Morse Code Musical Cryptography

International Morse Code What Is Cryptography Download Free Pdf What followed was a blend of digital forensics, cryptography, and audio analysis — culminating in the extraction of a hidden message buried in nostalgia and noise. the challenge began with a. Morse code in music. some examples of morse code in music from the sixties to the nineties.

Morse Code Musical Cryptography In music, morse code can be encoded in the rhythm of the music. each character may be represented in different instruments, different pitch of note, different bars, or all in a row. One unexpected form of transmitting such messages is through music. it’s better known as music cryptography, which is a method in which the musical notes a through g are used to spell out. We’ve talked about legendary encryption methods like caesar ciphers and vigenere ciphers, as well as simpler auditory ones like morse code and tap codes. we’ve seen encryptions through blinking lights, woven through crossword grids, and even knitted into scarves. I developed several units of work to go with my composition passion for symphonic winds, and this electronic version has nothing to do with that work except that that's where the interest in hiding messages in music began.
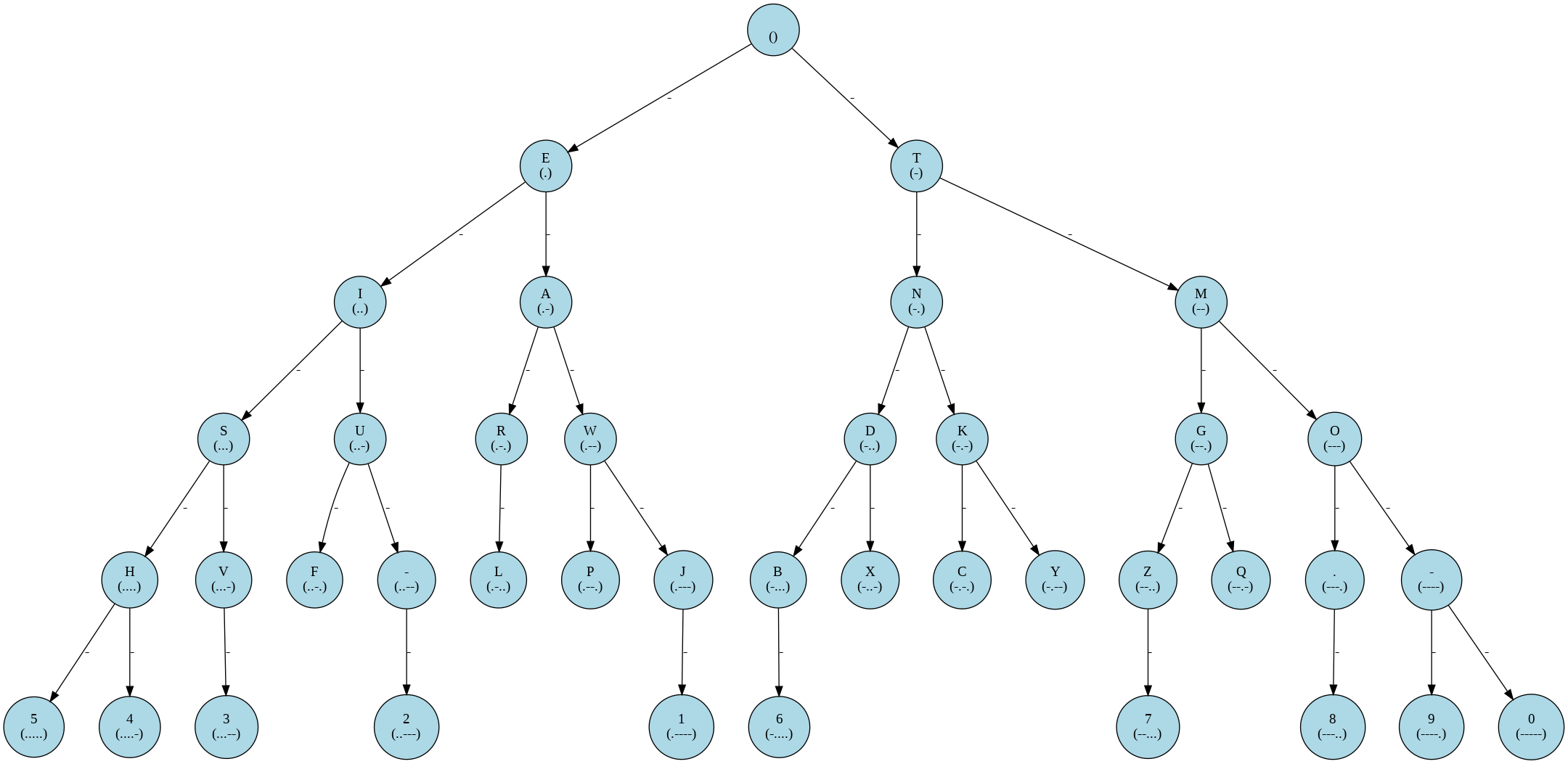
Github Jackgetdev Cryptography Morse Code For Developer We’ve talked about legendary encryption methods like caesar ciphers and vigenere ciphers, as well as simpler auditory ones like morse code and tap codes. we’ve seen encryptions through blinking lights, woven through crossword grids, and even knitted into scarves. I developed several units of work to go with my composition passion for symphonic winds, and this electronic version has nothing to do with that work except that that's where the interest in hiding messages in music began. This morse code translator article delves into the fascinating synergy between morse code in music and the creative arts. it explores how musicians and filmmakers employ this age old code to