Modern Windows Binary Patch Diffing

Modern Binary Patch Diffing R Blueteamsec There was a recent systematic analysis of modern binary diffing tools comparing over 61 tools and providing considerable insight on binary diffing. the analysis of the 61 binary diffing tools compared matching heuristics, speed, and several other features of the tools. In this video we look at some of the most effective ways to examine a microsoft security patch to identify the vulnerability being corrected.
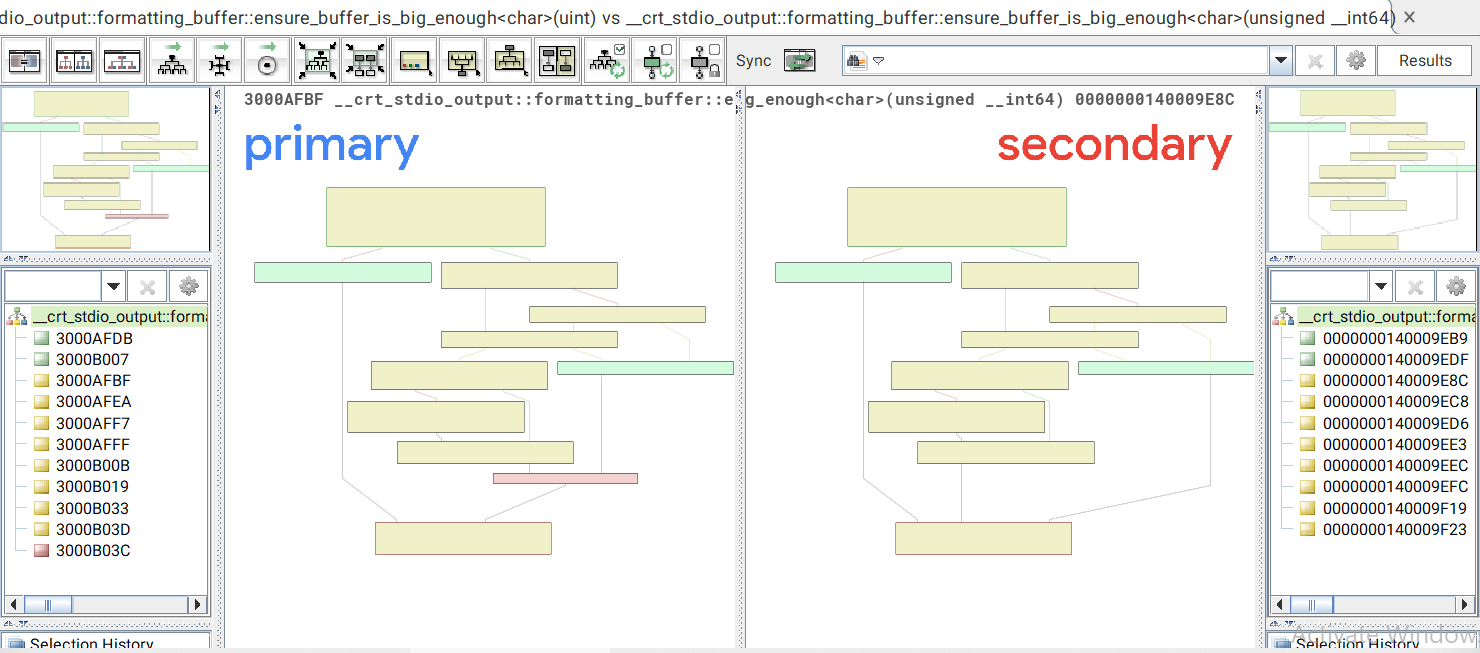
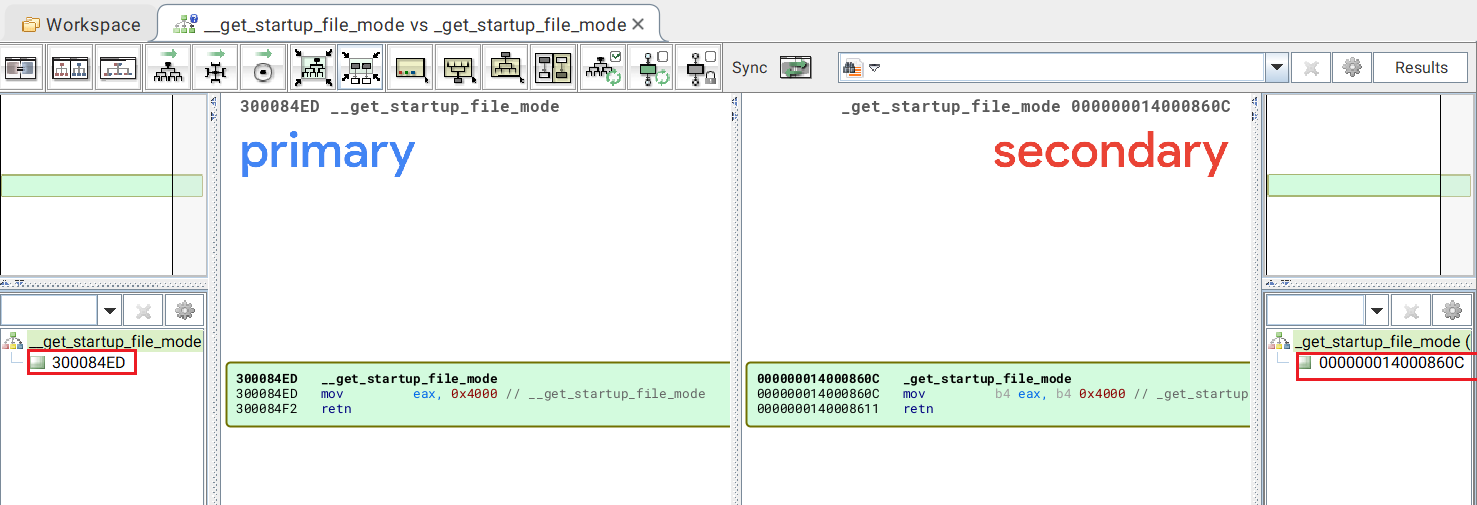
Windows Patch Diffing With Ghidra And Bindiff Rick S Blog Deepdiff represents a major leap forward in security analysis. it helps security researchers, reverse engineers, and development teams to pinpoint vulnerable functions and generate precise diffing views across binary files with unmatched accuracy. Diffrays is a research oriented tool for binary patch diffing, designed to aid in vulnerability research, exploit development, and reverse engineering. it leverages ida pro and the ida domain api to extract pseudocode of functions and perform structured diffing between patched and unpatched binaries. You'll learn a step by step approach to modern patch diffing, including best practices, common pitfalls to avoid, and useful scripts to enhance your workflow. Learn to leverage modern sre platforms and patch diffing methodologies to identify security critical code changes and uncover vulnerabilities in windows binaries.
