Multiple Access Techniquescdmatdmafdmaofdm

An Overview Of Multiple Access Techniques For Wireless Communication This chapter contains sections titled: frequency division multiple access (fdma) time division multiple access (tdma) code division multiple access (cdma). Cdma is much recommended for voice and data communications. while multiple codes occupy the same channel in cdma, the users having same code can communicate with each other. cdma offers more air space capacity than tdma. the hands off between base stations is very well handled by cdma.

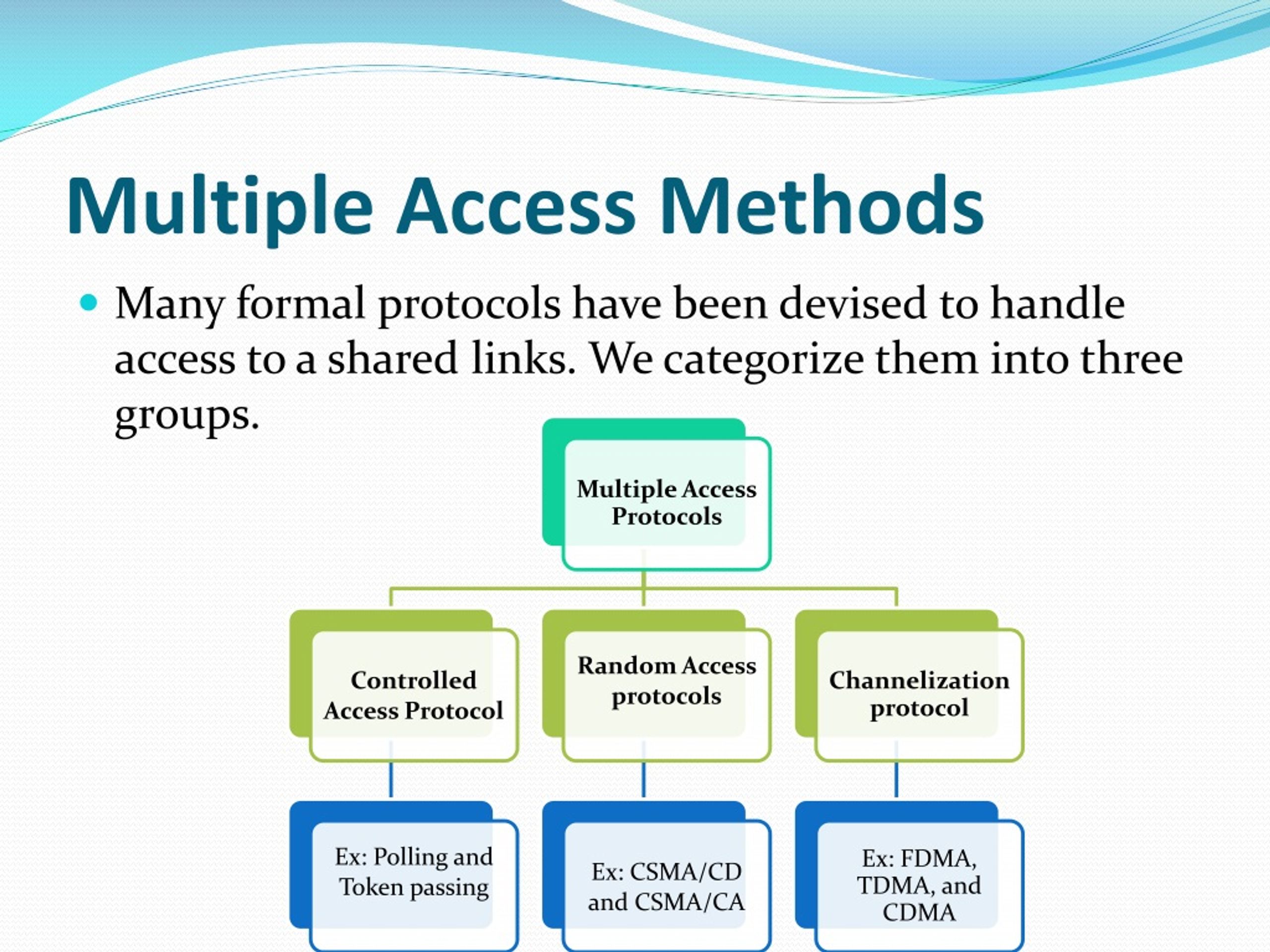
Unit Iv Multiple Access Techniques Pdf Channel Access Method Cdma becomes the dominant multiple access technique in the third generation (3g) wireless communication systems, with the prevailing worldwide standards known as cdma2000, wcdma (wideband cdma), and td scdma (time division – synchronous cdma). This can be achieved through various methods such as frequency division multiple access (fdma), time division multiple access (tdma), code division multiple access (cdma), or random access. In principle, there are three basic ways to have many channels within an allocated bandwidth: frequency division multiple access (fdma) time division multiple access (tdma) code division multiple access (cdma). This document discusses multiple access techniques for wireless communications. it introduces frequency division multiple access (fdma), time division multiple access (tdma), and code division multiple access (cdma) as the three major techniques used.

Pdf Elektro Undip Ac Idelektro Undip Ac Id Sukiswo Download Tts 04 In principle, there are three basic ways to have many channels within an allocated bandwidth: frequency division multiple access (fdma) time division multiple access (tdma) code division multiple access (cdma). This document discusses multiple access techniques for wireless communications. it introduces frequency division multiple access (fdma), time division multiple access (tdma), and code division multiple access (cdma) as the three major techniques used. Fdma stands for frequency division multiple access. tdma stands for time division multiple access. cdma stands for code division multiple access. in this, sharing of bandwidth among different stations takes place. Various methods exist to enable access to the channel, such as multiplexing. the main multiple access techniques used in wireless communications under multiplexing include fdma, tdma,. When many mobile users share the same channel, the strongest received mobile signal will capture the demodulator at a base station. thus a nearby subscriber could overpower the base station receiver by drowning out the signals of far away subscribers. Here, we focus on specific protocols or methods guiding access to the medium used for transmission and retransmission of packets (messages) to and from the satellites.
Ppt Multiple Access Techniques Powerpoint Presentation Free Download Fdma stands for frequency division multiple access. tdma stands for time division multiple access. cdma stands for code division multiple access. in this, sharing of bandwidth among different stations takes place. Various methods exist to enable access to the channel, such as multiplexing. the main multiple access techniques used in wireless communications under multiplexing include fdma, tdma,. When many mobile users share the same channel, the strongest received mobile signal will capture the demodulator at a base station. thus a nearby subscriber could overpower the base station receiver by drowning out the signals of far away subscribers. Here, we focus on specific protocols or methods guiding access to the medium used for transmission and retransmission of packets (messages) to and from the satellites.
Ppt Lec 5 Part 2 Powerpoint Presentation Free Download Id 609463 When many mobile users share the same channel, the strongest received mobile signal will capture the demodulator at a base station. thus a nearby subscriber could overpower the base station receiver by drowning out the signals of far away subscribers. Here, we focus on specific protocols or methods guiding access to the medium used for transmission and retransmission of packets (messages) to and from the satellites.

Multiple Access Techniques Pdf Channel Access Method Duplex
Comments are closed.