Ndpi Encrypted Traffic Analysis
Ndpi Traffic Classification Linuxbabe Dpi (deep packet inspection) however is not enough for complete visibility, and thus we have started to add classification techniques and algorithm to ndpi to merge visibility and behavioural analysis. You can use ndpi to selectively block selected internet traffic by embedding it onto an application (remember that ndpi is just a library). both ntopng and nprobe cento can do this.
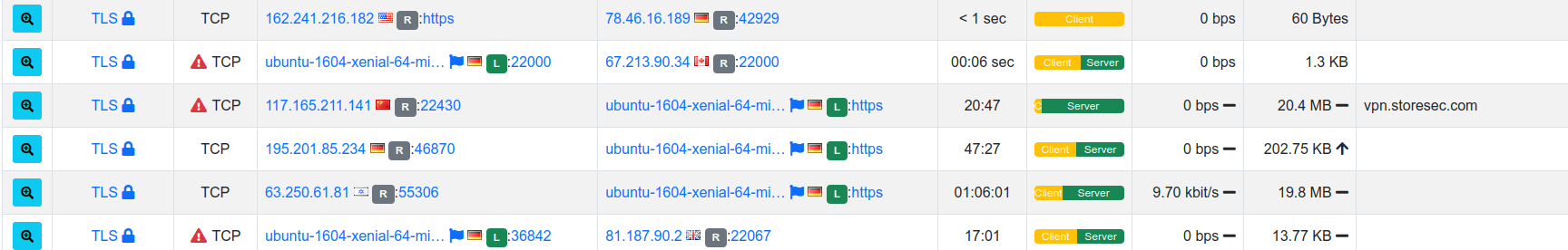
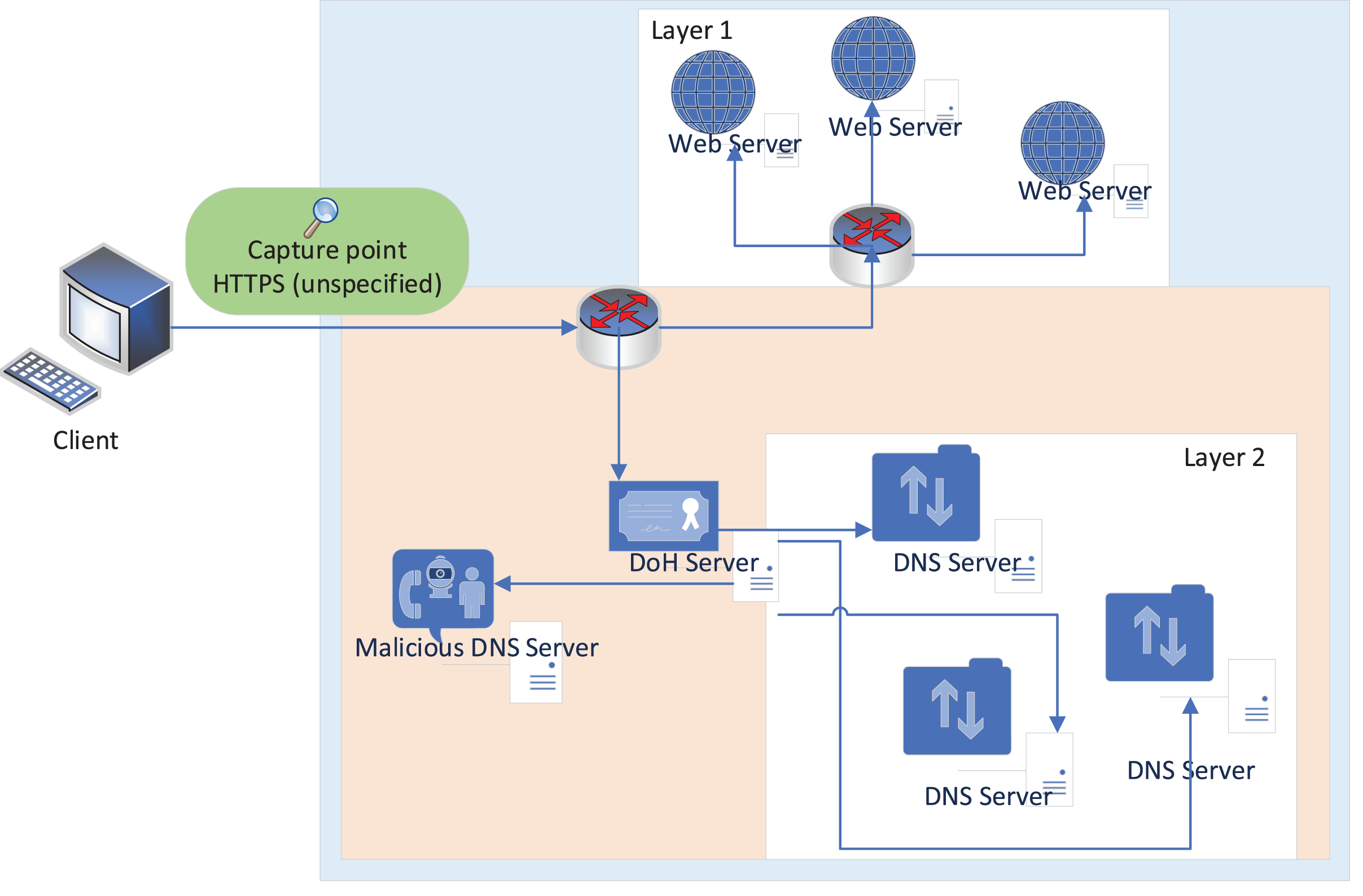
Github Lymeiseu Encrypted Network Traffic Analysis Encrypted Network Prevent specific traffic flows (e.g. unsafe tls communications) to happen on our network. provide metrics for measuring the nature of specific communications (e.g. https) while not being able to inspect the content. identify malware in network communications. Using tools like ndpi, tcpdump, suricata, and tshark enables comprehensive visibility into both encrypted and unencrypted network traffic. ndpi offers protocol classification at the. I installed ndpi and ntopng on an ubuntu machine and analyzed a real malware sample using a .pcap file from malware traffic analysis . Define methods for classifying (unknown) encrypted traffic similar to what ndpi does with doh that by means of binning techniques it can reliably detect this type of traffic.

Encrypted Traffic Analysis Inside Traffic I installed ndpi and ntopng on an ubuntu machine and analyzed a real malware sample using a .pcap file from malware traffic analysis . Define methods for classifying (unknown) encrypted traffic similar to what ndpi does with doh that by means of binning techniques it can reliably detect this type of traffic. Furthermore, since the trend of internet traffic is going towards encrypted content often using tls quic, ndpi allows you to extract metadata from encrypted communications and also classify encrypted traffic, implementing the