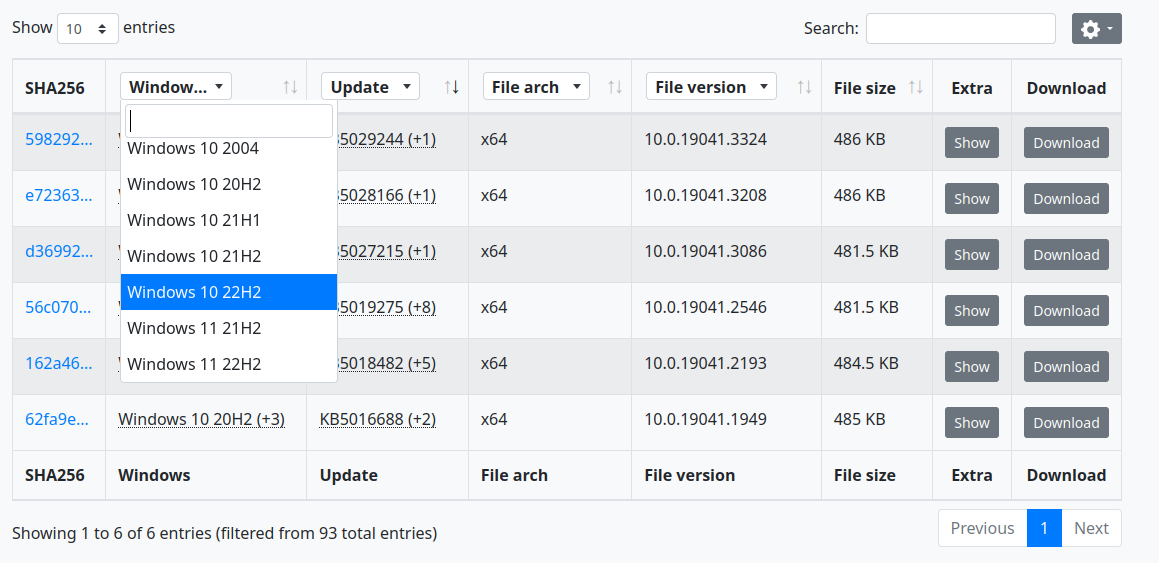
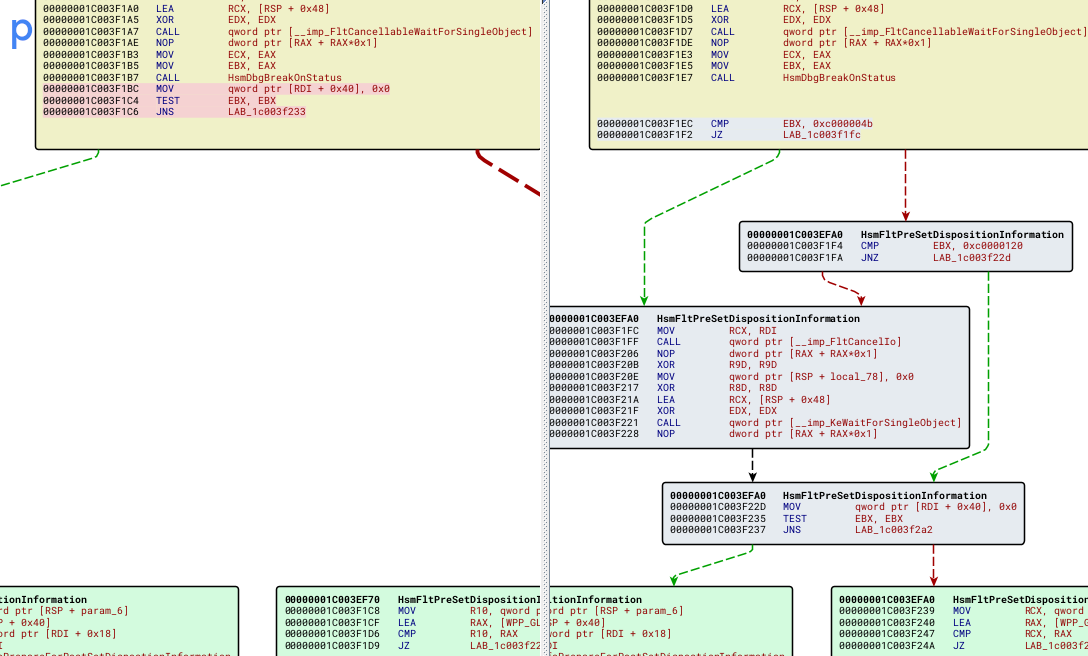
Windows Patch Diffing With Ghidra And Bindiff Rick S Blog You'll learn a step by step approach to modern patch diffing, including best practices, common pitfalls to avoid, and useful scripts to enhance your workflow. Learn to leverage modern sre platforms and patch diffing methodologies to identify security critical code changes and uncover vulnerabilities in windows binaries. Patch diffing remains a critical skill in cybersecurity, allowing researchers to identify vulnerabilities by comparing patched and unpatched software versions. in 2025, tools like bindiff and diaphora continue to evolve, now incorporating ai to enhance efficiency. The short topical lessons and hands on exercises will have you patch diffing recent cves and their corresponding binaries across on the windows platform. you will learn about best practices, how to avoid patch diffing pitfalls, and get useful scripts to enhance your analysis workflow. After looking for recently patched vulnerabilities, i wasn't able to find anything that fit the bill and seemed to match my skill level. the recent interesting bugs didn't seem to have any available pocs or analysis info online. This case study shows how patch diffing was used to analyze a vulnerability in the windows esp protocol. the analysis revealed an error in the handling of fragmented esp packets that could lead to remote code execution.
