Module 2dm Vulnerability Assessment

Module 5 Vulnerability Assessment Pdf Module 2 dm free download as pdf file (.pdf) or read online for free. Join us to develop the practical, analytical, and strategic skills required to secure enterprise systems through effective vulnerability assessment and management practices.

Vulnerability Assessment Section 03 Module 03 Pdf Vulnerability Dm module 2. Vulnerability assessments have not always been a part of risk assessment, but in recent times, they have become indispensable due to the recognition that disasters occur as a result of interactions between hazards and vulnerable elements. A security analyst is investigating a cyber attack that began by compromising one file system through a vulnerability in a custom software application. the attack now appears to be affecting additional file systems under the control of another security authority. Vulnerability assessment (va) is a highly specialized method of identifying security flaws in a system or programming environment. va is entirely a search and find method, intending to ensure that none of the provisos are overlooked.

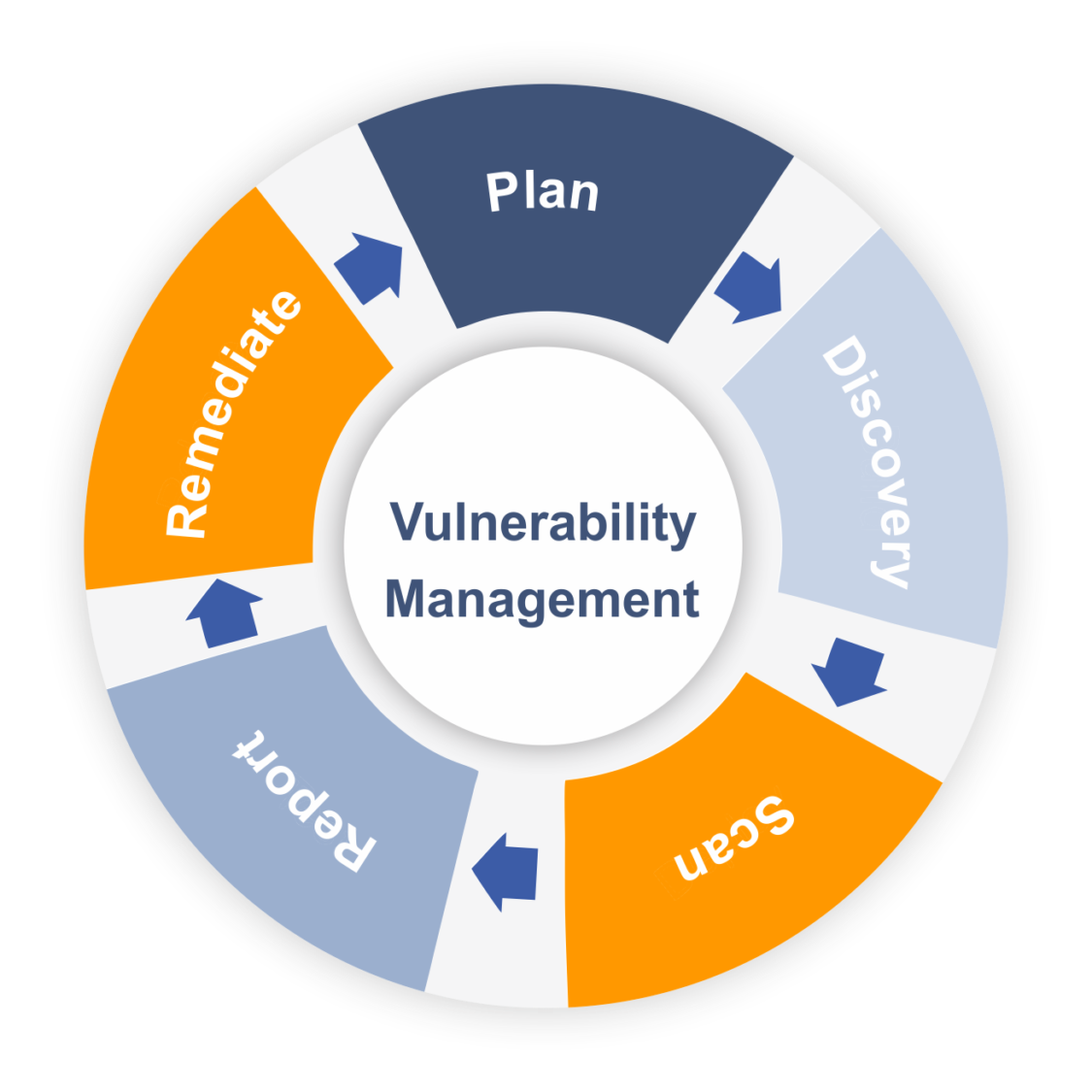
W02d2 Risk And Vulnerability Assessment Download Free Pdf Threat A security analyst is investigating a cyber attack that began by compromising one file system through a vulnerability in a custom software application. the attack now appears to be affecting additional file systems under the control of another security authority. Vulnerability assessment (va) is a highly specialized method of identifying security flaws in a system or programming environment. va is entirely a search and find method, intending to ensure that none of the provisos are overlooked. Dm module 2 free download as pdf file (.pdf), text file (.txt) or read online for free. module 2 covers hazards and vulnerability, detailing various hazard types, their mapping, and vulnerability assessments. Learn the key risk factors to consider when conducting a vulnerability assessment process. the goal of a vulnerability assessment is to prioritize high profile vulnerabilities. All components of a hazard assessment vary in space and time. as the consequences of hazards are usually large, it is prudent to include vulnerability and riskreduction strategies in the process. Microsoft defender vulnerability management uses a risk based approach to the discovery, prioritization, and remediation of endpoint vulnerabilities and misconfigurations.

Class 2 Vulnerability Management Pdf Vulnerability Computing Dm module 2 free download as pdf file (.pdf), text file (.txt) or read online for free. module 2 covers hazards and vulnerability, detailing various hazard types, their mapping, and vulnerability assessments. Learn the key risk factors to consider when conducting a vulnerability assessment process. the goal of a vulnerability assessment is to prioritize high profile vulnerabilities. All components of a hazard assessment vary in space and time. as the consequences of hazards are usually large, it is prudent to include vulnerability and riskreduction strategies in the process. Microsoft defender vulnerability management uses a risk based approach to the discovery, prioritization, and remediation of endpoint vulnerabilities and misconfigurations.

Training Module On Vulnerability Assessment Ii Pptx All components of a hazard assessment vary in space and time. as the consequences of hazards are usually large, it is prudent to include vulnerability and riskreduction strategies in the process. Microsoft defender vulnerability management uses a risk based approach to the discovery, prioritization, and remediation of endpoint vulnerabilities and misconfigurations.
Vulnerability Assessment Scanning Tools List 2018 Esecforte
Comments are closed.