Navigating Vulnerability Mapping
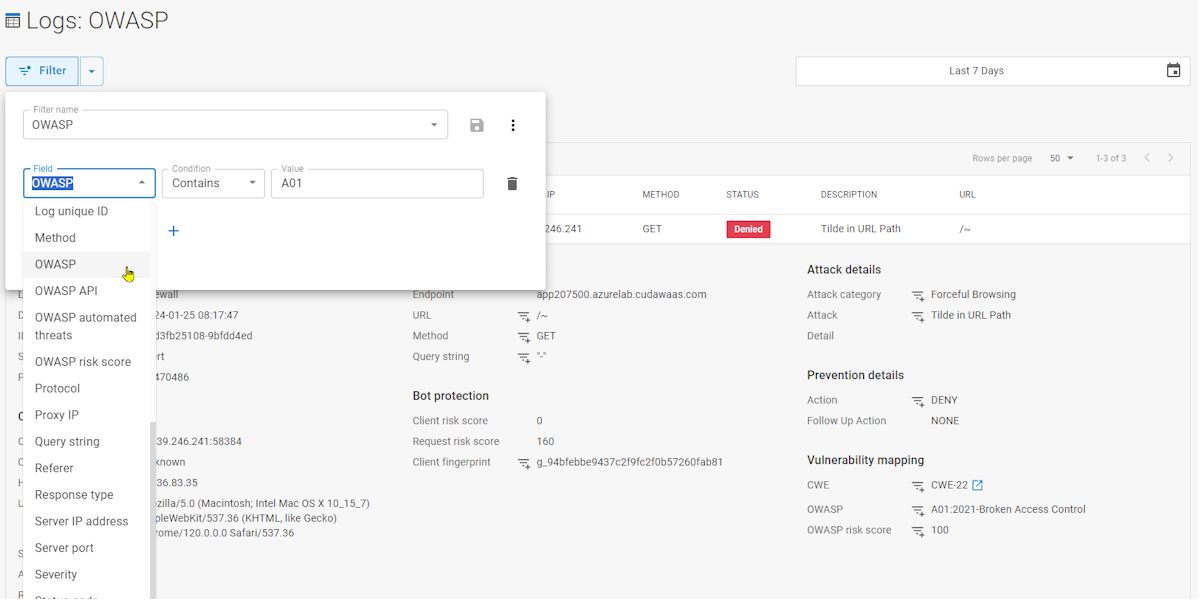
Barracuda Waf As A Service Updates Learn practical attack path mapping for effective threat modeling. transform theoretical security concepts into actionable steps for identifying and protecting critical assets. Attack paths in microsoft security exposure management help you to proactively identify and visualize potential routes that attackers can exploit using vulnerabilities, gaps, and misconfigurations across endpoints, cloud environments, and hybrid infrastructures.

Vulnerability Mapping Remediation Automate It By implementing a strategic vulnerability mapping process that leverages asm and vi, organizations can gain a comprehensive understanding of their attack surface, proactively identify and prioritize vulnerabilities, and make informed decisions to enhance their overall security posture. A complete guide to attack surface mapping—gain full visibility into external assets, exposures, and security risks. Mapping attack paths shows how attackers use vulnerabilities to break into systems. by simulating these steps, organizations can see potential weaknesses and prioritize their defenses better. Apm (attack path mapping) is a critical component of a modern security strategy. by moving beyond the limitations of cves and focusing on the potential attack paths, you can proactively address exposures and reduce your organization’s risk.
Github Abdiast Database Vulnerability Mapping Mapping attack paths shows how attackers use vulnerabilities to break into systems. by simulating these steps, organizations can see potential weaknesses and prioritize their defenses better. Apm (attack path mapping) is a critical component of a modern security strategy. by moving beyond the limitations of cves and focusing on the potential attack paths, you can proactively address exposures and reduce your organization’s risk. Mapping an organization’s attack surface involves understanding the vulnerabilities present in each of its it systems. the first step in accomplishing this is identifying all of the systems that the company owns. In this article, we will explore the concept of vulnerability mapping in depth, shedding light on its importance and how you can utilize attack surface management (asm) and vulnerability intelligence of socradar xti for vulnerability mapping. Using the vulnerability map you can see which of your workloads are highly vulnerable to attacks and can reduce the vulnerability score to make those workloads more secure. Learn how to use the attack surface map in microsoft security exposure management.

Vulnerability Mapping Vulnerability Assessment Pptx Mapping an organization’s attack surface involves understanding the vulnerabilities present in each of its it systems. the first step in accomplishing this is identifying all of the systems that the company owns. In this article, we will explore the concept of vulnerability mapping in depth, shedding light on its importance and how you can utilize attack surface management (asm) and vulnerability intelligence of socradar xti for vulnerability mapping. Using the vulnerability map you can see which of your workloads are highly vulnerable to attacks and can reduce the vulnerability score to make those workloads more secure. Learn how to use the attack surface map in microsoft security exposure management.

Vulnerability Risk Assessment Strategies Whitepaper Using the vulnerability map you can see which of your workloads are highly vulnerable to attacks and can reduce the vulnerability score to make those workloads more secure. Learn how to use the attack surface map in microsoft security exposure management.

Mapping Vulnerability Over Time Tabulae Spatial Services
Comments are closed.