Misconceptions About The Purdue Model For Network Segmentation
Purdue Model Segmentation Details Techyengineer Depending solely on a 30 year old manufacturing model without properly understanding iec 62443’s zones and conduits concepts is risky. this analysis will clarify three key misconceptions about the purdue model and present the correct application directions for modern industrial environments. There has been a growing narrative in recent years that the purdue model is outdated. in reality, the purdue model is not obsolete.
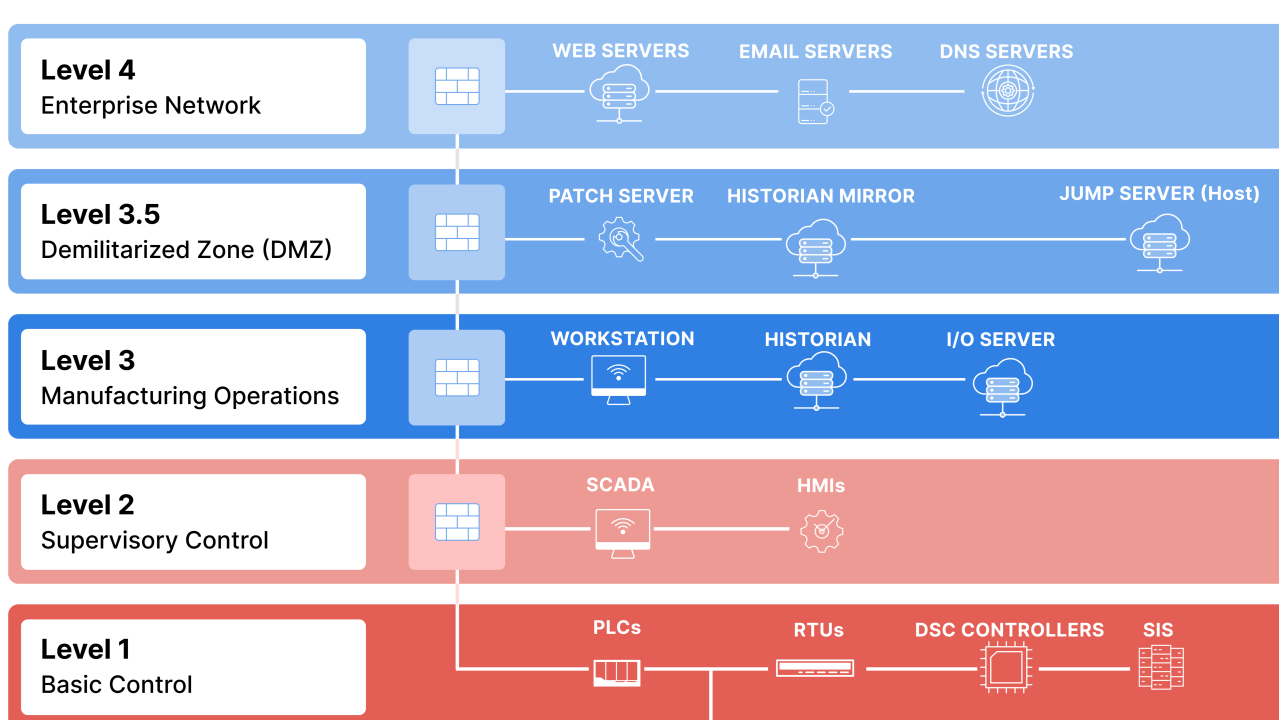
Purdue Model For Ics Security Segmentation Emberot This article gives you a practical, modern blueprint: what to keep from purdue, what to update, and how to implement segmentation, data flows, remote access, and cloud connectivity with resilience first design. The purdue model segments the industrial networks into levels but air gaps are fiction, and level 2 hmis are where attackers pivot from it to ot. know your architecture, because attackers. Network segmentation is fundamental to ics security and the purdue model creates distinct security zones within the ics environment. this approach provides a defense in depth strategy, limiting the impact of a breach, and hindering the lateral movement of attackers within the network. To mitigate the risk of an attacker gaining unfettered access to the network from a single point of entry, audit your network segmentation regularly to ensure you have the proper it ot segmentation. this process can be a drawn out and costly endeavor.