so called eta (encrypted traffic analysis). The ndpi library supports both real time packet processing and offline pcap analysis, making it suitable for network monitoring applications, traffic analysis tools, and security products that require accurate protocol identification and traffic classification. This extensive study encapsulates the evolution of encrypted traffic analysis from traditional methodologies, which struggle with the advent of encryption, to modern ml techniques that proficiently unravel encrypted data’s complexities. Ndpi development lifecycle is typically 6 to 9 months. the history of changes and features implemented by every release, is available on its changelog. ndpi is open source and available on github. in addition, pre compiled, binary ndpi packages are available both for linux and other platforms.

Encrypted Traffic Analysis Heynen Furthermore, since the trend of internet traffic is going towards encrypted content often using tls quic, ndpi allows you to extract metadata from encrypted communications and also classify encrypted traffic, implementing the so called eta (encrypted traffic analysis). The ndpi library supports both real time packet processing and offline pcap analysis, making it suitable for network monitoring applications, traffic analysis tools, and security products that require accurate protocol identification and traffic classification. This extensive study encapsulates the evolution of encrypted traffic analysis from traditional methodologies, which struggle with the advent of encryption, to modern ml techniques that proficiently unravel encrypted data’s complexities. Ndpi development lifecycle is typically 6 to 9 months. the history of changes and features implemented by every release, is available on its changelog. ndpi is open source and available on github. in addition, pre compiled, binary ndpi packages are available both for linux and other platforms.
