Module 1 1 Introduction Creating A Stack Based Buffer Overflow Windows Exploit

The Complete Metasploit Guide For the first of this series, we gonna use cloudme sync 1.11.0 application to develop our exploit. this application is vulnerable to remote buffer overflow on port 8888. Q.how can a buffer overflow be used to control the execution flow of a program? ans a buffer overflow controls a program’s execution flow by overwriting the return address on the program’s.
What Is A Stack Overflow Error This tutorial is part one of a two part series that focuses on binary exploitation, in particular on x86 stack based windows buffer overflows. this part of the series focuses on the theory behind memory, processors and buffer overflows. In this course, windows buffer overflow walkthrough, you’ll learn to identify, exploit, and gain control over a vulnerable application. first, you’ll explore how a stack based buffer overflow occurs in an x86 process. This video is part of the course hands on fuzzing and exploit development. in this module, we'll be learning on how to exploit a stack based buffer overflow. Complete guide to windows buffer overflow exploitation using immunity debugger and mona. learn stack based buffer overflow techniques for penetration testing.
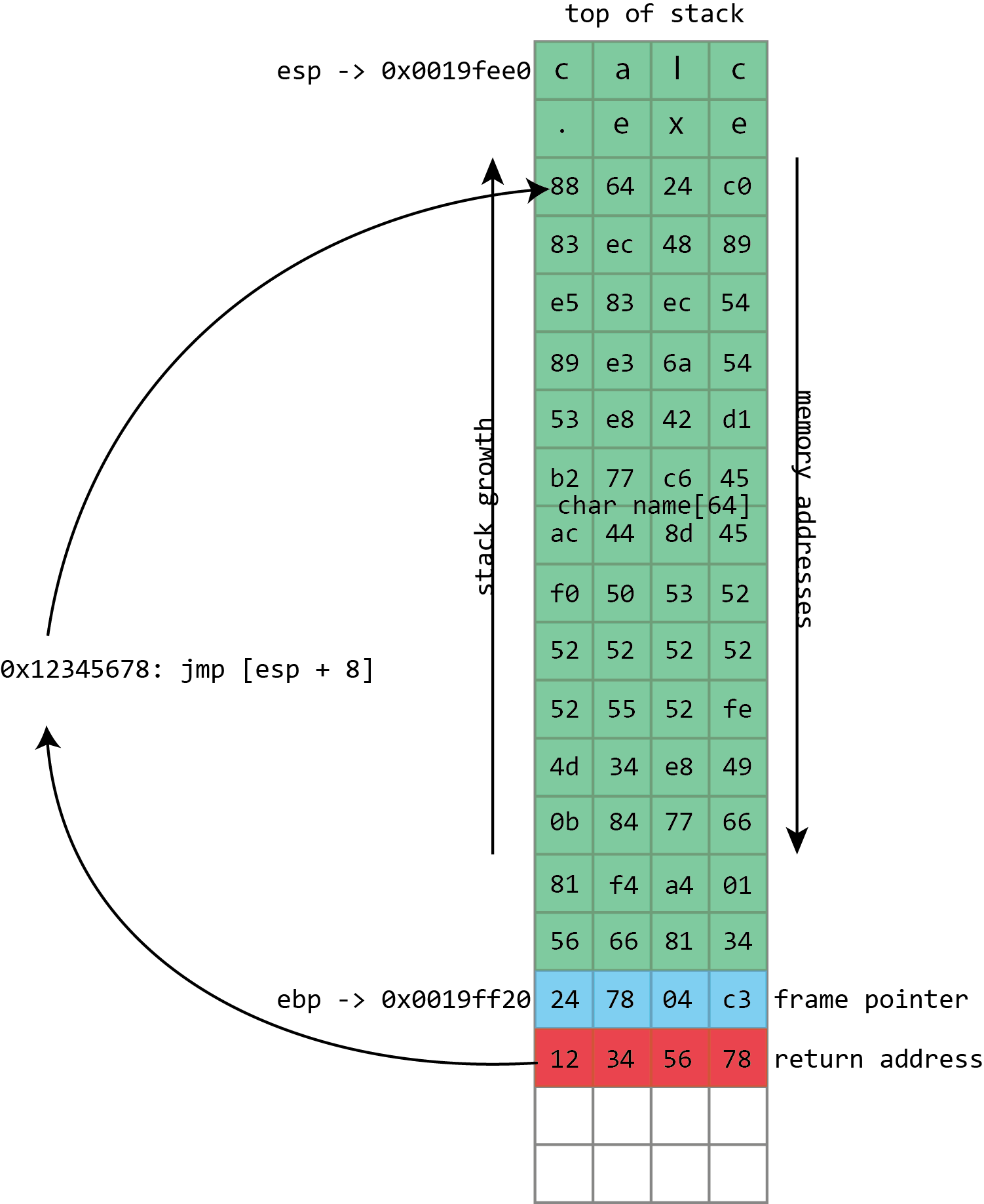
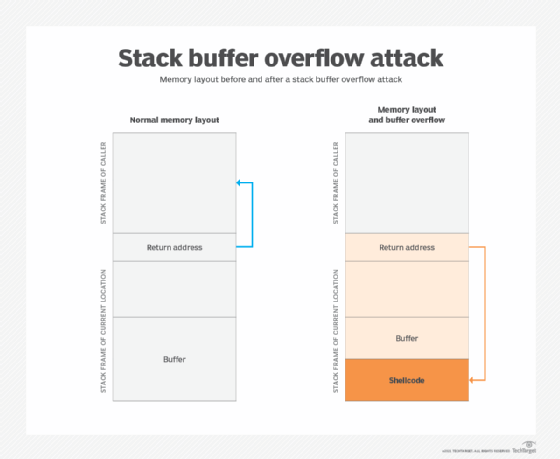
How Security Flaws Work The Buffer Overflow Ars Technica This video is part of the course hands on fuzzing and exploit development. in this module, we'll be learning on how to exploit a stack based buffer overflow. Complete guide to windows buffer overflow exploitation using immunity debugger and mona. learn stack based buffer overflow techniques