your it policy. Learn how to deploy context aware access in google workspace to enhance security by enforcing adaptive policies based on user identity, location, and more. Its principles are simple: network based trust is obsolete, and access must always be determined by contextual signals tied to the user and device. beyondcorp enterprise (bce) extends this model to the browser, adding advanced threat and data protection directly into chrome. In this paper, we propose a fog based adaptive context aware access control (fb acaac) framework for iot devices, dynamically adjusting access policies based on contextual information to prevent unauthorised resource access. Google introduced new features in late october to enhance its context aware access (caa) policies, with the goal of improving cybersecurity with minimal manual effort. In this blog post, we will delve into how it administrators and security professionals can take full advantage of the enhanced context aware access rules to protect sensitive corporate data and ensure compliant collaboration within enterprise environments.
Comments are closed.