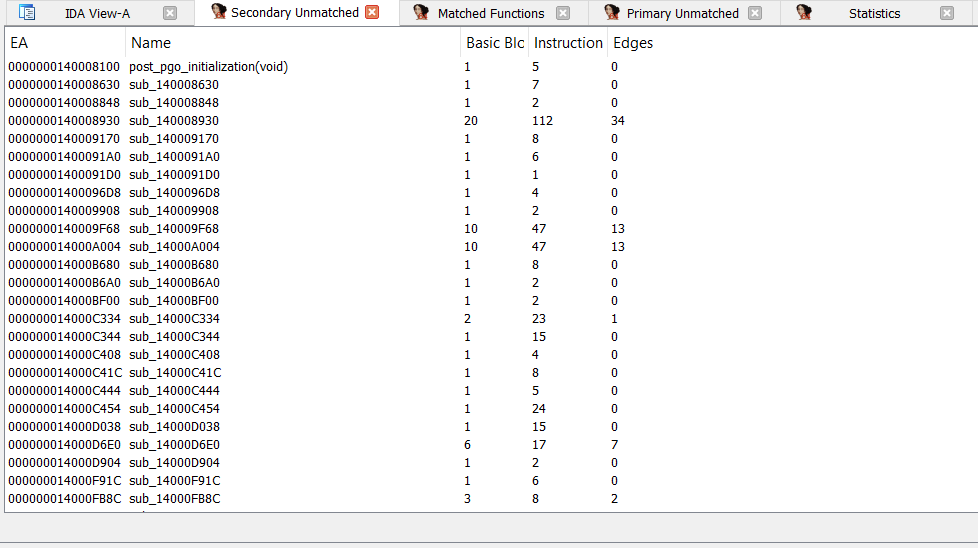
Binary Diffing Haiddy Patch diffing remains a critical skill in cybersecurity, allowing researchers to identify vulnerabilities by comparing patched and unpatched software versions. in 2025, tools like bindiff and diaphora continue to evolve, now incorporating ai to enhance efficiency. The short topical lessons and hands on exercises will have you patch diffing recent cves and their corresponding binaries across on the windows platform. you will learn about best practices, how to avoid patch diffing pitfalls, and get useful scripts to enhance your analysis workflow. After looking for recently patched vulnerabilities, i wasn't able to find anything that fit the bill and seemed to match my skill level. the recent interesting bugs didn't seem to have any available pocs or analysis info online. This case study shows how patch diffing was used to analyze a vulnerability in the windows esp protocol. the analysis revealed an error in the handling of fragmented esp packets that could lead to remote code execution.
Binary Diffing Haiddy After looking for recently patched vulnerabilities, i wasn't able to find anything that fit the bill and seemed to match my skill level. the recent interesting bugs didn't seem to have any available pocs or analysis info online. This case study shows how patch diffing was used to analyze a vulnerability in the windows esp protocol. the analysis revealed an error in the handling of fragmented esp packets that could lead to remote code execution.
Binary Diffing Haiddy
Comments are closed.