Module 6 Ssh Key Based Authentication
Configure Ssh Key Based Authentication On Linux In this module of ssh beginners, you'll learn to set up key based authentication for a more secure and hassle free ssh access. Learn how to set up ssh key based authentication for users with ansible, including key deployment, sshd configuration, and disabling password auth.
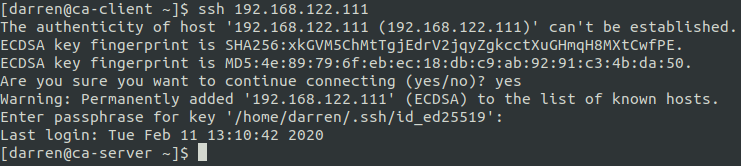
Ssh Key Based Authentication By following this step by step guide, you have successfully set up and secured ssh key based authentication for your remote server. you've generated a robust cryptographic key pair, distributed your public key, and most importantly, disabled less secure password based logins. By default ansible is able to find the default location of the rsa key pair, but you can tell ansible a custom rsa key pair location on your server by just adding the location of where to find the key such as the following example:. Implementing ssh key based authentication is a critical step in securing your linux and unix systems. by following this comprehensive guide, you’ve taken a significant step toward protecting your servers from unauthorized access and potential breaches. To be able to use ssh, scp, or sftp to connect to the server from a client machine, generate an authorization key pair by following the steps below. note that keys must be generated for each user separately.

Configure Ssh Key Based Authentication Tec Bartec Bar Implementing ssh key based authentication is a critical step in securing your linux and unix systems. by following this comprehensive guide, you’ve taken a significant step toward protecting your servers from unauthorized access and potential breaches. To be able to use ssh, scp, or sftp to connect to the server from a client machine, generate an authorization key pair by following the steps below. note that keys must be generated for each user separately. Are you tired of typing your password every time you connect to a remote server via ssh? in this guide, i'll show you how to set up ssh key based authentication, a more secure and convenient way to connect to your servers. You'll learn how to set up and configure ssh for secure, passwordless authentication using cryptographic keys. throughout this lab, you'll learn the fundamentals of ssh, including service management, key pair generation, and secure authentication configuration. My goal is to develop an ansible playbook to deploy multifactor ssh logins of the type (public key and otp) or (password and otp) on ubuntu server 18.04 hosts. i followed the guide here and it largely works. Ssh authentication uses a public–private key pair. the private key remains on the client machine and must be kept secret, while the public key is placed on the server in the ~ .ssh authorized keys file to enable authentication. ssh keys are generated using the ssh keygen utility.
Comments are closed.