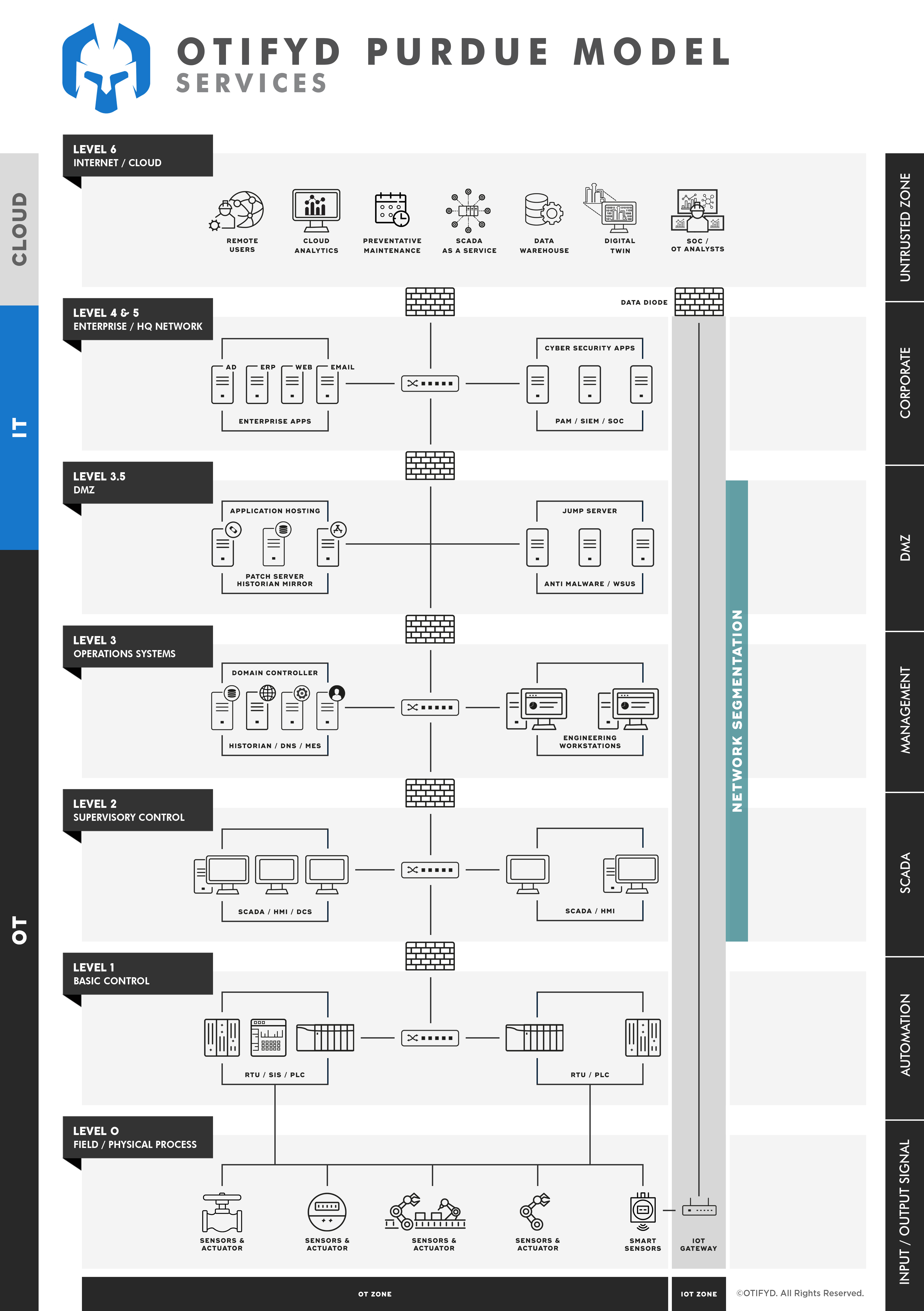
Network Segmentation Otifyd Safeguarding Ot Networks Network segmentation is fundamental to ics security and the purdue model creates distinct security zones within the ics environment. this approach provides a defense in depth strategy, limiting the impact of a breach, and hindering the lateral movement of attackers within the network. To mitigate the risk of an attacker gaining unfettered access to the network from a single point of entry, audit your network segmentation regularly to ensure you have the proper it ot segmentation. this process can be a drawn out and costly endeavor. In this blog post, we will debunk these misconceptions and emphasize the importance of understanding the true value and limitations of the purdue model in ensuring ot security. While the purdue model cannot solve all challenges outright, its emphasis on network segmentation and controlled interactions can offer a starting point for designing an effective ics security strategy. Improving ot segmentation isn't about discarding purdue or redrawing the whole architecture. it starts with recognizing that hierarchy alone does not deliver security and aligning your design with iec 62443 principles. Misconceptions about the purdue model for network segmentation otbase ot asset inventory software 4.62k subscribers subscribe.
