Multi Input Attribute Based Encryption And Predicate Encryption

Multi Authentication Attribute Based Encryption Download Scientific Motivated by several new and natural applications, we initiate the study of multi input predicate encryption (mipe) and further develop multi input attribute based encryption (miabe). Motivated by several new and natural applications, we initiate the study of multi input predicate encryption (\ (\textsf {mipe}\)) and further develop multi input attribute based encryption (\ (\textsf {miabe}\)).
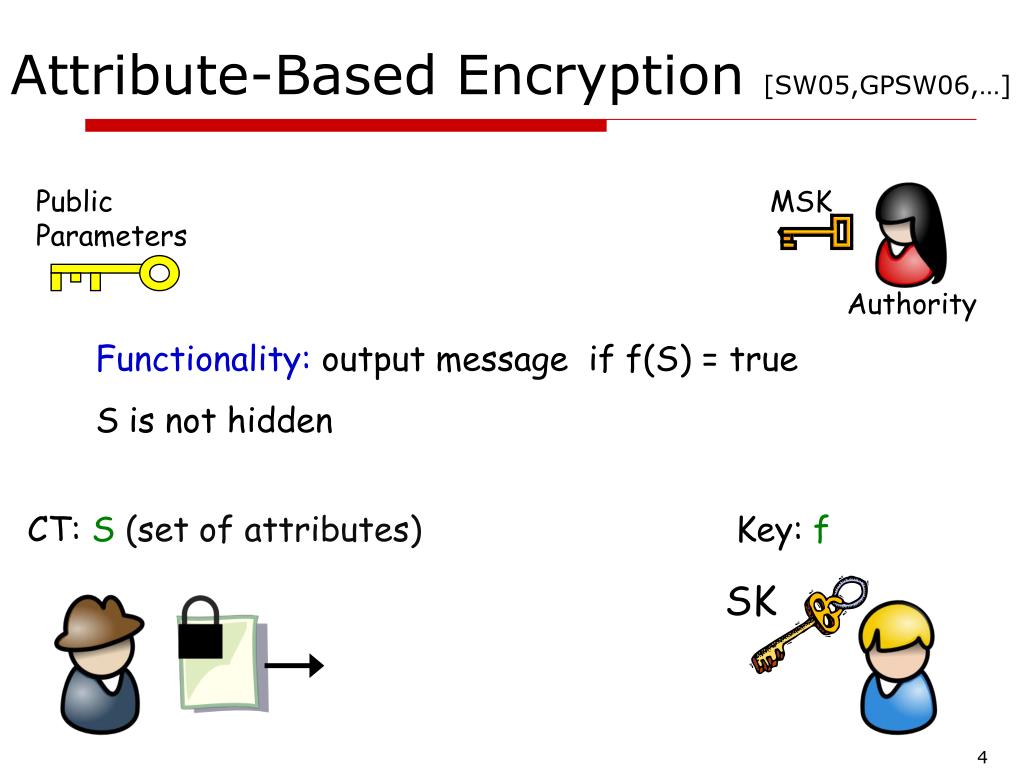
Ppt Online Offline Attribute Based Encryption Powerpoint Presentation In this paper, based on attribute based encryption (abe), we propose two private and mutual authentication protocols to protect the privacy of iot devices. the first protocol is a. Bibliographic details on multi input attribute based encryption and predicate encryption. Article "multi input attribute based encryption and predicate encryption" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). In this work, we advance this line of research by providing the first construction of multi input attribute based encryption (miabe) for the function class nc 1 for any constant arity from evasive lwe.

Multi Authorization Attribute Based Verifiable Encryption Scheme Based Article "multi input attribute based encryption and predicate encryption" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). In this work, we advance this line of research by providing the first construction of multi input attribute based encryption (miabe) for the function class nc 1 for any constant arity from evasive lwe. Constant input attribute based (and predicate) encryption from evasive and tensor lwe. shweta agrawal, mélissa rossi, anshu yadav, shota yamada. crypto 2023. attribute based multi input fe (and more) for attribute weighted sums. shweta agrawal, junichi tomida, anshu yadav. crypto 2023. In this section we introduce the notion of online offline multi input functional encryption (oo mife) and present the first oo mife construction for the bounded norm multi input inner product functionality in the private key setting. Shweta agrawal, anshu yadav, shota yamada 0001. multi input attribute based encryption and predicate encryption. iacr cryptology eprint archive, 2022:1024, 2022. [doi] authors bibtex references bibliographies reviews related. We consider a further generalization of mife, namely attribute based mife introduced by abdalla et al.[acgu20], which enables greater control on the leakage inherent by the functionality of mife, making it more suitable for practical applications.

Attribute Based Encryption With Enforceable Obligations Request Pdf Constant input attribute based (and predicate) encryption from evasive and tensor lwe. shweta agrawal, mélissa rossi, anshu yadav, shota yamada. crypto 2023. attribute based multi input fe (and more) for attribute weighted sums. shweta agrawal, junichi tomida, anshu yadav. crypto 2023. In this section we introduce the notion of online offline multi input functional encryption (oo mife) and present the first oo mife construction for the bounded norm multi input inner product functionality in the private key setting. Shweta agrawal, anshu yadav, shota yamada 0001. multi input attribute based encryption and predicate encryption. iacr cryptology eprint archive, 2022:1024, 2022. [doi] authors bibtex references bibliographies reviews related. We consider a further generalization of mife, namely attribute based mife introduced by abdalla et al.[acgu20], which enables greater control on the leakage inherent by the functionality of mife, making it more suitable for practical applications.

Pdf Efficient Revocable Multi Authority Attribute Based Encryption Shweta agrawal, anshu yadav, shota yamada 0001. multi input attribute based encryption and predicate encryption. iacr cryptology eprint archive, 2022:1024, 2022. [doi] authors bibtex references bibliographies reviews related. We consider a further generalization of mife, namely attribute based mife introduced by abdalla et al.[acgu20], which enables greater control on the leakage inherent by the functionality of mife, making it more suitable for practical applications.
Comments are closed.