for penetration testing. Lets solve a very basic stack based buffer overflow lab to learn how it occurs, how it can be exploited, and how to analyze execution flow using a debugger and python for automate exploit. This module is your first step into windows binary exploitation, and it will teach you how to exploit local and remote buffer overflow vulnerabilities on windows machines. The following article will explain in a clear hopefully way how to exploit the stack based buffer overflow for a vulnerable windows 32bit executable. In this blog, we demonstrate how to develop and execute a privilege escalation exploit on windows 11 24h2 using a custom vulnerable driver and token stealing shellcode. at its core, a buffer overflow happens when a program writes more data to a buffer than it can hold.
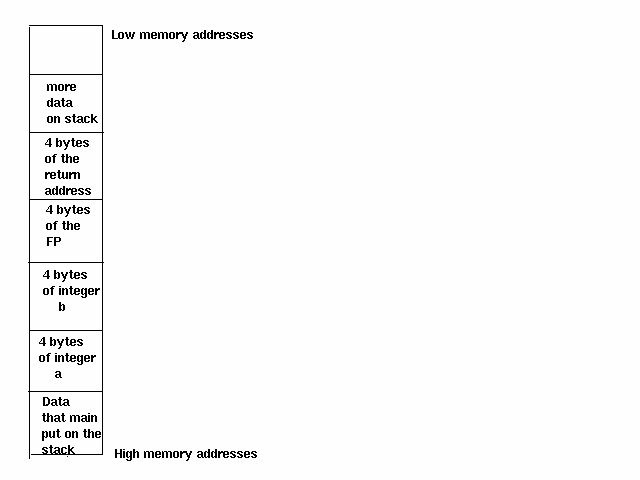
A Look At The Buffer Overflow Hack Linux Journal Lets solve a very basic stack based buffer overflow lab to learn how it occurs, how it can be exploited, and how to analyze execution flow using a debugger and python for automate exploit. This module is your first step into windows binary exploitation, and it will teach you how to exploit local and remote buffer overflow vulnerabilities on windows machines. The following article will explain in a clear hopefully way how to exploit the stack based buffer overflow for a vulnerable windows 32bit executable. In this blog, we demonstrate how to develop and execute a privilege escalation exploit on windows 11 24h2 using a custom vulnerable driver and token stealing shellcode. at its core, a buffer overflow happens when a program writes more data to a buffer than it can hold.
Comments are closed.