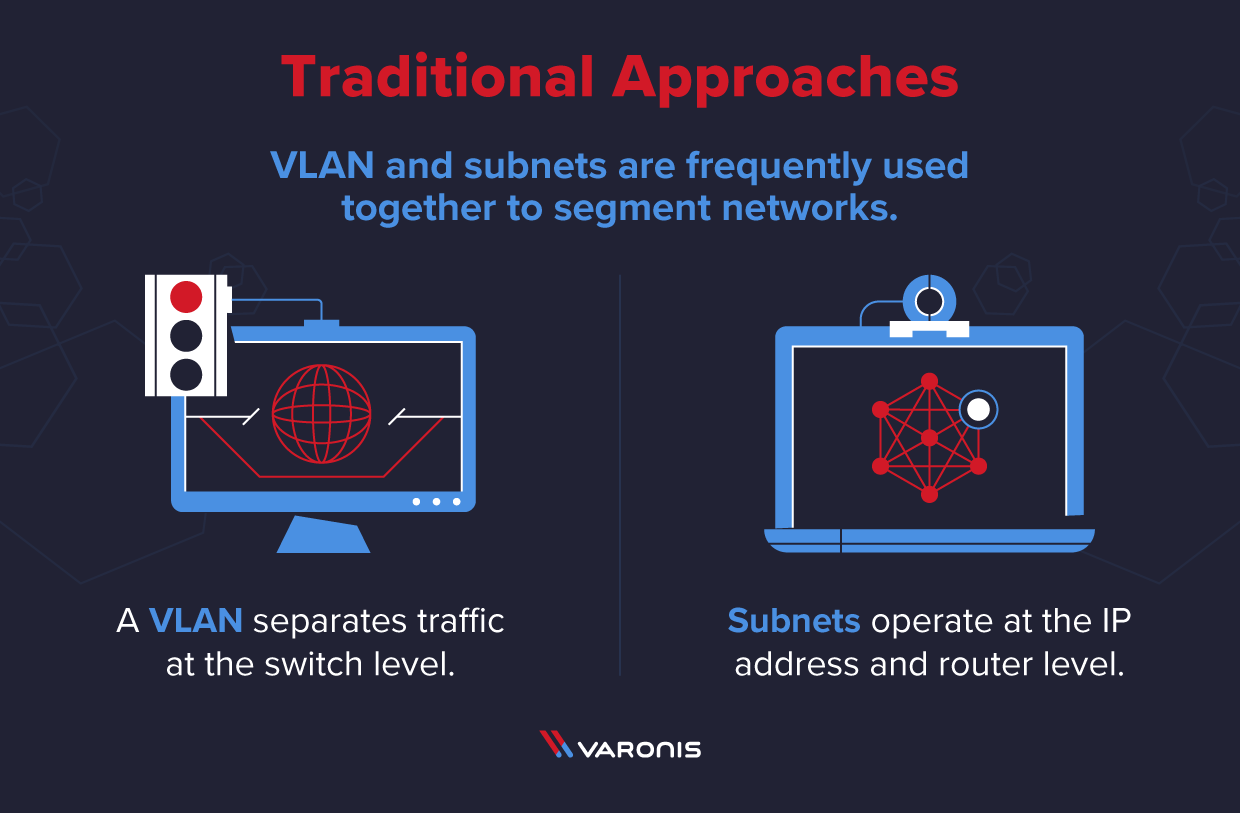
What Is Network Segmentation In this blog post, we will debunk these misconceptions and emphasize the importance of understanding the true value and limitations of the purdue model in ensuring ot security. While the purdue model cannot solve all challenges outright, its emphasis on network segmentation and controlled interactions can offer a starting point for designing an effective ics security strategy. Improving ot segmentation isn't about discarding purdue or redrawing the whole architecture. it starts with recognizing that hierarchy alone does not deliver security and aligning your design with iec 62443 principles. Misconceptions about the purdue model for network segmentation otbase ot asset inventory software 4.62k subscribers subscribe.
What Is Network Segmentation Improving ot segmentation isn't about discarding purdue or redrawing the whole architecture. it starts with recognizing that hierarchy alone does not deliver security and aligning your design with iec 62443 principles. Misconceptions about the purdue model for network segmentation otbase ot asset inventory software 4.62k subscribers subscribe.
Comments are closed.