conceal messages within their works’ auditory and visual landscapes. Embracing the art of musical cryptography involves creating your own musical codes within melodies and harmonies. crafting your personal musical cipher requires a series of steps that are not only intriguing but also quite rewarding. Once data encryption key (s) are available, alice and bob can start sending encrypted messages using a stream cipher, in snoa in the snow. as they go through the ciphertexts in this dance music, they frequently lose synchronization, but they recover each time. Explores how messages can be hidden in music, from note name ciphers to steganography and musical cryptograms.
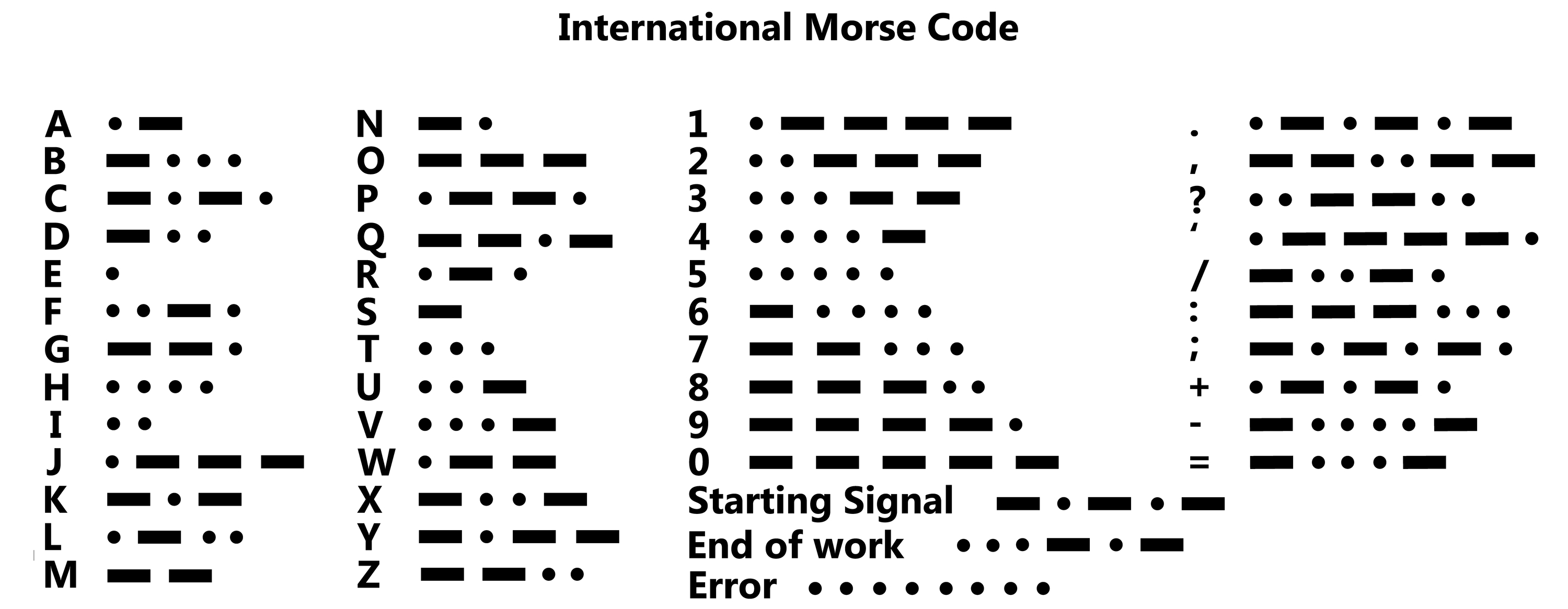
Cyber Org Practice Ctf This morse code translator article delves into the fascinating synergy between morse code in music and the creative arts. it explores how musicians and filmmakers employ this age old code to conceal messages within their works’ auditory and visual landscapes. Embracing the art of musical cryptography involves creating your own musical codes within melodies and harmonies. crafting your personal musical cipher requires a series of steps that are not only intriguing but also quite rewarding. Once data encryption key (s) are available, alice and bob can start sending encrypted messages using a stream cipher, in snoa in the snow. as they go through the ciphertexts in this dance music, they frequently lose synchronization, but they recover each time. Explores how messages can be hidden in music, from note name ciphers to steganography and musical cryptograms.

The Klein Academy For Ict 5 3 Cryptography Morse Code Once data encryption key (s) are available, alice and bob can start sending encrypted messages using a stream cipher, in snoa in the snow. as they go through the ciphertexts in this dance music, they frequently lose synchronization, but they recover each time. Explores how messages can be hidden in music, from note name ciphers to steganography and musical cryptograms.
Comments are closed.