Mitigating Data Breaches With Osint Authentic8

Mitigating Data Breaches With Osint Authentic8 This post will explain how osint can be used to discover breached and leaked data online. however, before we begin, it is worth differentiating between the terms "data breach" and "data leak.". My osint articles & guides authentic8 how osint strengthens corporate security and proactively reduces risk powering global security operations centers with osint capabilities ai driven osint threat hunting: how ai is transforming cyber defense investigating on bluesky osint for border security: how analysts can deploy open source techniques.

Mitigating Data Breaches With Osint Authentic8 In this blog, our partners from authentic8 discuss the importance of anonymity and obfuscation within osint investigations. Osint academy is delivered within silo, authentic8’s web isolation platform, and designed to educate and improve the efficacy of internet focused research teams. Page topic: "21 osint research tools for threat intelligence authentic8". created by: norman graves. language: english. Authentic8 is a web isolation platform. silo for research (toolbox) provides osint investigations & cyber threat analysis capabilities for the public sector.
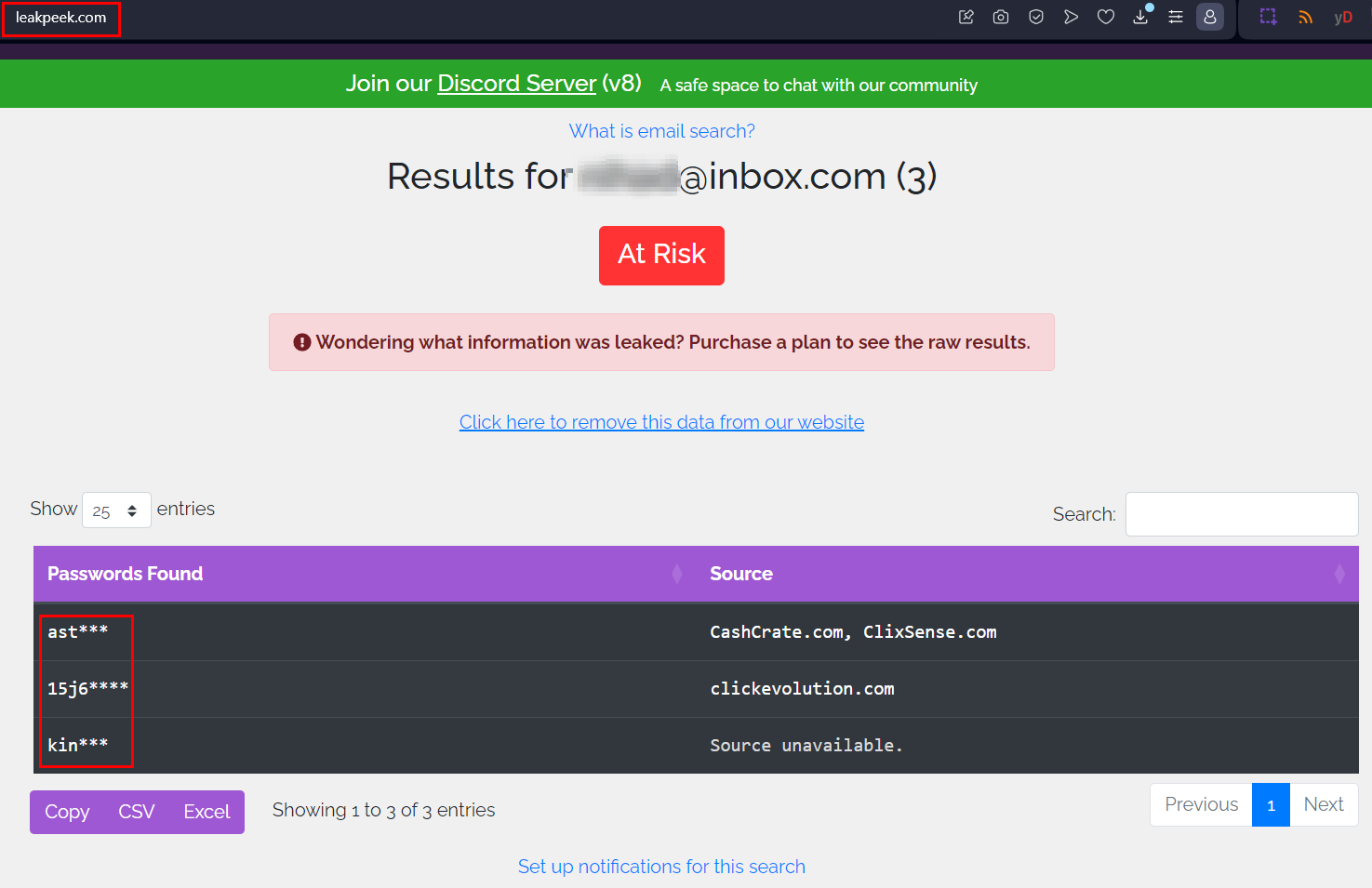
Mitigating Data Breaches With Osint Authentic8 Page topic: "21 osint research tools for threat intelligence authentic8". created by: norman graves. language: english. Authentic8 is a web isolation platform. silo for research (toolbox) provides osint investigations & cyber threat analysis capabilities for the public sector. Osint academy is delivered within silo, authentic8's web isolation platform, and designed to educate and improve the efficacy of internet focused research teams. Read authentic8's blog to gain insight from our experts on osint investigations, cybersecurity intelligence, protecting sensitive data and secure web browsing. Learn how osint helps corporate security teams identify threats, protect brands, prevent fraud, and act before attackers exploit public data. Mitigating data breaches with osint techniques: osint is an indispensable tool to identify weaknesses within your organization to mitigate data breaches and uncover leaked data before bad actors do.
.png)
Mitigating Data Breaches With Osint Authentic8 Osint academy is delivered within silo, authentic8's web isolation platform, and designed to educate and improve the efficacy of internet focused research teams. Read authentic8's blog to gain insight from our experts on osint investigations, cybersecurity intelligence, protecting sensitive data and secure web browsing. Learn how osint helps corporate security teams identify threats, protect brands, prevent fraud, and act before attackers exploit public data. Mitigating data breaches with osint techniques: osint is an indispensable tool to identify weaknesses within your organization to mitigate data breaches and uncover leaked data before bad actors do.
.png)
Mitigating Data Breaches With Osint Authentic8 Learn how osint helps corporate security teams identify threats, protect brands, prevent fraud, and act before attackers exploit public data. Mitigating data breaches with osint techniques: osint is an indispensable tool to identify weaknesses within your organization to mitigate data breaches and uncover leaked data before bad actors do.
Comments are closed.