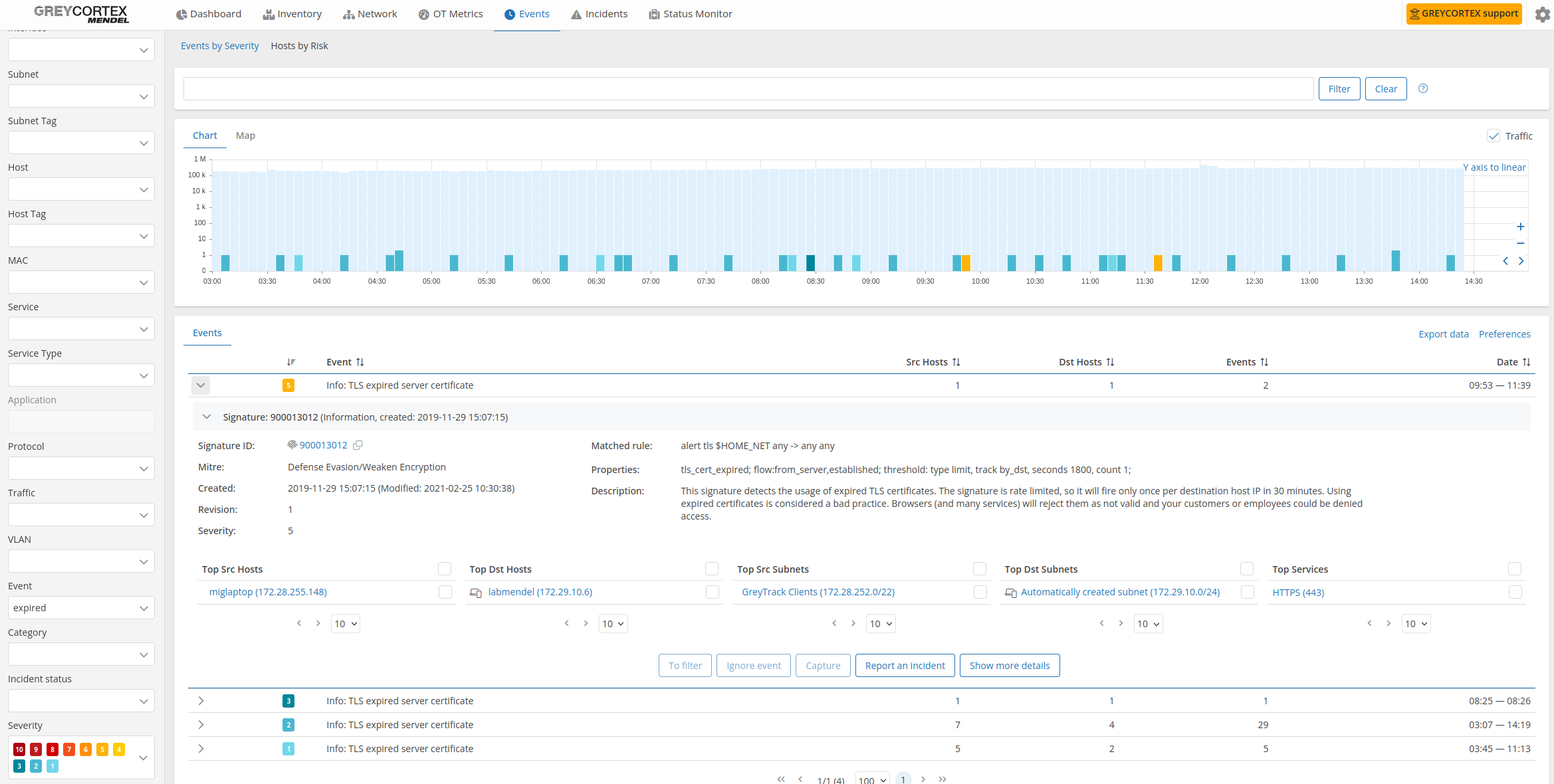
Encrypted Traffic Analysis Greycortex Solutions This extensive study encapsulates the evolution of encrypted traffic analysis from traditional methodologies, which struggle with the advent of encryption, to modern ml techniques that proficiently unravel encrypted data’s complexities. Ndpi development lifecycle is typically 6 to 9 months. the history of changes and features implemented by every release, is available on its changelog. ndpi is open source and available on github. in addition, pre compiled, binary ndpi packages are available both for linux and other platforms.
Encrypted Network Traffic Encrypted Network Traffic Analysis Fpyk
Comments are closed.